The Mystery Of Jeffrey Epstein's Missing Computer Window: What Really Happened?
What really happened to Jeffrey Epstein's computer systems in the days leading up to his arrest? The disappearance of critical digital evidence, particularly concerning a mysterious "missing computer window," has fueled conspiracy theories and raised serious questions about evidence tampering in one of the most high-profile criminal cases of our time. When federal investigators raided Epstein's properties, they expected to find comprehensive digital records that would support the mounting allegations against him. Instead, they discovered something far more troubling: gaps in the digital timeline that suggested deliberate deletion or manipulation of evidence.
The case of Jeffrey Epstein's missing computer window represents more than just a technical glitch—it's a window into the sophisticated methods allegedly used to conceal criminal activities and the challenges law enforcement faces when investigating powerful individuals with resources to erase their digital footprints. This article examines the evidence, the theories, and the implications of what investigators found (and didn't find) in Epstein's digital archives.
Jeffrey Epstein: A Brief Biography
Jeffrey Edward Epstein was an American financier and convicted sex offender who gained notoriety for his wealth, connections to powerful individuals, and subsequent criminal charges related to sex trafficking of minors. Born on January 20, 1953, in Brooklyn, New York, Epstein built a career in finance that eventually led to managing wealth for clients including Leslie Wexner, the founder of Victoria's Secret.
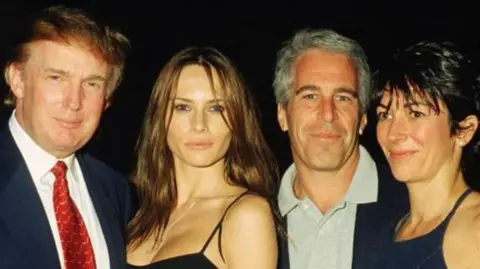
Epstein's rise in the financial world was marked by his work at Bear Stearns before establishing his own firm. His social connections included presidents, royalty, and celebrities, which would later complicate investigations into his activities. In 2008, he received a controversial plea deal for state charges in Florida, serving only 13 months in a private wing of a county jail. This deal, which has since been ruled illegal, allowed him to continue his activities for another decade.
In July 2019, Epstein was arrested again on federal charges of sex trafficking and conspiracy to commit sex trafficking of minors. He died by suicide in his jail cell on August 10, 2019, while awaiting trial. His death sparked numerous conspiracy theories and left many questions unanswered about his operations and associates.
Personal Details and Bio Data
| Category | Details |
|---|---|
| Full Name | Jeffrey Edward Epstein |
| Date of Birth | January 20, 1953 |
| Place of Birth | Brooklyn, New York, USA |
| Date of Death | August 10, 2019 |
| Education | Cooper Union (dropped out), Courant Institute of Mathematical Sciences at NYU (attended) |
| Occupation | Financier, convicted sex offender |
| Known For | Sex trafficking allegations, connections to powerful individuals, controversial 2008 plea deal |
| Criminal Charges | Sex trafficking of minors, conspiracy to commit sex trafficking (2019) |
| Net Worth | Estimated $500 million - $1 billion (at time of death) |
| Residences | New York City, Palm Beach, Santa Fe, Paris, U.S. Virgin Islands |
The Digital Evidence Trail: What Investigators Expected to Find
When federal agents executed search warrants at Epstein's properties in July 2019, they anticipated discovering a treasure trove of digital evidence that would corroborate witness testimonies and provide concrete proof of criminal activities. The investigation team, comprising the FBI and the Department of Justice, prepared for a comprehensive forensic analysis of multiple devices across Epstein's various residences.
Investigators expected to find:
- Detailed contact lists and communication logs
- Financial transaction records linking to alleged victims
- Video surveillance footage from hidden cameras
- Encrypted files containing sensitive information
- Cloud storage backups with years of archived data
- External hard drives and USB devices
The scope of the digital forensics operation was massive, involving specialized teams trained in recovering data from damaged, encrypted, or deliberately hidden files. The expectation was that Epstein's sophisticated operation would have left extensive digital footprints that could be traced and analyzed to build a comprehensive case against him and potentially his associates.
The Missing Computer Window: Timeline Discrepancies
The "missing computer window" refers to a specific period during which critical digital evidence appears to have been deliberately removed or destroyed. Forensic investigators discovered significant gaps in the timeline of Epstein's digital activity, particularly in the months and years leading up to his arrest.
Key findings included:
- Timestamp anomalies: Files that appeared to have been modified or accessed at impossible times
- Deleted system logs: Critical system files that should have maintained activity records were missing
- Encrypted partitions: Multiple hard drives contained encrypted sections that investigators couldn't access without proper keys
- Cloud account inconsistencies: Some cloud storage accounts showed signs of recent access after Epstein's arrest, suggesting someone else had credentials
- Device wipe indicators: Several devices showed evidence of factory resets or secure wipe procedures
The most concerning aspect was the systematic nature of these deletions. Rather than random data loss, investigators found patterns suggesting deliberate attempts to remove specific types of information while leaving other, less incriminating data intact.
Technical Analysis: How Evidence Could Be Deleted
Understanding how Epstein's digital footprint could be systematically erased requires knowledge of modern data deletion techniques. Professional data destruction goes far beyond simply deleting files or emptying a recycle bin.
Advanced deletion methods that may have been employed include:
- Secure erase protocols: These overwrite data multiple times with random patterns, making recovery virtually impossible
- Encryption without key storage: Files encrypted with keys that were subsequently destroyed
- Physical destruction: Hard drives that were drilled, shredded, or degaussed
- Cloud data manipulation: Remote access to cloud accounts to delete synchronized copies
- Log file tampering: Modification of system logs to hide evidence of file access or deletion
The sophistication of these techniques suggests either Epstein himself had advanced technical knowledge or he employed IT professionals specifically tasked with maintaining his digital security and, when necessary, destroying evidence.
The Role of IT Professionals in Evidence Tampering
The complexity of the missing computer window points to the likely involvement of IT professionals who managed Epstein's digital infrastructure. These individuals would have had the technical expertise to execute sophisticated data destruction while maintaining system functionality for legitimate users.
Potential scenarios include:
- Pre-planned destruction protocols: IT staff following instructions to delete specific data if certain trigger events occurred
- Remote access manipulation: Third parties gaining access to Epstein's systems through legitimate credentials
- Automated deletion systems: Software programmed to identify and remove specific types of content
- Decoy systems: Maintaining functional systems while critical evidence existed on separate, destroyed devices
The question of whether these IT professionals were complicit or acting under duress remains unanswered. Some may have been unaware of the full scope of their actions, while others might have been directly involved in planning the evidence destruction.
Legal Implications of Missing Digital Evidence
The disappearance of digital evidence in the Epstein case has significant legal ramifications. When critical evidence goes missing, it can undermine entire investigations and potentially allow criminals to escape justice.
Legal consequences include:
- Spoliation of evidence charges: Deliberate destruction of evidence can result in additional criminal charges
- Case dismissal risks: Insufficient evidence may force prosecutors to drop charges or accept lesser plea deals
- Civil liability: Individuals responsible for evidence destruction can face civil lawsuits
- Obstruction of justice: Deliberately impeding an investigation carries severe criminal penalties
The missing computer window has complicated efforts to prosecute not only Epstein but also his alleged co-conspirators. Without comprehensive digital records, prosecutors must rely more heavily on witness testimony, which can be challenged more easily in court.
Conspiracy Theories and Alternative Explanations
The mysterious nature of the missing computer window has spawned numerous conspiracy theories. While some explanations are more plausible than others, the lack of complete transparency has fueled speculation.
Popular theories include:
- Government involvement: Claims that federal agencies removed evidence to protect powerful individuals
- Foreign intelligence operations: Suggestions that foreign governments hacked Epstein's systems to protect their assets
** Insurance files: Theories that Epstein maintained "dead man's switch" files that would release information if he died - Accidental deletion: Claims that the gaps were caused by routine system maintenance rather than deliberate action
While many of these theories lack concrete evidence, they highlight the public's distrust of official explanations and the need for greater transparency in high-profile investigations.
Forensic Recovery Efforts and Their Limitations
Despite advanced forensic techniques, recovering deleted data has significant limitations. Modern deletion methods can make data recovery extremely difficult or impossible.
Challenges faced by forensic investigators:
- Encryption barriers: Without encryption keys, accessing protected data is nearly impossible
- Physical damage: Destroyed hardware cannot be analyzed
- Time delays: The longer investigators wait to examine devices, the more likely data will be overwritten
- Legal constraints: Warrants may not cover all devices or time periods
- Resource limitations: Comprehensive forensic analysis requires significant time and expertise
These limitations mean that even with the best technology and most skilled investigators, some deleted information may never be recovered.
The Broader Impact on High-Profile Investigations
The Epstein case has highlighted vulnerabilities in how law enforcement handles digital evidence in high-profile cases. The missing computer window has prompted discussions about improving investigative procedures.
Potential improvements include:
- Immediate evidence seizure: Faster response times when executing search warrants
- Better coordination: Improved communication between different law enforcement agencies
- Advanced monitoring: Real-time surveillance of suspects' digital activities
- Legislative updates: New laws addressing digital evidence preservation
- Public transparency: Greater disclosure about evidence collection and analysis methods
These changes could help prevent similar evidence gaps in future high-profile cases.
Conclusion: Unanswered Questions and Ongoing Mysteries
The mystery of Jeffrey Epstein's missing computer window remains one of the most troubling aspects of an already controversial case. The systematic deletion of digital evidence has not only hampered the investigation but also fueled conspiracy theories and public distrust.
Key takeaways from this investigation:
- The sophistication of evidence destruction suggests professional involvement
- Legal and technical limitations continue to challenge investigators
- The case has exposed vulnerabilities in how digital evidence is handled
- Public trust in official investigations has been damaged by the missing evidence
- The full extent of what was deleted may never be known
As investigations continue and new information potentially emerges, the missing computer window serves as a reminder of the challenges law enforcement faces in the digital age. It also underscores the need for improved procedures and greater transparency in handling evidence in cases involving powerful individuals with resources to conceal their activities.
The Epstein case continues to evolve even after his death, with ongoing investigations into his associates and the full scope of his operations. The missing computer window remains a central mystery in understanding the complete picture of what happened and who might have been involved in both the criminal activities and the subsequent evidence destruction.