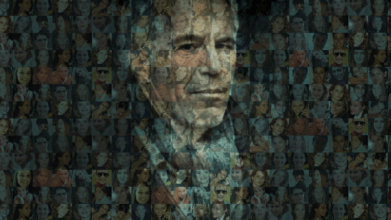
Decoding The Jeffrey Epstein Code: Unraveling The Complex Web Of Power And Influence
Have you ever wondered how a convicted sex offender managed to maintain connections with presidents, billionaires, and royalty? The Jeffrey Epstein code represents far more than just a single criminal case—it's a complex system of power, manipulation, and elite networking that continues to fascinate and horrify the public. This article delves deep into the mechanisms that allowed Epstein to operate for so long, examining the intricate patterns of influence that protected him and the shocking revelations that emerged after his death.
Biography of Jeffrey Epstein
Jeffrey Edward Epstein was born on January 20, 1953, in Brooklyn, New York. Raised in a working-class family, he demonstrated exceptional mathematical abilities from an early age. Epstein attended Lafayette High School in Brooklyn before briefly attending Cooper Union in New York City, though he eventually graduated from college in 1974.
His early career began as a teacher at the Dalton School in Manhattan, where he caught the attention of investment banker Alan Greenberg, chairman of Bear Stearns. This connection would prove pivotal in launching Epstein's career in finance, despite his lack of formal training in the field.
- Annamalai Ips Wife Akila S Nathan
- Xxl 2024
- What Happened To Jessica Tarlov
- Gore Center Where The Living
Epstein quickly rose through the ranks at Bear Stearns, becoming a partner within four years. However, his tenure was short-lived, and in 1981 he left to establish his own financial management firm. This move would set the stage for his later activities and the development of what many now refer to as the "Jeffrey Epstein code."
Personal Details and Bio Data
| Detail | Information |
|---|---|
| Full Name | Jeffrey Edward Epstein |
| Date of Birth | January 20, 1953 |
| Place of Birth | Brooklyn, New York |
| Education | Cooper Union (briefly), New York University (B.A.) |
| Career | Finance, Investment Management, Consulting |
| Known For | Sex trafficking, Elite Networking, Financial Management |
| Date of Death | August 10, 2019 |
| Place of Death | Metropolitan Correctional Center, New York City |
The Architecture of the Jeffrey Epstein Code
The Jeffrey Epstein code wasn't a literal programming language or secret cipher, but rather a sophisticated system of social engineering, financial manipulation, and network building that enabled Epstein to operate with impunity for decades. Understanding this architecture requires examining multiple interconnected components.
Financial Manipulation and Money Laundering
At the core of the Epstein code was his ability to manage vast sums of money for wealthy clients while maintaining an air of exclusivity and mystery around his investment strategies. Epstein claimed to use a "value investment approach" but provided little concrete information about his methods. This opacity served multiple purposes:
- It created an aura of exclusivity that attracted high-net-worth individuals
- It made it difficult for clients to verify his claims or track their investments
- It provided cover for potentially illegal financial activities
The complexity of his financial operations made it challenging for authorities to investigate his activities, as traditional auditing methods proved insufficient to unravel his web of shell companies and offshore accounts.
Social Engineering and Network Building
Perhaps the most crucial aspect of the Jeffrey Epstein code was his mastery of social engineering. Epstein understood that access to power was more valuable than money itself. He cultivated relationships with:
- Politicians and government officials
- Business tycoons and financial leaders
- Academics and scientists
- Celebrities and cultural figures
- Royalty and international elites
By strategically placing these individuals in his social orbit, Epstein created a protective shield around himself. Many of these connections were genuine friendships, while others were carefully cultivated for strategic purposes.
The Recruitment and Grooming System
Central to the Epstein code was his systematic approach to recruiting and grooming victims. This process involved:
- Targeting vulnerable individuals: Often young women from disadvantaged backgrounds
- Building trust: Through promises of modeling careers, education, or financial opportunities
- Gradual escalation: Slowly introducing more exploitative elements
- Creating dependency: Through financial incentives, gifts, or emotional manipulation
- Expanding the network: Encouraging victims to recruit others, creating a pyramid scheme of exploitation
This systematic approach allowed Epstein to maintain a steady supply of victims while minimizing the risk of exposure.
The Power Dynamics Behind the Code
The Jeffrey Epstein code operated within a framework of power dynamics that protected him for years. Understanding these dynamics is crucial to comprehending how such a system could exist.
Elite Protection Networks
One of the most disturbing aspects of the Epstein case is the apparent willingness of powerful individuals to protect him. This protection manifested in several ways:
- Legal maneuvering: Epstein's 2008 plea deal, negotiated by Alexander Acosta (who later became Trump's Labor Secretary), has been widely criticized as extraordinarily lenient
- Media complicity: For years, major media outlets were reluctant to investigate Epstein's activities despite mounting evidence
- Political connections: Epstein's relationships with both Democratic and Republican figures created bipartisan protection
The existence of these protection networks suggests that the Jeffrey Epstein code was embedded within broader systems of power and influence that extend far beyond a single individual.
The Role of Compromised Information
Many theories about the Epstein code suggest that he used his access to victims and his recording capabilities to gather compromising information on powerful individuals. This information could then be used for:
- Blackmail and coercion: Forcing influential people to protect him or provide favors
- Insurance policy: Ensuring his own protection by threatening to expose others
- Political leverage: Gaining influence over policy decisions or investigations
While the extent of Epstein's alleged blackmail operations remains unclear, the possibility that he was gathering such information adds another layer of complexity to the code.
The Collapse of the System
The Jeffrey Epstein code began to unravel in 2019, leading to his arrest and subsequent death in custody. Several factors contributed to this collapse:
Investigative Journalism and Whistleblowers
The Miami Herald's "Perversion of Justice" series, published in November 2018, reignited public interest in Epstein's case and exposed the inadequacies of his previous legal proceedings. This investigative work, combined with testimony from victims and whistleblowers, created momentum for renewed investigations.
Social Media and Information Sharing
The rise of social media platforms allowed for the rapid dissemination of information about Epstein's activities. Online communities dedicated to investigating the case grew, sharing documents, testimonies, and theories that kept public pressure on authorities.
Changing Social Attitudes
The #MeToo movement and increased awareness of sexual exploitation created a cultural shift that made it more difficult for powerful individuals to shield themselves from accusations. This changing climate contributed to the willingness of victims to come forward and the public's receptiveness to their stories.
The Legacy and Ongoing Investigations
Even after Epstein's death, the ramifications of his code continue to unfold. Multiple investigations and legal proceedings are ongoing:
Civil Lawsuits and Victim Compensation
Hundreds of victims have filed civil lawsuits against Epstein's estate and those who allegedly facilitated his crimes. These cases are slowly working through the courts, with some victims already receiving compensation from a fund established by Epstein's estate.
Criminal Investigations of Accomplices
Authorities have launched investigations into individuals who may have assisted Epstein in his crimes. Notable figures under scrutiny include:
- Ghislaine Maxwell, Epstein's longtime associate, who was convicted in 2021
- Jean-Luc Brunel, a modeling agent connected to Epstein who died in custody in 2022
- Various pilots, schedulers, and other associates who allegedly helped facilitate his activities
Policy and Legal Reforms
The Epstein case has prompted calls for legal reforms, particularly regarding:
- Non-prosecution agreements: Greater oversight of deals that prevent victims from speaking out
- Financial transparency: Enhanced regulations for hedge funds and private investment vehicles
- Victim protection: Improved support systems for those coming forward with abuse allegations
Understanding the Broader Implications
The Jeffrey Epstein code represents more than just a single criminal case—it's a window into how power, privilege, and corruption can intersect to create systems of exploitation. Several broader implications emerge from this case:
The Vulnerability of Justice Systems
The apparent ease with which Epstein manipulated legal systems raises serious questions about the vulnerability of justice to wealth and influence. This vulnerability extends beyond Epstein to suggest systemic issues in how the powerful are held accountable.
The Role of Networks in Enabling Crime
The Epstein case demonstrates how criminal enterprises can thrive when embedded within legitimate networks of power. Understanding these network dynamics is crucial for preventing similar situations in the future.
The Importance of Investigative Persistence
The eventual exposure of Epstein's crimes underscores the importance of persistent investigative journalism and the willingness of victims to come forward despite potential risks. These factors proved essential in breaking through the protective layers of the Epstein code.
Conclusion: Breaking the Code
The Jeffrey Epstein code was a complex system of exploitation, manipulation, and protection that operated for decades before finally collapsing. Its unraveling has revealed uncomfortable truths about power, privilege, and the vulnerabilities in our systems of justice and accountability.
As investigations continue and more details emerge, it's clear that fully understanding and addressing the implications of the Epstein case will require sustained effort from journalists, law enforcement, policymakers, and the public. The code may have been broken, but its legacy continues to influence discussions about power, accountability, and justice.
Moving forward, the challenge is to ensure that the systems that protected Epstein are reformed and that similar codes of silence and protection cannot develop in the future. Only by confronting these uncomfortable realities can we hope to prevent such exploitation from occurring again.
The Jeffrey Epstein code serves as a stark reminder that in the shadows of power and privilege, there are often hidden systems operating beyond public view. Shining light on these systems—and dismantling them when necessary—remains one of the most important tasks for a just society.