The Jeffrey Epstein Technology Connection: Unveiling The Hidden Networks
Have you ever wondered about the technological infrastructure that enabled Jeffrey Epstein's complex operations? The intersection of Jeffrey Epstein technology and his criminal enterprise reveals a sophisticated network of digital tools, communication systems, and data management platforms that operated largely beneath public scrutiny. This article delves into the technological aspects of Epstein's world, examining how modern technology facilitated his activities and what this tells us about the vulnerabilities in our digital age.
Biography of Jeffrey Epstein
Jeffrey Edward Epstein was born on January 20, 1953, in Brooklyn, New York. He rose from modest beginnings to become a prominent financier, though his wealth and connections were often shrouded in mystery. Epstein's career began as a teacher at the Dalton School before transitioning to finance, where he worked at Bear Stearns before establishing his own wealth management firm.
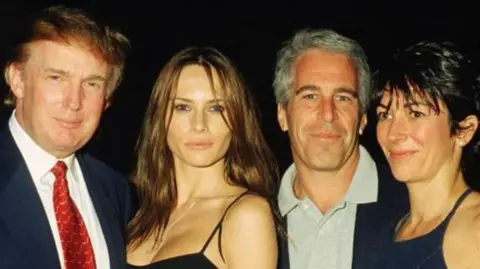
His trajectory from educator to financier to convicted sex offender represents one of the most dramatic falls from grace in recent American history. Epstein cultivated relationships with numerous high-profile individuals across politics, science, technology, and academia, creating a network that would later prove central to understanding the scope of his operations.
Personal Details and Bio Data
| Detail | Information |
|---|---|
| Full Name | Jeffrey Edward Epstein |
| Date of Birth | January 20, 1953 |
| Place of Birth | Brooklyn, New York, USA |
| Date of Death | August 10, 2019 |
| Education | Cooper Union (dropped out), Courant Institute of Mathematical Sciences at NYU (attended) |
| Professional Title | Financier, Registered Sex Offender |
| Known For | Wealth management, high-profile connections, criminal convictions |
| Net Worth | Estimated $500 million - $1 billion at peak |
| Primary Residence | New York City and Palm Beach, Florida |
| Criminal Status | Convicted sex offender (pleaded guilty in 2008), died in custody awaiting trial on federal charges in 2019 |
Jeffrey Epstein's Technological Infrastructure
The technological infrastructure surrounding Jeffrey Epstein's operations was far more sophisticated than many realize. Epstein maintained multiple properties equipped with advanced security systems, encrypted communication networks, and data storage facilities. His Little Saint James island in the U.S. Virgin Islands featured extensive technological installations, including underground facilities that reportedly housed computer servers and communication equipment.
Epstein's properties were known for their unusual architectural features, including hidden rooms, sophisticated surveillance systems, and what some described as data centers that appeared disproportionate to typical residential needs. These installations raised questions about the nature and extent of the digital operations conducted under his purview. The technology infrastructure wasn't merely for security or luxury—it suggested a complex system of information management and communication.
The Role of Science and Technology Funding
One of the most significant aspects of Jeffrey Epstein's technological influence was his funding of scientific research and technological development. Through the Jeffrey Epstein VI Foundation, established in 2000, he provided financial support to numerous scientists, researchers, and technological initiatives. This funding extended to artificial intelligence, quantum computing, and other cutting-edge fields.
Epstein's connections to prominent scientists like Stephen Hawking, Martin Nowak, and Lawrence Krauss created pathways for technological collaboration. His donations to institutions like Harvard University's Program for Evolutionary Dynamics demonstrated how financial resources could be leveraged to gain access to technological expertise and research capabilities. This intersection of finance, technology, and academia created a complex web of relationships that extended far beyond traditional investment activities.
Digital Communication Networks
The digital communication networks associated with Jeffrey Epstein's operations were reportedly extensive and sophisticated. Multiple sources have indicated that Epstein utilized encrypted messaging platforms, secure servers, and private networks to conduct his affairs. These systems would have been essential for maintaining confidentiality among the numerous high-profile individuals connected to his network.
Encrypted communication became increasingly important as awareness of Epstein's activities grew. The use of secure messaging apps, virtual private networks (VPNs), and other privacy-enhancing technologies suggests a deliberate effort to shield communications from public scrutiny. This aspect of Jeffrey Epstein technology raises important questions about how modern communication tools can be exploited by those seeking to conceal illicit activities.
Data Management and Storage Systems
The data management systems reportedly associated with Epstein's operations were reportedly substantial. Multiple properties featured server rooms and data storage facilities that exceeded typical residential requirements. These systems likely supported various functions, from security surveillance to document management and potentially more concerning activities.
The scale of these data storage systems suggests that Epstein and his associates were managing significant volumes of digital information. This could have included financial records, personal data, surveillance footage, and other sensitive materials. The existence of such extensive data management infrastructure points to the organized nature of Epstein's operations and the importance of information control within his network.
Connections to Silicon Valley and Tech Executives
Jeffrey Epstein's connections to Silicon Valley represent a particularly troubling aspect of his technological network. He cultivated relationships with numerous tech executives, venture capitalists, and entrepreneurs, often leveraging his wealth and connections to gain access to cutting-edge technological developments. These relationships extended to companies involved in artificial intelligence, biotechnology, and advanced computing.
The tech industry connections raised concerns about potential conflicts of interest and the ethical implications of accepting funding from controversial sources. Epstein's ability to navigate these relationships while maintaining his public persona as a legitimate financier demonstrates the complex intersections between technology, finance, and influence. The Silicon Valley connections also highlight how technological expertise can be leveraged for purposes beyond their intended applications.
Artificial Intelligence and Research Funding
Artificial intelligence emerged as a particular focus of Epstein's technological interests. He funded AI research at multiple institutions and maintained relationships with prominent researchers in the field. This involvement in AI development raised questions about the potential applications of artificial intelligence in his operations and the ethical implications of accepting funding from controversial sources.
The AI research funding extended to various applications, including pattern recognition, data analysis, and potentially surveillance technologies. Epstein's interest in these areas suggests a strategic approach to leveraging technological advancements for his purposes. The intersection of AI development and Epstein's network illustrates how cutting-edge technology can be influenced by individuals with questionable motives.
Surveillance and Security Technologies
The surveillance technologies employed across Epstein's properties were reportedly extensive. Multiple sources have described sophisticated camera systems, motion detectors, and other monitoring equipment installed at his residences and on his island. These security systems went far beyond typical luxury property installations, suggesting a need for comprehensive monitoring and control.
The surveillance infrastructure raises significant privacy concerns and questions about the extent of monitoring conducted on visitors and residents. The use of advanced security technologies in this context demonstrates how legitimate security tools can be repurposed for more concerning applications. This aspect of Jeffrey Epstein technology highlights the dual-use nature of many modern surveillance systems.
Cryptocurrency and Financial Technology
In the later years of his operations, there were indications that cryptocurrency and blockchain technology may have played a role in Epstein's financial activities. The anonymous and decentralized nature of cryptocurrencies would have aligned with his apparent need for financial privacy and security. While direct evidence remains limited, the timing and nature of his activities suggest possible exploration of blockchain technology.
The potential use of cryptocurrency raises important questions about how emerging financial technologies can be exploited by those seeking to conceal illicit activities. The intersection of financial technology and criminal enterprise represents a growing concern as digital currencies become more mainstream. Epstein's network may have been among the early adopters of these technologies for purposes beyond legitimate investment.
The Aftermath and Digital Evidence
Following Epstein's death in August 2019, investigations into his technological infrastructure continued. Law enforcement agencies reportedly seized numerous electronic devices, servers, and storage systems from his properties. The digital evidence collected represents a significant trove of information that could shed light on the full extent of his operations.
The posthumous investigation of Epstein's technology infrastructure highlights the challenges of digital forensics in complex cases. The encryption, data protection measures, and distributed nature of modern technology systems create significant obstacles for investigators. The ongoing examination of Jeffrey Epstein's digital footprint continues to reveal new information about the scope and nature of his technological operations.
Conclusion
The technological aspects of Jeffrey Epstein's operations reveal a sophisticated understanding of how modern technology can be leveraged for both legitimate and illicit purposes. From encrypted communications to advanced surveillance systems, from AI research funding to potential cryptocurrency use, the Jeffrey Epstein technology network represents a troubling case study in the intersection of technology, finance, and criminal enterprise.
Understanding these technological connections is crucial for developing better safeguards against similar abuses in the future. As technology continues to evolve, the lessons learned from examining Epstein's digital infrastructure become increasingly relevant. The case underscores the importance of ethical considerations in technological development and the need for robust oversight mechanisms to prevent the exploitation of advanced systems for harmful purposes.
The Jeffrey Epstein technology story serves as a reminder that technological sophistication alone is not sufficient—it must be coupled with strong ethical frameworks and accountability measures. As we continue to grapple with the implications of this case, the technological dimensions offer important insights into how modern tools can be both enabling and revealing, depending on how they are deployed and monitored.