The Truth Behind Jeffrey Epstein's Emails: Fact Or Fiction?
Have you ever wondered if the emails attributed to Jeffrey Epstein are actually real? In an age where digital manipulation and misinformation run rampant, it's natural to question the authenticity of sensitive documents, especially when they involve high-profile figures connected to criminal investigations. The Jeffrey Epstein case has been shrouded in controversy, conspiracy theories, and unanswered questions since his arrest in 2019. But what about the emails? Are they genuine communications, or sophisticated fabrications designed to fuel speculation?
The question of whether Jeffrey Epstein's emails are real touches on fundamental issues of digital forensics, legal evidence, and public trust. With so much at stake—including potential criminal investigations, civil lawsuits, and the reputations of powerful individuals—determining the authenticity of these emails isn't just about satisfying curiosity. It's about understanding the truth behind one of the most notorious criminal cases of our time.
Who Was Jeffrey Epstein?
Jeffrey Epstein was a wealthy financier and convicted sex offender whose life and crimes have captivated public attention for years. Born in 1953 in Brooklyn, New York, Epstein built a career in finance, eventually managing money for billionaires and establishing connections with influential figures across politics, science, and entertainment. His rise from a modest background to the upper echelons of wealth and power remains one of the more perplexing aspects of his story.
Epstein's criminal activities came to light through a series of investigations that revealed a pattern of sexual abuse involving underage girls. In 2008, he pleaded guilty to soliciting prostitution from a minor in Florida and served 13 months in a county jail under controversial circumstances that allowed him to leave the facility for work release six days a week. This lenient sentence sparked outrage and raised questions about his connections and influence.
The full extent of Epstein's crimes became clearer in 2019 when federal authorities arrested him on new charges of sex trafficking of minors. He died by suicide in his jail cell in August 2019 while awaiting trial, leading to even more conspiracy theories and unanswered questions. His death, combined with the ongoing investigation into his associates and the mysterious circumstances surrounding his wealth, has kept public interest in his case alive.
Personal Details and Bio Data
| Category | Details |
|---|---|
| Full Name | Jeffrey Edward Epstein |
| Date of Birth | January 20, 1953 |
| Place of Birth | Brooklyn, New York, USA |
| Date of Death | August 10, 2019 |
| Place of Death | Metropolitan Correctional Center, New York City |
| Education | Cooper Union (dropped out), Courant Institute of Mathematical Sciences at NYU (attended) |
| Occupation | Financier, convicted sex offender |
| Known For | Sex trafficking, connections to powerful figures, controversial death |
| Net Worth | Estimated $500 million - $1 billion |
| Criminal Charges | Sex trafficking of minors (2019), soliciting prostitution from a minor (2008) |
| Notable Associates | Bill Clinton, Donald Trump, Prince Andrew, Bill Gates, Les Wexner |
The Origins of the Epstein Email Controversy
The controversy surrounding Jeffrey Epstein's emails began to gain traction in the aftermath of his 2019 arrest. As investigators combed through his properties and digital devices, reports emerged about the discovery of vast amounts of data, including emails, documents, and other electronic communications. The sheer volume of information—allegedly spanning decades—raised immediate questions about what might be contained within these communications.
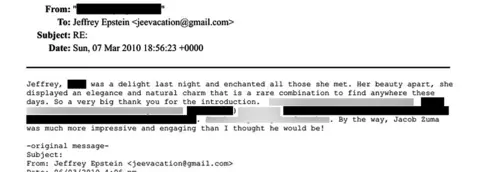
One of the most significant aspects of the email controversy involves the potential connections between Epstein and his powerful associates. Many people believe that emails could contain evidence of criminal activity, coordination among elites, or information about other individuals involved in Epstein's alleged trafficking network. This belief has fueled intense public interest and speculation about the contents of these communications.
The controversy was further amplified by the mysterious circumstances surrounding Epstein's death and the subsequent release of documents in various legal cases. When court documents were unsealed and certain materials became public, it only intensified the desire to know what else might exist in the form of emails and other communications. The question of authenticity became particularly important because any fabricated emails could be used to damage reputations or advance conspiracy theories.
Analyzing the Authenticity of Alleged Epstein Emails
When examining the authenticity of emails allegedly connected to Jeffrey Epstein, several factors come into play. Digital forensics experts look for specific markers that can verify whether an email is genuine or fabricated. These include metadata analysis, header information, IP addresses, timestamps, and the email's path through various servers. Understanding these technical aspects is crucial for anyone trying to determine the legitimacy of controversial communications.
One of the primary challenges in verifying Epstein-related emails is the lack of official sources releasing verified communications. Much of what circulates online comes from anonymous sources, conspiracy theory websites, or individuals claiming to have access to insider information. Without authentication from credible authorities or the release of emails through official channels, it becomes extremely difficult to verify their authenticity.
Experts in digital forensics note that creating convincing fake emails has become increasingly sophisticated. With modern technology, it's possible to forge headers, manipulate timestamps, and create emails that appear authentic at first glance. However, there are often subtle indicators that can reveal forgeries, such as inconsistencies in formatting, impossible time zones, or email addresses that don't match the purported sender's known accounts.
The Role of Digital Forensics in Email Verification
Digital forensics plays a critical role in determining whether emails attributed to Jeffrey Epstein are real or fabricated. Forensic analysts examine multiple layers of an email's structure to authenticate its origin. This process involves analyzing the email header, which contains information about the servers the email passed through, the originating IP address, and the software used to send the message.
One of the most important aspects of email forensics is metadata analysis. Metadata includes information like when the email was sent, the device used to compose it, and the route it took through the internet. For emails to be considered authentic, this metadata must be consistent with the alleged sender's known patterns and technical capabilities. Any discrepancies in this information can raise red flags about the email's authenticity.
Chain of custody is another crucial factor in email verification. For emails to be admissible as evidence in legal proceedings, there must be a clear record of who handled them and how they were preserved. This documentation helps establish that the emails haven't been tampered with or altered since their creation. In the case of Epstein-related emails, questions about chain of custody have made verification more challenging.
Common Characteristics of Verified vs. Fake Emails
Understanding the difference between verified and fake emails can help readers evaluate the authenticity of documents they encounter. Verified emails typically have consistent metadata that aligns with the sender's known patterns. The headers show a logical path through legitimate email servers, and the content is consistent with the sender's writing style and typical communications.
Fake emails often contain subtle but detectable errors. These might include impossible timestamps that suggest the email was sent from multiple locations simultaneously, headers that don't match the purported sender's email provider, or content that uses language or references inconsistent with the sender's known communications. In some cases, fake emails may contain anachronisms—references to events or technologies that didn't exist when the email was supposedly written.
Another red flag for fake emails is the presence of formatting inconsistencies. Authentic emails from a particular sender usually maintain consistent formatting patterns, while fake emails might show variations that suggest they were created using different software or by different people. Additionally, verified emails often have corresponding records in the recipient's email history, while fake emails may exist only in isolation without any supporting documentation.
The Impact of Fake Emails on Public Perception
The circulation of potentially fake emails related to Jeffrey Epstein has had a significant impact on public perception and the broader conversation about his crimes. When unverified or fabricated emails circulate online, they can create false narratives that distract from verified facts and legitimate investigations. This misinformation can make it harder for the public to understand what really happened and who might be responsible.
Fake emails can also damage innocent people's reputations. When emails that appear to implicate powerful individuals are circulated without verification, it can lead to public accusations based on potentially fabricated evidence. This creates a situation where both the truth about Epstein's crimes and the reputations of those who may or may not be involved become obscured by a fog of unverified information.
The psychological impact of fake emails shouldn't be underestimated. When people encounter documents that seem to confirm their suspicions about powerful elites and criminal conspiracies, it can reinforce existing beliefs and make them less likely to accept verified information that contradicts those beliefs. This creates an environment where truth becomes relative and evidence becomes secondary to what people want to believe.
Legal Implications of Email Authentication
The authentication of emails has serious legal implications, particularly in cases involving criminal investigations like the Jeffrey Epstein matter. For emails to be admissible as evidence in court, they must meet specific standards of authenticity. This typically requires testimony from digital forensics experts who can verify that the emails are what they purport to be and haven't been altered or fabricated.
In criminal cases, the burden of proving authenticity often falls on the party introducing the emails as evidence. This means that prosecutors or investigators must be able to demonstrate through technical analysis and chain of custody documentation that the emails are genuine. Without this authentication, even compelling emails may be excluded from consideration by a court.
The legal standards for email authentication have become increasingly sophisticated as technology has advanced. Courts now expect detailed forensic analysis that can withstand scrutiny from defense attorneys. This includes analysis of metadata, verification of IP addresses, examination of server logs, and often comparison with verified emails from the same sender to establish consistent patterns.
How to Verify Email Authenticity Yourself
While professional digital forensics requires specialized tools and expertise, there are some steps individuals can take to evaluate the authenticity of emails they encounter. One of the first things to check is the email header, which can often be viewed in most email programs. The header contains information about the email's path through the internet and can reveal inconsistencies or suspicious patterns.
Another approach is to look for corroborating evidence. Authentic emails are often part of larger collections of communications that can be verified independently. If an email appears in isolation without any supporting documentation or context, that can be a red flag. Additionally, checking the email address and comparing it to known addresses for the purported sender can help identify potential forgeries.
It's also important to consider the source of the emails. Emails released through official channels, such as court proceedings or law enforcement investigations, carry more credibility than those obtained from anonymous sources or conspiracy websites. Being skeptical of sensational claims and looking for verification from multiple credible sources can help protect against misinformation.
The Technology Behind Email Forgery
Understanding how email forgery works can help people recognize potential fakes. Email systems were designed in an era when trust between servers was assumed, which means the basic protocols for sending email don't include strong authentication mechanisms. This design flaw makes it relatively easy for someone with technical knowledge to send an email that appears to come from someone else.
One common technique for email forgery is "spoofing," where the sender manipulates the email header to make it appear as if the message came from a different address. This can be done using various tools and techniques, some of which are readily available online. More sophisticated forgeries might involve compromising an actual email account and sending messages from it, making the forgery even harder to detect.
Advanced email forgery can also involve creating realistic-looking email threads that appear to show ongoing conversations. These forgeries might include multiple emails with consistent formatting and content that seems authentic. However, forensic analysis often reveals inconsistencies in metadata or patterns that don't match the purported sender's typical behavior.
The Broader Context of Epstein-Related Information
The controversy over Epstein's emails exists within a broader context of information—and misinformation—related to his case. Since his arrest and death, numerous documents, testimonies, and allegations have emerged, creating a complex landscape of verified facts and unverified claims. Understanding how to navigate this landscape requires critical thinking and attention to credible sources.
Official documents released through court proceedings have provided some verified information about Epstein's activities and associates. These documents have been subject to legal scrutiny and are generally considered reliable. However, they represent only a fraction of the information that has circulated about the case, and much of what people believe about Epstein comes from sources that haven't been independently verified.
The intersection of Epstein's case with conspiracy theories has further complicated the information landscape. Some genuine information has been mixed with fabricated content, making it difficult for the public to distinguish between what's real and what's not. This blending of fact and fiction has made it especially important to verify information before accepting it as true.
Conclusion
The question of whether Jeffrey Epstein's emails are real remains a complex and often contentious issue. While some emails have been verified through official channels and forensic analysis, many others circulating online lack proper authentication and may be fabricated. The importance of determining email authenticity goes beyond mere curiosity—it affects ongoing investigations, legal proceedings, and public understanding of one of the most significant criminal cases of our time.
As we've explored, verifying email authenticity requires technical expertise, attention to detail, and often access to resources that aren't available to the general public. The proliferation of sophisticated forgery techniques means that even emails that appear authentic at first glance may be fake. This reality underscores the importance of skepticism and verification when encountering potentially explosive documents.
Moving forward, the truth about Jeffrey Epstein's emails—both real and fake—will likely continue to emerge through official investigations and forensic analysis. For those following the case, the key is to rely on credible sources, understand the limitations of what can be verified, and remain open to new information as it becomes available through proper channels. In an age of digital misinformation, critical thinking and verification are more important than ever.