Dump File Creation Failed? Decoding The "Error During Dump Creation" Message
Have you ever been in the middle of diagnosing a critical system or application crash, only to be met with the frustrating and cryptic message: "dump file creation failed due to error during dump creation"? You know that a memory dump is your single most valuable artifact for understanding why a system failed, but the very tool meant to capture that evidence has itself failed. This isn't just an inconvenience; it's a major roadblock that leaves you blindfolded in the middle of a forensic investigation, forcing you to guess at the root cause of instability, data corruption, or security breaches. This comprehensive guide will transform that frustrating error message from a dead-end into a clear diagnostic pathway. We will move beyond the basic error text to explore the intricate ecosystem of dump file generation, uncover the specific conditions that trigger this failure, and equip you with a systematic, actionable toolkit to not only resolve the immediate issue but also build a resilient debugging infrastructure for the future.
Understanding the Foundation: What Exactly Are Dump Files?
Before we can diagnose why their creation fails, we must have a crystal-clear understanding of what dump files are and the critical role they play in system reliability and security. In essence, a dump file (or crash dump, memory dump, core dump) is a snapshot of a process's or the entire system's memory at a precise moment in time—typically when an unhandled exception, kernel panic, or critical error occurs. Think of it as a forensic photograph of the system's brain at the instant of the "heart attack." This snapshot captures the state of all running threads, loaded modules (DLLs, drivers), register values, and the contents of memory, providing an immutable record that can be analyzed long after the transient error has passed and the system has rebooted.
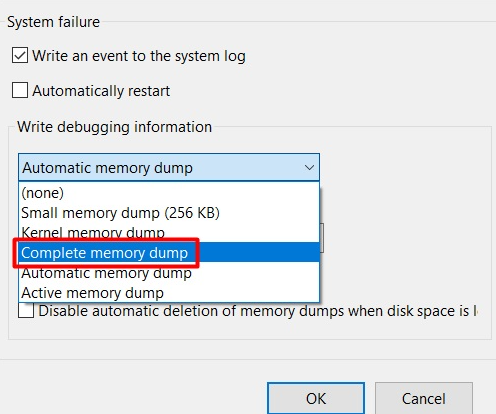
There are several primary types of dump files, each with a different scope and size:
- Small Dump (Minidump): The most common type, typically 256KB to 1MB. It contains crucial information like the exception record, stack traces for the threads that were executing, a list of loaded modules, and sometimes a small section of memory. It's fast to create and small to store, making it ideal for automated error reporting.
- Kernel Memory Dump: This is the workhorse for analyzing system-wide crashes (Blue Screens of Death on Windows). It records all the memory that the Windows kernel was using at the time of the crash. Its size is typically 1/3 to 1/2 of the system's physical RAM (e.g., a system with 16GB RAM might produce a 5-7GB dump). It includes kernel-mode drivers and system state.
- Complete Memory Dump: The most comprehensive (and largest) option, capturing all physical memory at the time of the crash. This is essential for analyzing issues that involve user-mode data or complex interactions but is rarely needed and can be prohibitively large.
- Automatic Memory Dump: A smart default on modern Windows that acts like a kernel dump but can include additional memory if the system has enough free space, optimizing for the most likely analysis scenarios.
The primary purpose of these files is post-mortem debugging. Without them, developers and system administrators are left with only the error code (like a Windows STOP code) and perhaps a vague event log entry. With a proper dump file, using tools like WinDbg (Windows Debugger) or Visual Studio, you can:
- Identify the exact function, driver, or module that caused the crash.
- Examine the call stack to see the sequence of events leading to the failure.
- Inspect variable values and memory contents at the time of the crash.
- Correlate the crash with specific system activity or recent changes.
- Provide developers with irrefutable evidence to fix a bug.
In short, a failed dump file creation doesn't just mean you lost a file; it means you lost the most powerful diagnostic key to a complex puzzle. The "error during dump creation" is the sound of that key snapping in the lock.
The Anatomy of Failure: Common Causes Behind "Error During Dump Creation"
The error message itself is a generic wrapper. The real error, the specific reason the dump engine aborted, is often logged elsewhere—in the Windows Event Viewer under System logs with sources like "BugCheck" or "Windows Error Reporting", or in the application's own logs. Understanding the common root causes is the first step to targeted troubleshooting.
1. Insufficient Disk Space and Permissions
This is the most frequent and straightforward culprit. Dump file creation is a write operation to a specific location (by default, %SystemRoot%\MEMORY.DMP for kernel dumps or %LOCALAPPDATA%\CrashDumps for user-mode application dumps).
- Disk Space: A kernel memory dump on a server with 64GB of RAM requires significant free space (often 20GB+). If the target drive is full or nearing capacity, the write operation will fail. This is especially common on system drives (C:) that are partitioned too small or on servers where log files and other data have grown unchecked.
- Permissions: The process responsible for writing the dump (often the System account or the Windows Error Reporting Service) must have Full Control permissions over the target directory. A misconfigured security policy, a third-party security tool that overly restricts the System account, or a simple ACL inheritance break can silently block the write.
2. Dump File Location is Invalid or Inaccessible
The configured dump file path might point to a location that no longer exists.
- A mapped network drive that is disconnected at boot time.
- A volume that has been offline, disabled, or has failed.
- A directory that has been deleted or renamed.
The dump writer will attempt to open a handle to this path and fail immediately if it's invalid, triggering the generic error.
3. The Dump Target Process or Service is Unavailable
The actual work of writing the dump is often performed by a dedicated service or process.
- Windows Error Reporting (WER) Service: If this service is disabled, stopped, or corrupted, it cannot accept the crash report and write the file.
- Debugging Services: In some enterprise environments, third-party crash dump collectors or debugging agents are used. If these are not running or have crashed themselves, the chain is broken.
- System Account Corruption: Since dumps are often written under the highly privileged Local System account, corruption or misconfiguration of this built-in account can lead to failure.
4. Hardware or Firmware Issues
This is a more insidious category. The act of dumping memory involves reading from physical RAM.
- Faulty RAM: A failing memory module can cause read errors during the dump process itself. The system might successfully crash but then be unable to reliably read the memory contents to write to disk.
- BIOS/UEFI Firmware Bugs: Outdated or buggy firmware can have issues with memory mapping or power management states that interfere with the low-level dump routines, especially during wake-from-sleep crashes.
- Storage Controller Issues: Problems with the disk controller driver or firmware can cause I/O errors during the critical dump write operation.
5. Software Conflicts and Kernel-Mode Interference
- Antivirus/Antimalware Real-Time Scanning: Overzealous security software can intercept the dump file creation process, seeing the large, rapid write of a
.dmpfile as suspicious behavior (akin to a memory-scraping malware) and block it. - Third-Party System Utilities: Tools that deeply hook into the system for monitoring, optimization, or encryption (e.g., some disk encryption tools, system cleaners, performance monitors) can conflict with the dump writer's low-level access.
- Driver Conflicts: A poorly written or outdated kernel-mode driver can corrupt memory or system state in such a way that the crash occurs, and the subsequent attempt to dump memory hits a secondary fault within that same corrupted driver space, causing a secondary failure.
6. Dump File Already Exists and is Locked
If a previous dump file (MEMORY.DMP) exists and is locked by another process (perhaps a debugger that has it open, an antivirus scanner, or a backup agent), the new dump cannot overwrite it. The system will fail to create the new file.
7. Group Policy or Registry Misconfiguration
The dump settings are controlled by the registry (HKLM\SYSTEM\CurrentControlSet\Control\CrashControl) and can be overridden by Group Policy.
- The
CrashDumpEnabledvalue might be set to0(disabled). - The
DumpFilepath might be mis-typed. - The
Overwritevalue might be set to0, and the existing dump file is locked, preventing a new one.
A policy push from IT could have inadvertently broken the configuration.
Systematic Diagnosis: Your Step-by-Step Investigation Protocol
When faced with "dump file creation failed," methodical diagnosis is key. Do not guess; investigate.
Step 1: Consult the Primary Evidence - The Event Viewer
This is your starting point. Open Event Viewer (eventvwr.msc) and navigate to Windows Logs > System. Filter for Event sources: "BugCheck" and "Windows Error Reporting" around the time of the crash. Look for events with Event ID 1001 (WER) or Event ID 1003 (BugCheck). The description of these events often contains the specific error code that caused the dump failure (e.g., 0x80070057 for invalid parameter, 0x80070005 for access denied, 0xC0000005 for access violation during dump). This code is your most critical clue.
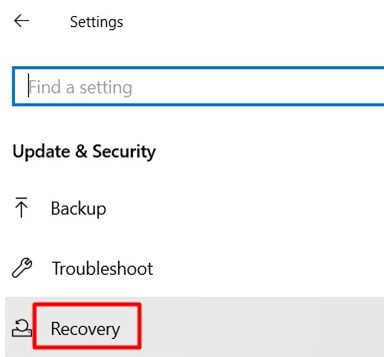
Step 2: Verify Dump Configuration and Disk Space
- Check Dump Settings: Open System Properties > Advanced > Startup and Recovery > Settings. Confirm:
- Dump file type is selected (Kernel memory dump, etc.).
- Dump file path is valid and on a drive with ample space.
- "Overwrite" is checked unless you have a specific archival need.
- Check Disk Space: On the target drive, ensure you have at least 1.5x the expected dump size free. For a kernel dump on a 32GB RAM system, have 50GB+ free.
- Check Permissions: Navigate to the dump file folder in Explorer. Right-click > Properties > Security. Ensure the SYSTEM account has Full Control. Also check if "TrustedInstaller" has control, which can sometimes interfere.
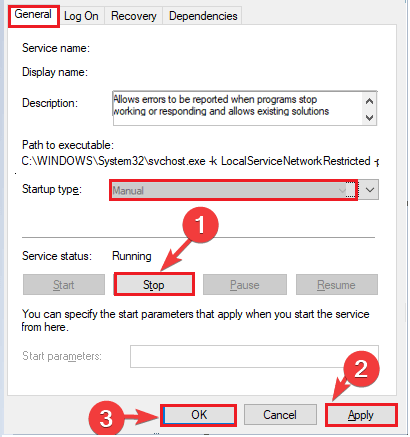
Step 3: Examine the Health of the Dump Infrastructure
- Service Status: Run
services.msc. Ensure Windows Error Reporting Service is set to Manual (it starts on demand) and is not disabled. Also check "Problem Reports and Solutions" service. - Test the Mechanism Manually: Force a test crash (on a non-production system!) using the NotMyFault tool from Microsoft Sysinternals or by setting the registry key
HKLM\SYSTEM\CurrentControlSet\Control\CrashControl\CrashOnCtrlScrollto1and then holding Right Ctrl and pressing Scroll Lock twice. Observe if a dump is created. This isolates whether the problem is with the crash event or the dump infrastructure. - Check for Locked Files: Use Sysinternals Handle or Process Explorer to search for handles on
MEMORY.DMPor your configured dump file name. If a process has it locked, stop that process.
Step 4: Investigate Software and Hardware Conflicts
- Clean Boot: Perform a clean boot (
msconfig> Services tab > Hide all Microsoft services > Disable all, then Startup tab > Open Task Manager > Disable all). Reboot and trigger a test crash. If the dump succeeds, a third-party service or driver is the culprit. Re-enable services in batches to isolate the offender. - Antivirus Exclusion: Temporarily disable your antivirus real-time protection and retry. If it works, add an exclusion for the dump file folder and the
werfault.exeprocess. - Memory Diagnostics: Run Windows Memory Diagnostic (
mdsched.exe) to check for RAM errors. - Update Firmware/Drivers: Ensure your BIOS/UEFI is updated. Update critical chipset, storage controller, and graphics drivers from the manufacturer's website.
Step 5: Analyze the Specific Error Code
If you found an error code in Step 1, research it.
0x80070005(E_ACCESSDENIED): Almost certainly a permissions issue on the dump folder or a security software block.0x80070057(E_INVALIDARG): Often a misconfigured registry path or an invalid parameter passed by a conflicting driver.0xC0000005(STATUS_ACCESS_VIOLATION): Indicates a driver or the dump process itself tried to read invalid memory, pointing to a faulty driver or hardware (RAM).0xC000021A(STATUS_SYSTEM_PROCESS_TERMINATED): A critical system process died during the dump, suggesting severe system instability or corruption.
Resolution Strategies: Fixing the "Error During Dump Creation"
Armed with a diagnosis, apply the targeted fix.
For Disk Space & Permission Issues
- Free Up Space: Use Disk Cleanup (as admin) to remove system files, old Windows updates, and temporary files. Manually clear old dump files and logs. Consider moving the dump location to a larger, dedicated data drive via the Startup and Recovery settings.
- Reset Permissions: On the dump folder, take ownership (Advanced > Owner), then grant SYSTEM and Administrators Full Control. Reset all permissions to defaults using
icacls "C:\" /reset /T /C(run as admin in the target drive's root) if corruption is suspected.
For Service and Configuration Problems
- Repair WER: Run
sfc /scannowandDISM /Online /Cleanup-Image /RestoreHealthfrom an elevated Command Prompt to repair system files. - Correct Registry/Group Policy: If Group Policy is overriding local settings, work with your IT department to correct the policy. Manually verify and set these registry values under
HKLM\SYSTEM\CurrentControlSet\Control\CrashControl:CrashDumpEnabled=1(for kernel dump)DumpFile=%SystemRoot%\MEMORY.DMPOverwrite=1
- Clear Stale Dumps: Delete any existing
MEMORY.DMPorMiniDumpfiles from the target folder. They may be locked or corrupted.
For Software Conflicts
- Configure Antivirus: Add explicit exclusions for:
- The dump file directory (e.g.,
C:\Windows\). - The process
C:\Windows\System32\werfault.exe. - The process
C:\Windows\System32\wer.dll.
- The dump file directory (e.g.,
- Identify the Offending Driver/Service: Use the clean boot method. Once identified, update that specific driver/software from the vendor's site. If it's a legacy driver with no update, consider removing or replacing the hardware/software it supports.
- Check for Pending Reboots: Some driver or Windows Update installations require a reboot to finalize. A pending reboot can leave the system in a state where dump creation fails. Reboot the server/workstation.
For Hardware and Firmware Issues
- Run Full Diagnostics: Use the manufacturer's diagnostic tools for your RAM (e.g., MemTest86+ from a bootable USB) and hard drives/SSDs.
- Update BIOS/UEFI: Visit your motherboard or system vendor's support page. Download and install the latest stable BIOS version, following their procedures carefully. This can resolve low-level memory mapping issues.
- Test with Minimal Hardware: If possible, remove non-essential hardware (extra RAM sticks, PCIe cards) and test dump creation with a minimal configuration to isolate a faulty component.
Proactive Measures: Building a Resilient Dump Strategy
Don't wait for a failure to occur. Implement these practices to ensure dump files are always there when you need them.
- Dedicated Dump Volume: On critical servers, create a small, dedicated partition (e.g., 50-100GB) on a fast, reliable drive separate from the OS drive. Point all dump files here. This eliminates OS drive space issues and isolates dump I/O.
- Automated Space Monitoring: Use Performance Monitor (perfmon) or a simple PowerShell script to alert you when the free space on the dump drive falls below a threshold (e.g., 20GB). A scheduled task can even clean old dumps automatically.
- Standardized Configuration via GPO: For domain-joined machines, use Group Policy Preferences to consistently configure dump settings across all servers/workstations, ensuring the correct path, type, and overwrite settings are enforced.
- Regular Health Checks: Incorporate a weekly check into your system administration routine:
- Verify the WER service is running.
- Check free space on the dump volume.
- Confirm the existence and accessibility of a recent test dump file.
- Document the Process: Create a runbook for your team that includes: the standard dump configuration, the primary diagnostic steps (Event Viewer, service check), and the escalation path for suspected hardware failures.
Advanced Tools and Techniques for the Persistent Problem
When standard fixes fail, you need to escalate your toolkit.
- Sysinternals Suite - Your Best Friend:
- ProcDump: This is the ultimate command-line utility for controlling dump creation. You can use it to manually create dumps of running processes (
procdump -ma <PID>), set triggers based on CPU, memory, or unresponsive windows (procdump -s 5 -n 3 -o <process>for 3 dumps after 5 seconds of high CPU), and bypass problematic system mechanisms entirely. If the built-in dump fails,procdumpoften succeeds because it uses a different code path. - DebugDiag: Microsoft's older but powerful tool for analyzing hangs and memory leaks. Its crash rule can be configured with specific dump settings and can sometimes succeed where the default WER fails.
- VMMap: Helps understand a process's memory usage. If a dump fails due to an "out of memory" error during the dump itself, VMMap can show if a process is using an abnormally large amount of non-paged pool, which could indicate a leak that's also interfering with the dump.
- ProcDump: This is the ultimate command-line utility for controlling dump creation. You can use it to manually create dumps of running processes (
- Windows Debugging (WinDbg) - Analyzing the Un-Dumped: If you have no dump at all from a crash, you can still analyze the BugCheck parameters from the Event Viewer (Event ID 1003). The four parameters after the STOP code (e.g.,
0x0000007E: 0xFFFFFFFFC0000005, 0xFFFFF80000000000, 0x0000000000000000, 0x0000000000000000) can sometimes be looked up in the Microsoft Debugging Tools documentation or with the!analyze -vcommand in WinDbg (using a symbol server) to get a preliminary hypothesis, though without a stack trace it's less precise. - Kernel Debugging: For the most stubborn, hardware-suspected cases, setting up a kernel debugger (using a second machine and a null-modem or network cable) allows you to break into the system at the moment of the crash before the dump attempt, potentially capturing state that the failed dump writer could not.
Conclusion: Turning a Debugging Nightmare into a Controlled Process
The "dump file creation failed due to error during dump creation" message is more than a simple file error; it's a meta-problem. It's a failure of the very system designed to help you diagnose failures. However, by understanding the architecture of dump generation, meticulously diagnosing the specific error code from the Event Viewer, and systematically eliminating common causes—from simple disk space shortages to elusive driver conflicts—you can reclaim your diagnostic capability. Remember the hierarchy: Check Event Viewer first, then disk space/permissions, then services, then software conflicts, and finally hardware. Implement proactive measures like dedicated dump volumes and automated monitoring to prevent recurrence. Tools like ProcDump are your powerful allies when the built-in mechanisms falter. Ultimately, mastering this process transforms you from a reactive troubleshooter into a proactive guardian of system stability. You ensure that the next time a critical crash occurs, you won't be staring at a dead end. Instead, you'll have a memory.dmp file ready and waiting, containing all the evidence you need to find the root cause, implement a permanent fix, and restore confidence in your systems. The key was always there; you just needed to know how to turn it.