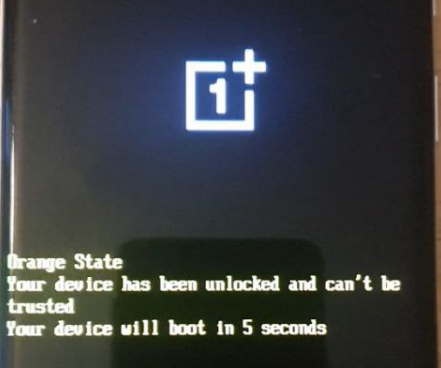
Your Device Has Been Unlocked And Can't Be Trusted: What This Warning Really Means
Have you ever seen the chilling message "your device has been unlocked and can't be trusted" flash across your screen? That sudden notification can feel like a digital red alert, instantly sparking anxiety. What does it mean? Is your phone compromised? Is your personal data at risk? This ominous warning isn't just a random glitch; it's a critical security signal from your device's operating system, primarily Android, indicating that a fundamental layer of its integrity has been altered. In this comprehensive guide, we will decode this warning, explore the technical mechanics behind it, assess the real-world risks, and provide you with clear, actionable steps to understand and address it. Whether you're a curious tinkerer or someone who accidentally triggered this message, understanding this alert is essential for protecting your digital life.
Decoding the Warning: What "Unlocked and Can't Be Trusted" Actually Means
At its core, this message is the manifestation of a failed security check. Modern smartphones are built with a chain of trust that starts at the very first code that runs when you power on the device—the bootloader. The bootloader is responsible for loading the operating system (like Android). Manufacturers lock this bootloader by default to ensure that only software they have verified and signed can run on your device. This protects against malware that could persist even after a factory reset.
When you unlock the bootloader, you are explicitly breaking this chain of trust. You are telling the device, "I want to run software that hasn't been approved by the manufacturer." This action is often the first step toward installing a custom recovery (like TWRP) and a custom ROM (like LineageOS), or gaining root access. The Android operating system, through a framework called Google SafetyNet Attestation API, constantly checks the device's integrity. When it detects an unlocked bootloader, a modified system partition, or the presence of root-management tools, it flags the device as "untrusted." The system then displays this warning to inform you that certain security-sensitive features and applications will no longer function correctly because the device's verified state has been compromised.
The Technical Chain: From Bootloader to SafetyNet
To fully grasp the warning, it helps to understand the sequence:
- Bootloader Lock: The device ships with a locked bootloader. Only firmware signed with the manufacturer's cryptographic key can be installed.
- Unlock Command: You (or someone) executes a command, often via
fastboot oem unlockor through developer options, which wipes the device and changes a flag in the bootloader, allowing unsigned images to be flashed. - Integrity Checks: Android's verified boot and dm-verity systems check that the system and boot partitions match the expected cryptographic hashes stored in the bootloader.
- SafetyNet Attestation: Apps, especially banking, payment, and streaming apps, query Google's SafetyNet servers. The device's "attestation" report includes a boolean "basicIntegrity" and "ctsProfileMatch" flag. An unlocked bootloader or modified system causes these to fail.
- The Warning: The OS or a specific app (like Google Play Services) interprets this failure and presents the user with the "your device has been unlocked and can't be trusted" alert. It's a direct consequence of a failed
ctsProfileMatch.
Why Manufacturers and Google Care: The "Why" Behind the Lock
You might wonder, why go through all this trouble? The reason is a multi-layered security model designed to protect you, the user, and the ecosystem.
Protecting Against Persistent Malware
A locked bootloader and verified boot are your primary defenses against bootkits and persistent malware. This type of malicious software can infect the boot or recovery partitions. Because these partitions are checked before the OS even loads, such malware could survive a complete factory reset, silently re-infecting your device every time you restart. By ensuring only signed, unmodified system images run, manufacturers drastically reduce this attack surface. The warning is a last line of defense, telling you that this protection is now offline.
Safeguarding Digital Rights Management (DRM) and Secure Payments
Services like Netflix, Amazon Prime Video, and banking apps rely on a secure, untampered execution environment to enforce DRM policies (like HD streaming) and protect financial transactions. The Widevine L1 DRM level, required for Full HD and 4K streaming on Android, is only available on devices with a locked bootloader and a passing SafetyNet attestation. Similarly, the Trusted Execution Environment (TEE) and hardware-backed keystore, which store sensitive biometric and payment credentials, are designed to work within a verified system. An unlocked device cannot guarantee this environment's integrity, so these services rightfully block access to prevent potential credential theft or content piracy.
Maintaining a Consistent and Secure User Experience
For the average user, an unlocked device can lead to a fragmented and unstable experience. System apps may crash, OTA (over-the-air) updates from the manufacturer will fail, and core functionality like Google Pay can become unusable. The warning is a clear signal that you have left the supported, secure, and predictable path. It's a guardrail, not a punishment, meant to steer users away from a configuration that inherently weakens the device's security posture.
The Real Risks of Ignoring the Warning: What's Actually at Stake?
Seeing this warning and choosing to ignore it is not a neutral act. It comes with tangible, often severe, consequences that extend beyond a few apps not working.
1. Complete Loss of Financial and Payment App Functionality
This is the most immediate and impactful risk. Google Pay (in regions using NFC), Samsung Pay, and most major banking apps will refuse to function. They perform deep SafetyNet checks and will detect an unlocked bootloader or root access immediately. You will be unable to add cards, make contactless payments, or even log in to view your accounts. Some apps may show a generic "device not supported" error, while others might display the exact "untrusted" message. This turns your smartphone from a powerful wallet into a mere communication device for financial matters.
2. Streaming Service Degradation and Blocking
As mentioned, Widevine L1 certification is lost. The practical outcome is that you will be downgraded to Widevine L3, which typically only supports Standard Definition (SD) streaming on most services. You will lose the ability to watch content in HD, Full HD, or 4K on platforms like Netflix, Disney+, Hulu, and HBO Max. Some services might block playback entirely on devices they deem insecure. For a media-centric user, this is a significant degradation of a core smartphone feature.
3. Increased Vulnerability to Malware and Data Theft
With the verified boot chain broken, your device is susceptible to kernel-level rootkits and system-level malware. These threats can hide from standard antivirus scans, monitor all your activity (keystrokes, messages, calls), and exfiltrate data silently. The very act of unlocking often requires installing custom recoveries and flashing ZIPs, which if sourced from untrusted repositories, can be the initial infection vector. Your device's "untrusted" state means it can no longer reliably detect if its own core system has been compromised.
4. Loss of OTA Updates and Manufacturer Support
Your phone will no longer receive official security patches or Android version updates over the air (OTA). When you try to install an update, the process will fail because the signature of the new system image won't match the unlocked bootloader's expected state. You will be stuck on the Android version you installed, missing critical security fixes that patch known vulnerabilities. Over time, this creates an increasingly dangerous security gap. Furthermore, if you need warranty service, the manufacturer will almost certainly void it upon detecting an unlocked bootloader.
5. App Incompatibility and Game Ban Risks
Beyond finance and streaming, many other apps perform integrity checks. Pokémon GO, Fortnite, and other competitive online games use SafetyNet or similar checks to prevent cheating. An untrusted device can lead to an immediate, permanent ban. Some productivity apps, especially those dealing with enterprise data, may refuse to run on unsecured devices as part of a company's Mobile Device Management (MDM) policy. The ecosystem of compatible software shrinks dramatically.
How Apps and Services Detect an "Untrusted" Device
The detection isn't a single check but a sophisticated combination of methods, making it very difficult to fool all systems all the time.
SafetyNet Attestation API
This is Google's primary tool. When an app requests an attestation, the device generates a cryptographically signed statement about its software and hardware state. This statement is sent to Google's servers for verification. The response includes:
- basicIntegrity: Indicates the device is running a basic Android environment (not an emulator, has passed some basic checks).
- ctsProfileMatch: The gold standard. This means the device's software profile (build parameters, system properties, security patch level) matches the Compatibility Test Suite (CTS) profile for that device model as certified by Google. An unlocked bootloader or custom ROM will fail this.
Hardware-Backed Keystore and Key Attestation
Secure hardware (Titan M, TrustZone) can generate keys that are cryptographically bound to the device's verified state. If the boot state changes, these keys become invalid or can't be generated. Apps that use this for high-security operations (like banking) will fail if the hardware can't provide a valid attestation chain.
Root Detection Techniques
Even if you hide root from some apps using tools like MagiskHide or Zygisk, detection methods evolve:
- Checking for su binary, Magisk app, or root management packages.
- Scanning for dangerous props (system properties that indicate a modified build).
- Checking for writable system partitions.
- Using native code to probe for root binaries in expected paths.
- Analyzing the output of the
getpropcommand for telltale signs of custom ROMs.
Play Integrity API
Google is phasing in the newer Play Integrity API, which replaces SafetyNet for many developers. It provides even more detailed signals, including a clear "MEETS_DEVICE_INTEGRITY" verdict. It's harder to spoof and integrates more deeply with Google Play Services.
What To Do If You See This Warning: A Step-by-Step Guide
Your response depends entirely on why you're seeing it. Did you intentionally unlock your device, or is this a surprise?
Scenario 1: You Intentionally Unlocked Your Bootloader
If you unlocked it to install a custom ROM or root, you are operating in an advanced, unsupported, and inherently insecure state by design. Your options are:
- Accept the Consequences: Live with the limitations. Use your device for tasks that don't require high security or premium streaming. Use alternative payment methods (like a separate, locked device or a physical card). This is the path of the enthusiast who values customization over convenience and security.
- Re-lock the Bootloader (If Possible):This is extremely device and ROM-specific and often impossible. Some manufacturers (like Google with Pixel) allow re-locking after flashing a stock factory image. If you are on a custom ROM, re-locking is almost never supported and will likely brick your device. If you have a Pixel and want to return to stock, use the official Android Flash Tool to restore factory images, which will re-lock the bootloader during the process.
- Use Magisk for "Stealth" Root: If your goal was root access for specific modules (like ad-blockers or UI tweaks), use the latest Magisk with Zygisk and its DenyList feature. Configure it to hide root from the specific apps that are complaining (Google Play Services, banking apps). Note: This is a constant cat-and-mouse game. Google updates detection, Magisk updates to hide. It is never a 100% guaranteed permanent solution.
Scenario 2: You Did NOT Unlock Your Device (Surprise Warning)
This is a rarer but serious scenario. Possible causes include:
- A buggy system update that incorrectly flags your device.
- Malware that has flashed a modified boot image without your knowledge.
- A used device purchased with an already-unlocked bootloader that was not properly re-flashed to stock.
Your Action Plan:
- Immediately Backup Critical Data. Assume the device may be compromised.
- Perform a Full Factory Reset from Recovery Mode. Do not just reset from settings. Power off, boot into recovery (usually Volume Up + Power), and select "Wipe data/factory reset." This removes user data but does not fix a modified system/boot partition.
- Flash Official Stock Firmware. This is the nuclear and only certain option. You must download the exact factory image for your device model and region from the manufacturer's website (e.g., Samsung's Frija tool, Google's Flash Tool, Xiaomi's Mi Flash). Using tools like Odin (Samsung) or fastboot, flash the AP, BL, CP, CSC files (or equivalent). This will overwrite the bootloader, system, and all partitions with a clean, signed, locked version. This will erase all data.
- After Re-flashing: Do not root or unlock again. The warning should be gone. If it returns immediately after a clean flash without any action on your part, the device's hardware security fuses may have been permanently altered (e.g.,
avbhash tree flag), indicating a deep, possibly unrecoverable compromise. In this case, the device should be considered compromised and retired from sensitive use.
Prevention and Best Practices: Staying in the "Trusted" Zone
The best strategy is to avoid triggering the warning in the first place.
- Never unlock the bootloader on your primary device if you rely on banking, mobile payments, or premium streaming.
- Maintain a "clean" secondary device for experimentation with custom ROMs and rooting. Keep your daily driver pristine.
- Only install apps from the Google Play Store and avoid sideloading APKs from unknown sources, which is a common infection vector.
- Keep your device updated with official OTA security patches.
- Be extremely cautious with "root checker" or "bootloader unlocker" apps from unofficial sources—they can be malware.
- If buying a used phone, insist on a device with a locked bootloader and perform a fresh official firmware flash before using it for sensitive tasks.
Frequently Asked Questions (FAQs)
Q: Can I use a VPN to bypass this warning?
A: No. The SafetyNet/Play Integrity check happens locally on your device and is cryptographically signed. A VPN only encrypts your network traffic; it does not alter the device's local integrity state.
Q: Will a factory reset fix the "unlocked" warning?
A: No. A factory reset only wipes the /data partition (your apps, settings, files). The bootloader status and system partition modifications reside in /boot and /system, which are untouched by a standard reset. Only re-flashing stock firmware can restore these.
Q: Is there any legitimate reason to unlock my bootloader?
A: Yes, for development, installing certified custom ROMs (like LineageOS without GApps), or deep system customization. However, you must accept the trade-offs: loss of security features, payment functionality, and OTA updates. It is a choice for enthusiasts, not for security-conscious users.
Q: Do iPhones have this warning?
A: The concept is similar but the implementation differs. iPhones have a "nonce" and "sep" security system. Jailbreaking an iPhone breaks its chain of trust. While you won't see an identical pop-up, apps like banking apps and Netflix will detect the jailbreak via known methods (file existence, sandbox violations) and refuse to run, often with a generic "unsupported device" message. The principle of a compromised trusted execution environment is the same.
Q: Can malware cause this warning without me unlocking anything?
A: Theoretically, yes, if the malware exploits a privilege escalation vulnerability (a "root exploit") to modify the boot or system partitions. This is a severe, low-level compromise. The warning in this case is a correct and critical indicator that your device's firmware has been altered by an unauthorized party. The remediation is the same: a full, official firmware re-flash.
Conclusion: Heeding the Digital Sentinel
The message "your device has been unlocked and can't be trusted" is not an annoyance to be dismissed. It is your device's digital sentinel, a final, unambiguous warning that the foundational security guarantees designed to protect your data, your money, and your privacy have been voluntarily or maliciously dismantled. It signals the end of the verified boot chain, the failure of SafetyNet, and the activation of a high-risk state.
For the vast majority of users, this state is unacceptable. The convenience of a few custom tweaks or root-access apps is a poor trade for the loss of secure mobile payments, high-definition streaming, timely security updates, and robust protection against sophisticated malware. If you see this warning and did not intentionally unlock your device, treat it as a potential security incident. Back up your data and perform a clean re-flash of official firmware without delay.
Ultimately, this warning forces a fundamental question: what is the value of your digital trust? In an era of rampant data breaches and financial fraud, a device that cannot be trusted is a liability. The path of the locked bootloader, while less flexible, is the path of security, compatibility, and peace of mind. Choose wisely.