The Dark Side Of Technology: How Hackers Are Exploiting Jeffrey Epstein's Legacy
Have you ever wondered how the digital age has transformed the way criminal networks operate? When we think about Jeffrey Epstein and his infamous crimes, most people focus on the legal and social aspects. But what about the digital dimension? How have hackers been exploiting Epstein's legacy in the years following his death? This article delves into the murky world where technology, crime, and the Epstein scandal intersect.
The Digital Footprint of Jeffrey Epstein
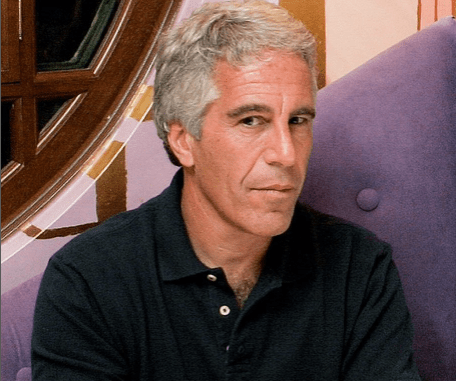
Jeffrey Epstein, a financier and convicted sex offender, left behind a complex web of connections, secrets, and digital footprints. His death in 2019 only intensified public interest in his life and the people associated with him. But what many don't realize is how this interest has created a breeding ground for cybercriminals.
The Rise of Digital Exploitation
In the wake of Epstein's death, hackers have found new ways to exploit his legacy. From phishing scams using his name to sophisticated cyber attacks targeting those connected to him, the digital exploitation of the Epstein case has become a significant concern. But how exactly are these hackers operating?
Biography of Jeffrey Epstein
Jeffrey Edward Epstein was born on January 20, 1953, in Brooklyn, New York. He began his career as a teacher before moving into finance, where he eventually became a successful financier and registered sex offender.
Personal Details and Bio Data
| Category | Details |
|---|---|
| Full Name | Jeffrey Edward Epstein |
| Date of Birth | January 20, 1953 |
| Place of Birth | Brooklyn, New York |
| Date of Death | August 10, 2019 |
| Education | Cooper Union, Courant Institute of Mathematical Sciences |
| Occupation | Financier, Registered Sex Offender |
| Net Worth | Estimated $500 million - $1 billion |
| Known For | Financial crimes, Sex trafficking |
How Hackers Are Exploiting the Epstein Scandal
Phishing and Social Engineering Tactics
One of the primary ways hackers have been exploiting the Epstein scandal is through sophisticated phishing campaigns. These campaigns often use the names of high-profile individuals connected to Epstein to lure victims into clicking malicious links or providing sensitive information.
For example, emails claiming to be from lawyers handling Epstein's estate or journalists investigating the case have been used to trick people into revealing personal data. These phishing attempts are particularly effective because they prey on people's curiosity about the Epstein case and their desire for insider information.
Data Breaches and Information Theft
Another concerning trend is the increase in data breaches targeting individuals and organizations connected to Epstein. Hackers have been attempting to access private communications, financial records, and other sensitive information that could shed light on Epstein's network or be used for blackmail.
These breaches have affected not only the rich and famous but also ordinary people who may have had peripheral connections to Epstein's world. The stolen data can then be sold on the dark web or used for various criminal purposes.
The Role of Social Media in Spreading Misinformation
Fake News and Conspiracy Theories
Social media platforms have become breeding grounds for misinformation related to Jeffrey Epstein. Hackers and bad actors have been using these platforms to spread fake news, conspiracy theories, and malicious content related to the case.
This misinformation serves multiple purposes: it can be used to manipulate public opinion, discredit legitimate investigations, or simply create chaos and confusion. The viral nature of social media makes it an ideal tool for those looking to exploit the Epstein scandal for their own gain.
Deepfakes and Digital Manipulation
One of the more disturbing trends is the use of deepfake technology to create fake videos or audio recordings related to Jeffrey Epstein. These deepfakes can be used to spread false information, create scandals, or even blackmail individuals.
For instance, there have been attempts to create fake videos of Epstein making incriminating statements or of other individuals discussing their connections to him. These videos, while clearly fake to experts, can be convincing enough to fool the general public and cause significant damage.
Cybersecurity Measures and Prevention
Protecting Yourself from Epstein-Related Scams
Given the prevalence of Epstein-related scams, it's crucial to know how to protect yourself. Here are some practical steps you can take:
- Be skeptical of unsolicited emails or messages claiming to have information about Epstein or his associates.
- Verify the source of any information before believing or sharing it.
- Use strong, unique passwords for all your accounts and enable two-factor authentication where possible.
- Keep your software and security systems up to date to protect against the latest threats.
- Be cautious when clicking on links or downloading attachments, especially from unknown sources.
The Role of Law Enforcement and Cybersecurity Firms
Law enforcement agencies and cybersecurity firms have been working tirelessly to combat the exploitation of the Epstein scandal. This includes tracking down and prosecuting hackers, shutting down malicious websites, and educating the public about online threats.
However, the anonymous nature of the internet and the global reach of these crimes make it challenging to completely eliminate the problem. It's a constant game of cat and mouse between cybercriminals and those trying to stop them.
The Broader Implications of Digital Exploitation
The Erosion of Privacy in the Digital Age
The exploitation of the Epstein scandal is just one example of how the digital age has eroded privacy and security. As more of our lives move online, we become increasingly vulnerable to various forms of exploitation and manipulation.
This trend raises important questions about digital privacy, the role of technology companies in protecting users, and the need for stronger cybersecurity measures at both individual and institutional levels.
The Future of Cybercrime and Online Exploitation
As technology continues to evolve, so too will the methods used by hackers to exploit scandals and high-profile cases. We can expect to see more sophisticated phishing attempts, more convincing deepfakes, and new forms of cybercrime that we haven't even imagined yet.
This underscores the need for ongoing education about cybersecurity, the development of new protective technologies, and a broader societal discussion about the balance between connectivity and privacy.
Conclusion
The exploitation of Jeffrey Epstein's legacy by hackers is a stark reminder of the dark side of our digital age. From phishing scams to deepfakes, cybercriminals have found numerous ways to profit from public interest in the case. As we move forward, it's crucial that we remain vigilant, educate ourselves about online threats, and work together to create a safer digital environment.
The Epstein case may have captured headlines for its shocking revelations, but the digital exploitation that has followed is equally concerning. By understanding these threats and taking appropriate precautions, we can protect ourselves and others from falling victim to these malicious schemes. The fight against cybercrime is ongoing, and it's one that requires constant attention and adaptation in our ever-evolving digital landscape.