Ari Kytsya Girthmaster Leak: What Happened And What It Means For Online Privacy
What exactly is the "Ari Kytsya Girthmaster leak," and why has it sparked such intense debate about digital consent and creator rights? In the fast-paced world of online content creation, where personal brands are built on exclusive platforms like OnlyFans, a single security breach can unravel years of careful work. The incident involving popular creator Ari Kytsya and the moniker "Girthmaster" serves as a stark, modern case study in the vulnerabilities faced by digital entrepreneurs. This comprehensive article delves deep into the origins of the leak, its profound impact on those involved, and the critical lessons it offers for every internet user and content creator navigating an increasingly exposed digital landscape.
Understanding the Incident: Unpacking the "Ari Kytsya Girthmaster Leak"
The term "Ari Kytsya Girthmaster leak" refers to the unauthorized distribution of private, explicit content originally created and sold by the adult content creator known online as Ari Kytsya. The content, which was part of her paid subscription service, was allegedly obtained and then repackaged or redistributed under the label "Girthmaster," a term often associated within certain online communities. This wasn't a simple case of a subscriber sharing a single image; it represented a systematic breach of her digital storefront, where paid content was made freely available on various file-sharing sites, forums, and social media platforms without her consent.
For creators like Ari Kytsya, whose livelihood depends on the controlled exchange of intimate content for a fee, such a leak is catastrophic. It directly attacks their revenue stream, as subscribers who can access the material for free have no incentive to pay. Furthermore, it constitutes a severe violation of personal autonomy and privacy. The content was created with an expectation of a limited, paying audience, not for public consumption. The leak transforms a consensual, commercial transaction into a non-consensual, widespread public spectacle, stripping the creator of all control over how, where, and with whom their most private material is shared.
The Ripple Effects: Beyond Financial Loss
The consequences of such a leak extend far beyond immediate lost income. There is a profound psychological toll. Creators often report feelings of violation, anxiety, and a loss of safety. The knowledge that deeply personal images and videos are circulating indefinitely on the internet, beyond one's ability to retract them, can lead to significant stress, depression, and a sense of powerlessness. This psychological burden can impact every aspect of their life, from personal relationships to their ability to create new content.
There are also serious reputational risks. While Ari Kytsya's brand is built in the adult space, a leak can still damage her specific reputation for reliability and security. Potential new subscribers may hesitate, fearing their own access could be compromised or that the content is no longer "exclusive." Moreover, the leak can spill over into her personal life, affecting friends, family, and future non-adult career opportunities. In our digital age, a past leak can haunt an individual for years, resurfacing at inopportune moments.
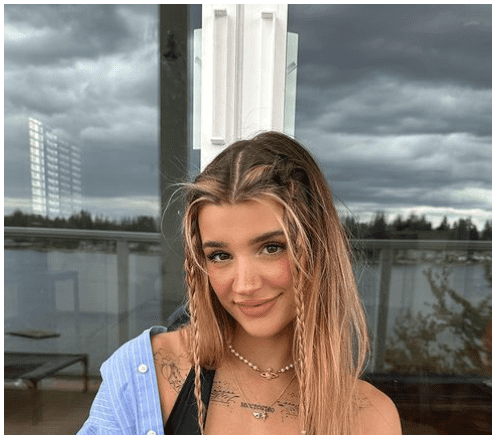
Who is Ari Kytsya? A Look at the Creator Behind the Headlines
To understand the full impact of the leak, it's essential to look at the person behind the online persona. Ari Kytsya is a prominent figure in the adult content creation industry, primarily known for her work on subscription-based platforms like OnlyFans and Fansly. She cultivated a significant following by offering a mix of professional photoshoots, videos, and personalized interactions, building a brand centered on a specific aesthetic and direct fan engagement.
Her success is not accidental; it represents the entrepreneurial spirit of the modern creator economy. She manages her own content schedule, marketing, customer service, and financials. For many, this level of independence and control over their work and image is a primary draw of the industry, offering a stark contrast to traditional adult entertainment pipelines.
Personal Details and Bio Data
| Attribute | Details |
|---|---|
| Online Alias | Ari Kytsya |
| Primary Platforms | OnlyFans, Fansly, Twitter (X) |
| Content Niche | Adult entertainment, lifestyle, fan interaction |
| Estimated Following | Hundreds of thousands across platforms (exact figures fluctuate) |
| Business Model | Subscription-based, pay-per-view content, tips |
| Known For | High-quality production, consistent posting schedule, direct fan engagement |
| Incident | Subject of a major content leak in [Year of leak, if known, otherwise use "recent years"] |
The Anatomy of a Content Leak: How It Typically Happens
Understanding the mechanics of how leaks occur is crucial for prevention. While the precise method in the "Girthmaster" case may not be publicly confirmed, leaks generally follow a few common patterns.
Account Compromise: This is one of the most frequent vectors. A creator's platform account (OnlyFans, email, cloud storage) may be hacked through phishing scams, password reuse, or malware. Once the attacker has login credentials, they can download the entire content library and distribute it at will. The "Girthmaster" leak's scale suggests a compromise of a primary storage account rather than isolated screenshot sharing.
Insider Threat: Sometimes, leaks originate from within a creator's circle—a former partner, disgruntled employee, or even a trusted collaborator with access to files. This betrayal is particularly damaging as it exploits a personal relationship of trust.
Subscription Scraping & Aggregation: Tech-savvy individuals or groups use automated tools to scrape content from subscription platforms. While platforms have anti-scraping measures, determined actors can sometimes circumvent them, especially if a creator posts content in a way that can be captured (e.g., screen recording). The aggregated content is then uploaded to dedicated "leak" sites.
The "Girthmaster" Ecosystem: The naming suggests the leak may have been organized. Leak groups often rebrand stolen content with their own watermark or tag (like "Girthmaster") to build a brand around distributing pirated material, driving traffic to their own sites or forums. This turns a single leak into a persistent, searchable archive.
The Legal Landscape: Copyright, Privacy, and the Fight for Justice
From a legal standpoint, a leak like this is a clear-cut case of copyright infringement and potentially invasion of privacy or misappropriation of likeness. The creator holds the copyright to the images and videos they produce. Distributing them without permission violates intellectual property law. Furthermore, in many jurisdictions, the non-consensual distribution of intimate images, often called "revenge porn" laws, is a criminal offense, regardless of whether the distributor was originally a paying subscriber.
What Can Creators Do Legally?
- DMCA Takedown Notices: The first and most common step. Creators can send Digital Millennium Copyright Act notices to websites hosting the leaked content, demanding its immediate removal. While effective against compliant platforms, it's a game of whack-a-mole against sites hosted in jurisdictions with lax enforcement.
- Cease & Desist Letters: Formal legal letters to the identified distributor (if possible) demanding they stop and destroy all copies.
- Law Enforcement Report: Filing a report with local police or federal agencies (like the FBI in the U.S.) for computer fraud, theft, and violations of revenge porn statutes. This is a more serious step that can lead to criminal charges if the perpetrator is identified.
- Civil Lawsuits: Suing for damages. This can include lost revenue, statutory damages for copyright infringement, and compensation for emotional distress. However, litigation is expensive and time-consuming, and identifying anonymous online distributors can be a major hurdle.
The "Ari Kytsya Girthmaster leak" highlights the gap between the speed of digital piracy and the often-slower wheels of justice. While legal recourse exists, the practical challenge of policing the entire internet means much of the damage is immediate and potentially permanent.
Platform Responsibility: The Role of OnlyFans and Others
This incident inevitably raises questions about the security obligations of platforms like OnlyFans. These companies are not mere passive hosts; they are active businesses that profit from creator subscriptions. They have a fiduciary and ethical responsibility to implement robust security measures.
Expected Platform Safeguards Include:
- Strong, Enforced Two-Factor Authentication (2FA): Making it mandatory for all accounts, especially high-earning creators.
- Advanced Login Monitoring: Systems that flag and block suspicious login attempts from new devices or geographic locations.
- Watermarking & Fingerprinting: Invisible digital watermarks embedded in content that can trace a leak back to a specific subscriber account.
- Rapid Response Takedown Teams: Dedicated, well-resourced teams to process DMCA notices and act on reports of leaks swiftly.
- Transparent Communication: Clear, timely communication with creators when a potential breach is detected.
Critics argue that platforms could do more, such as implementing more aggressive anti-scraping technology or providing creators with more granular download controls (e.g., disabling right-click save, limiting video quality). The "Girthmaster" leak serves as a pressure point, pushing the entire industry to continually evaluate and upgrade its security protocols.
Protecting Yourself as a Creator: Practical Security Tips
While platforms bear significant responsibility, creators must also be proactive in securing their digital assets. Here is an actionable security checklist:
- Password Hygiene is Non-Negotiable: Use a unique, complex password for every single account (email, platform, cloud storage). A password manager like Bitwarden, 1Password, or Dashlane is essential.
- Enable ALL Available 2FA: Prefer authenticator apps (Google Authenticator, Authy) over SMS-based 2FA, which can be hijacked via SIM swap.
- Segregate Your Accounts: Do not use your personal, everyday email for your creator business. Create a dedicated, secure email for all platform registrations and financial communications.
- Secure Your Devices: Ensure your computer and phone have up-to-date antivirus software, firewalls, and operating system patches. Be wary of phishing emails and suspicious links.
- Be Wary of "Verification" Scams: No legitimate platform employee will ever ask for your password or 2FA code via direct message or email.
- Limit Content Downloads: If your platform allows, disable the ability for subscribers to download videos. While not foolproof (screen recording remains an issue), it raises the barrier.
- Regularly Audit Connected Apps: Review which third-party apps have access to your social media and platform accounts. Revoke access for anything unused or suspicious.
- Consider a "Burner" for Business: Some high-risk creators use a dedicated smartphone and computer solely for their business, isolated from personal data.
The Broader Implications: Privacy in the Digital Age
The Ari Kytsya leak is not an isolated incident. It is a symptom of a pervasive problem: the erosion of digital privacy and the commodification of personal data. For adult creators, this risk is amplified due to the nature of their content and the stigma that can still attach to their work, sometimes leading to less sympathy from law enforcement or platforms.
This event forces a larger conversation about consent in the digital era. Consent is not a one-time checkbox when a subscriber pays. It is an ongoing process that includes control over distribution. A leak completely nullifies the original consent given to a specific, paying audience. It also highlights the asymmetry of power in online spaces—individual creators versus organized piracy groups, and often, creators versus the platforms that host them.
What Can Fans and Subscribers Do? Ethical Consumption
Fans and subscribers have a crucial role to play in the ecosystem. Ethical consumption means:
- Never Share or Save Paid Content: Understand that paying for a subscription grants you a personal, non-transferable license to view content. It does not grant ownership or the right to distribute.
- Report Leaks Immediately: If you come across leaked content from a creator you support, report it to the platform it's on and notify the creator (if you have a safe way to do so). Do not engage with or share the links.
- Support Creators Directly: If you discover a leak, the best response is to double down on supporting the creator through official channels. Renew your subscription, purchase PPVs, or send a tip. This directly counters the financial damage of the leak.
- Respect Boundaries: Remember that creators are people. The content they produce is a product. Respect their boundaries regarding what they do and do not share, both online and off.
Conclusion: Navigating a Leaked World
The "Ari Kytsya Girthmaster leak" is more than just a salacious headline. It is a critical lesson in digital vulnerability, the high stakes of online entrepreneurship, and the fragile nature of consent in a world of infinite copying. For Ari Kytsya and countless creators like her, the incident represents a significant personal and professional setback, a violation that money alone cannot fully repair.
The path forward requires a multi-pronged approach: creators must become vigilant digital security experts; platforms must invest aggressively in proactive protection and rapid response systems; legal frameworks must continue to adapt to the speed of digital crime; and consumers must embrace a code of ethics that respects the labor and autonomy of creators. The leak of private content is never a victimless crime. It is a theft of safety, security, and sovereignty. As our lives and livelihoods become increasingly digitized, understanding and defending against this threat is not optional—it is a fundamental necessity for anyone who values privacy and creative independence in the 21st century. The story of Ari Kytsya is a reminder that behind every username and subscription is a real person, and the security of their digital world is everyone's responsibility.