Our Systems Have Detected Unusual Traffic: Your Complete Fix Guide
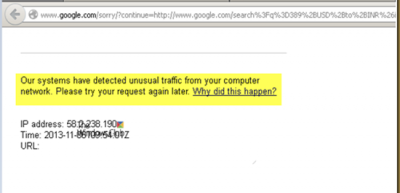
Have you ever been mid-research, ready to click through to a crucial result, only to be stopped dead by the frustrating message: "Our systems have detected unusual traffic from your computer network"? This digital roadblock can feel like an inexplicable lockdown on your own internet freedom. You’re not doing anything wrong—you’re just trying to search or browse—so why is this happening, and more importantly, how do you make it stop? This comprehensive guide dismantles this common error, explaining exactly what triggers it, providing immediate and advanced solutions, and giving you the proactive knowledge to prevent it from hijacking your workflow again.
This message is a security measure, not a personal accusation. Services like Google, Cloudflare, or various websites deploy sophisticated algorithms to distinguish between normal human browsing and automated, potentially malicious bot activity. When your network's request pattern matches the profile of a botnet, a scraper, or a DDoS attack, these systems instinctively throw up a barrier—often a CAPTCHA or a full block—to protect their servers and ensure fair access for all users. Understanding this is the first step toward reclaiming your smooth browsing experience. We’ll walk through everything from the simplest one-click fixes to deeper network diagnostics, ensuring you have a clear path forward no matter the cause.
What Does "Unusual Traffic" Actually Mean?
Decoding the Error Message
The phrase "our systems have detected unusual traffic from your computer network" is a standardized alert from anti-bot and DDoS mitigation services, most famously from Google’s reCAPTCHA system but also used by countless other websites protected by services like Cloudflare, Akamai, or Imperva. It’s a automated response triggered by behavioral analytics. These systems constantly monitor metrics such as the number of requests per second from a single IP address, the timing and pattern of those requests (e.g., perfectly spaced, robotic clicks), and the type of actions performed (e.g., rapid form submissions, high-volume data scraping). If your activity—or the activity of others sharing your IP—deviates from what’s statistically considered "normal" human behavior, the system flags it as "unusual."
It’s crucial to understand that the message points to your computer network, not necessarily your specific computer. This means the IP address assigned to your router by your Internet Service Provider (ISP) is the one under scrutiny. If you’re on a shared network—like in an office, school, coffee shop, or even a residential building with a single shared gateway—the actions of anyone using that same public IP can trigger the block for everyone. This collective responsibility is a common source of confusion and frustration.
Why These Protections Are Essential for the Internet
While inconvenient, these traffic filters are a critical line of defense for the modern web. Without them, websites would be overwhelmed by bot traffic, which according to recent cybersecurity reports, accounts for nearly 40% of all internet traffic. This includes malicious scrapers stealing content, credential stuffing attacks trying to break into accounts, and the massive networks of compromised devices (botnets) used for DDoS (Distributed Denial of Service) attacks that can take down major platforms. By challenging suspicious traffic with a CAPTCHA (Completely Automated Public Turing test to tell Computers and Humans Apart) or a temporary block, these systems:
- Protect server resources from being exhausted by non-human requests.
- Prevent fraud and abuse of online services (like ticket scalping or fake account creation).
- Ensure equitable access and performance for genuine users.
- Mitigate large-scale attacks that could disrupt service for thousands.
So, while the message is an annoyance, it’s also a sign that the security infrastructure is working as intended to keep the broader ecosystem stable.
Common Causes: Why Is Your Network Flagged?
Malware and Compromised Devices on Your Network
One of the most serious causes is a malware infection on a device connected to your network. Botnet malware, like Mirai or its variants, can secretly turn your smart TV, laptop, or even a router into a "zombie" device that participates in large-scale cyberattacks without your knowledge. Your network’s IP starts emitting a flood of requests to target websites, triggering the "unusual traffic" alert on your subsequent visits. This is why a sudden, unexplained block, especially if persistent, warrants a full security scan of all networked devices.
The Shared IP Dilemma: VPNs, Proxies, and Public Networks
This is the most frequent culprit for the average user.
- VPNs (Virtual Private Networks) and Proxy Servers: These services route your traffic through an intermediary server, masking your real IP. However, that server’s IP address is shared by hundreds or thousands of other users. If any one of those users engages in aggressive scraping or triggering activity, the entire IP address gets a bad reputation. Free VPNs are particularly notorious for this due to overcrowded and abused servers.
- Corporate/School Networks: Large institutions often use a single public IP for hundreds of users. Automated security scans, software updates, or even a single student running a data collection script can flag the whole network.
- Public Wi-Fi (Cafes, Airports, Libraries): Similar to corporate networks, the shared nature means you have no control over the collective traffic pattern. Your innocent search might follow a bot’s rapid-fire requests, landing you in the digital penalty box.
- Mobile Carriers and Large ISPs: Some internet providers, especially mobile carriers, use Carrier-Grade NAT (CGNAT). This means thousands of customers share a single public IP address. One heavy user or infected device on that network can cause blocks for everyone on that CGNAT block.
Your Own Browsing Behavior (It’s Not Always External)
Sometimes, the issue stems from actions on your own machine that mimic bot behavior:
- Rapid, Repetitive Actions: Manually refreshing a search results page dozens of times in quick succession, using browser extensions that auto-refresh, or running a script to automate form filling or data extraction.
- Multiple Tabs and Aggressive Search Patterns: Having dozens of tabs open that constantly fetch new data (like live sports scores or stock tickers) can look like a script hammering a server.
- Using Automated SEO or Research Tools: Many legitimate tools for keyword research, site auditing, or lead generation make numerous requests to Google and other sites very quickly. If not configured with proper delays (rate limiting), they will almost certainly trip this alarm.
- A Glitch or Bug: Occasionally, a temporary glitch in the service’s detection algorithm or a corrupted browser session can generate a false positive.
Immediate Solutions: How to Get Unblocked Right Now
Step 1: Solve the CAPTCHA (If Presented)
The most common resolution is a CAPTCHA challenge. When the message appears, look for a link or button that says something like "I'm not a robot" or "Verify you are human." Clicking this will usually present you with a classic CAPTCHA (distorted text) or the more modern "select all squares with traffic lights" type. Successfully completing this proves you’re a human and typically grants you a temporary "clearance" for that IP address, often for 24 hours or more. Always complete this step first if available.
Step 2: The Classic "Turn It Off and On Again" Approach
- Refresh the Page: After completing a CAPTCHA, a simple refresh (F5 or Ctrl+R) often restores normal access.
- Close and Reopen Your Browser: This clears temporary session data that might be contributing to the problem.
- Restart Your Router: This is a powerful step. By powering off your modem/router for 60 seconds, you force your ISP to assign you a new dynamic IP address (unless you have a static IP). A fresh IP has no "reputation" and should resolve the issue if the problem was tied to your old IP's history. This is the single most effective fix for issues caused by shared IP abuse.
Step 3: Clear Your Browser's Clutter
Corrupted or overloaded browser data can sometimes contribute to suspicious-looking requests.
- Clear your browser cache and cookies for the affected site (or all sites). Cached scripts or corrupted cookies can cause erratic behavior.
- Try an Incognito or Private Browsing window. This mode starts with a clean slate, no extensions, no cache. If the problem disappears in incognito, the issue is likely a browser extension or cached data in your main profile.
Step 4: Disable VPNs and Proxies Temporarily
If you are using any VPN, proxy service, or privacy-focused browser with built-in proxy (like Tor), disable it immediately. Connect directly to your ISP and try accessing the site again. If the block lifts, your VPN’s IP is the problem. You may need to switch VPN servers, contact your VPN provider, or consider using a more reputable, paid service with less crowded IP pools.
Step 5: Scan for Malware
If the problem persists despite the above steps, run a comprehensive malware scan on all computers and devices on your network. Use trusted security suites like Malwarebytes, Bitdefender, or Windows Defender (for PCs) and reputable antivirus apps for mobile devices. Look specifically for trojans, rootkits, and botnet clients. Ensure your router’s firmware is also updated, as compromised routers are a common botnet entry point.
Step 6: The Patience Test
Sometimes, the block is temporary and time-based. If you’ve tried the above and the message persists, wait 30 minutes to a few hours before trying again. The service may be implementing a "cool-down" period for your IP. Avoid making any more requests to that site during this wait, as it could extend the block.
Advanced Troubleshooting for Persistent Blocks
Investigate Browser Extensions Like a Detective
Some browser extensions, particularly ad-blockers, script blockers, privacy tools, and even some SEO plugins, can modify web traffic in ways that appear automated. Disable all extensions and reload the page. If it works, re-enable them one by one to find the culprit. Pay special attention to extensions that:
- Auto-fill forms or scrape page data.
- Block trackers and scripts aggressively (some sites interpret this as bot-like evasion).
- Manage cookies or sessions in unusual ways.
Flush DNS and Force a New IP Lease
Beyond restarting your router, you can manually force your computer to request a new IP from your local network and clear its DNS cache:
- On Windows: Open Command Prompt as Administrator. Type
ipconfig /release, press Enter. Then typeipconfig /renew, press Enter. Finally, typeipconfig /flushdns. - On macOS/Linux: Open Terminal. Type
sudo dscacheutil -flushcache(macOS) orsudo systemd-resolve --flush-caches(Linux). You may also need to renew DHCP:sudo ipconfig set en0 DHCP(macOS, interface may vary).
After this, restart your browser.
Contact Your Internet Service Provider (ISP)
If you suspect your ISP’s IP block is the issue (common with CGNAT or if your IP was previously used for malicious activity), call your ISP’s technical support. Explain you’re receiving a "unusual traffic" block from major services and believe your public IP may have a poor reputation. They may be able to:
- Assign you a new IP address from a different pool.
- Confirm if you are on a CGNAT network and discuss options for a dedicated IP (often a paid business service).
- Check if there is any known issue or malware outbreak affecting their network segment.
Escalate to the Service Provider (Last Resort)
If you’ve exhausted all personal troubleshooting and believe the block is a false positive affecting legitimate use (e.g., you’re a researcher using approved tools), you can sometimes appeal. Look for a "Contact Us" or "Support" link on the error page (it may be hidden in small print). Be prepared to provide:
- Your IP address (find it at whatismyipaddress.com).
- The exact time and date of the block.
- A clear, polite explanation of your legitimate use case.
- Proof you are not using automation (if applicable).
However, understand that for massive services like Google, direct human support for this specific issue is virtually non-existent for general users. This step is more viable for business customers or developers using APIs.
Proactive Measures: Staying Ahead of the Block
Adopt Smart Browsing and Research Habits
- Add Delays: If you’re manually doing repetitive searches or actions, consciously slow down. Pause 2-3 seconds between clicks or page loads.
- Use Official APIs: For data gathering or research, always use the official API (Application Programming Interface) provided by the service (e.g., Google Custom Search JSON API, Twitter API). These are designed for automated access and include authentication and rate limits that keep you compliant.
- Limit Open Tabs: Avoid having dozens of tabs from the same domain open simultaneously, especially if they are auto-refreshing.
- Use a Dedicated Browser Profile: For work involving research tools, create a separate browser profile with only necessary extensions. This isolates potential conflicts.
Secure Your Home Network Relentlessly
- Change Default Router Credentials: The admin username and password on your router should be unique and strong.
- Update Router Firmware Regularly: Enable automatic updates if available.
- Use a Strong Wi-Fi Password: Prevent neighbors or passersby from piggybacking on your network.
- Segment Your Network (Advanced): Some modern routers allow you to create separate network segments (VLANs) for IoT devices, guests, and primary computers. This can contain a potential infection.
For Businesses and Power Users: Consider a Static IP or Business-Grade Connection
If your work consistently involves legitimate automated access to web services (competitive analysis, SEO monitoring, data aggregation), a residential dynamic IP is a liability. Investing in:
- A business-class internet plan with a dedicated static IP address.
- A reputable business VPN with a dedicated, clean IP.
- Proxy services that provide private, authenticated IPs for web scraping.
These options provide a predictable, controllable IP reputation and are essential for scalable, reliable operations.
Implement Rate Limiting in Your Own Tools
If you are a developer building a tool that accesses third-party websites, you must implement rate limiting. This means programming your tool to make no more than 1-2 requests per second from a given IP and to respect robots.txt files. Use exponential back-off when you encounter a 429 (Too Many Requests) or CAPTCHA error. This ethical scraping practice protects both your tool’s functionality and the target website’s stability.
The Bigger Picture: Cybersecurity and Fair Use in the Digital Age
How These Systems Keep the Internet Safe and Fair
The "unusual traffic" detection is a frontline defense in a constant arms race against cybercrime. By filtering out bot traffic, these systems:
- Preserve Bandwidth and Server Costs: Websites, especially smaller ones, operate on tight margins. Bot traffic can drain resources meant for paying customers or readers.
- Thwart Fraud: Automated attacks are used to crack passwords, create fake accounts for spam, and manipulate online polls or reviews.
- Ensure Search Quality: Search engines like Google need to index the web efficiently. Aggressive scrapers can distort indexation and waste crawl budget, potentially harming the quality of search results for everyone.
- Maintain Platform Integrity: E-commerce sites, social media platforms, and ticketing services rely on these systems to prevent scalpers, fake engagement, and inventory hoarding.
The Delicate Balance: Security vs. Accessibility
This system isn’t perfect. It can create false positives, blocking legitimate users on shared networks or those using privacy tools. There’s an inherent tension between robust security and user accessibility. Services constantly tweak their algorithms to become smarter, using machine learning to better recognize nuanced human behavior patterns versus machine patterns. As a user, your best strategy is to be aware of the triggers and adopt habits that align with "human-like" interaction patterns. The goal is to be a good digital citizen: browse at a human pace, use official channels for automation, and secure your devices.
Conclusion: Knowledge is Your Best Defense
Encountering the "our systems have detected unusual traffic from your computer network" message is a momentary disruption, but it doesn’t have to be a mystery. By understanding that this is an automated security response to patterns that resemble bot activity, you empower yourself to methodically diagnose and solve the problem. Start with the simplest fixes: complete the CAPTCHA, restart your router to get a new IP, and disable any VPNs. If that fails, dig deeper into malware scans, browser extensions, and your network setup.
Ultimately, this message is a reminder of the complex, automated ecosystem that underpins our daily internet use. It highlights the importance of securing your personal network, being mindful of your own browsing patterns, and using the right tools for the job—especially when automation is involved. By adopting the proactive habits outlined here, you not only reduce your chances of seeing this block again but also contribute to a healthier, more secure internet for everyone. The next time this warning appears, you won’t see a frustrating dead end; you’ll see a clear, actionable checklist to get back online.