How To Create An NFS Share On CachyOS: A Complete Step-by-Step Guide
Have you ever wondered how to seamlessly share files and directories across multiple Linux machines on your home network or in a small office? If you're using the powerful, performance-optimized CachyOS distribution, the answer lies in mastering the Network File System (NFS). The simple command sequence cachyos create nfs share isn't a single built-in command, but it perfectly encapsulates the practical goal: leveraging CachyOS's robust architecture to set up a fast, efficient, and reliable NFS server. This comprehensive guide will transform that conceptual query into a concrete, actionable workflow, empowering you to share resources like never before.
Whether you're setting up a centralized media server for your smart TVs, creating a shared development environment for a team, or simply needing to access files from multiple computers without constant copying, NFS is the gold standard for Unix-like systems. CachyOS, with its Linux kernel optimizations and focus on performance, provides an excellent foundation for an NFS server that can handle demanding workloads. By the end of this article, you will not only know the exact commands but also understand the underlying principles, security considerations, and troubleshooting techniques to build a share that is both powerful and secure.
Understanding the Foundation: What is NFS and Why Use It on CachyOS?
Before diving into the cachyos create nfs share process, it's crucial to understand what you're building. The Network File System (NFS) is a distributed file system protocol originally developed by Sun Microsystems. It allows a client machine to access files over a network much like local storage is accessed. For the user, the remote directory appears as if it's mounted locally. This transparency is its greatest strength.
Why choose NFS for file sharing on CachyOS?
- Performance: Especially on a local area network (LAN), NFS version 4 (NFSv4) offers excellent speed with features like compound operations and stateful protocols. CachyOS's kernel optimizations can further enhance this throughput.
- Simplicity: Once configured, mounting shares is straightforward for clients. There's no need for complex user authentication at the share level (it relies on standard Linux UID/GID mapping).
- Maturity & Stability: NFS is a battle-tested protocol with decades of development. It's incredibly reliable for 24/7 operations.
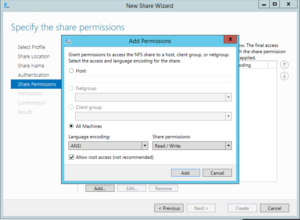
- Cross-Platform Support: While native to Linux/Unix, NFS clients are available for nearly every operating system, including Windows (via Services for NFS) and macOS.
However, NFS is not a silver bullet. Its primary security model in older versions (NFSv3) relied on IP address trust and insecure file handle handling. NFSv4 mandates strong security with Kerberos, but in a simple home lab setup, we often use a combination of firewall rules, no_root_squash caution, and network isolation. We will address security in depth.
Prerequisites: Preparing Your CachyOS System
You cannot simply run cachyos create nfs share as a magic command. You must first prepare your system by installing the necessary server components and ensuring your network is ready. This preparation phase is critical for a smooth setup.
- Lovecherryxo Of Leak
- Kannadamovierulzcom Download 2024
- Miles Okeeffe
- Was Jessica Tarlov Fired From Fox News
Installing the NFS Server Suite
CachyOS, being Arch-based, uses the pacman package manager. The NFS server functionality is provided by the nfs-utils package. Open your terminal and execute:
sudo pacman -S nfs-utils This single command installs the core daemons (rpcbind, nfs-server), management tools (exportfs, showmount), and configuration files. It's a lightweight installation with no unnecessary bloat, aligning perfectly with CachyOS's philosophy.
Verifying the Network Configuration
NFS operates over specific ports and requires proper network communication.
- Static IP Recommendation: For a server, it's highly recommended to assign a static IP address to your CachyOS machine. This can be done via your router's DHCP reservation or by configuring a static IP in CachyOS's network manager (e.g.,
systemd-networkdor NetworkManager). Your clients will need a reliable way to find the server. - Hostname Resolution: Ensure your server's hostname is resolvable by clients. The simplest method is editing the
/etc/hostsfile on every client machine, adding a line like:
Alternatively, set up a local DNS server if you have one.192.168.1.100 cachyos-server - Firewall Configuration: This is non-negotiable. You must allow NFS traffic through
iptables/nftablesorufw. For a basic setup allowing NFS from your local subnet (e.g.,192.168.1.0/24), withufw:
Forsudo ufw allow from 192.168.1.0/24 to any port nfsnftablesoriptables, you need to allow ports forrpcbind(111/tcp and udp),nfs(2049/tcp and udp), and themountdandstatdports (which can be fixed in/etc/nfs.conf). Usingufwor a similar front-end is easier for beginners.
The Core Configuration: Editing the Exports File
The heart of the cachyos create nfs share process is the /etc/exports file. This configuration file tells the NFS server which directories to share, with what permissions, and to which client hosts.
Understanding the /etc/exports Syntax
Each line in /etc/exports follows this structure:
<directory> <client1>(options) <client2>(options) ... <directory>: The absolute path to the folder you wish to share (e.g.,/srv/nfs/share).<client>: This can be a single IP address (e.g.,192.168.1.50), a hostname (e.g.,laptop), a network in CIDR notation (e.g.,192.168.1.0/24), or the wildcard*(insecure, use with extreme caution).(options): A comma-separated list of options that define access rights, security, and behavior. Common options include:rw: Read/write access.ro: Read-only access.sync: Writes must be committed to disk before returning success (safer, slightly slower). Always use this.no_subtree_check: Disables subtree checking, which improves reliability for shares that are the root of a filesystem or have many subdirectories. Highly recommended.no_root_squash: Allows the root user on the client to have root privileges on the share. Extremely dangerous on untrusted networks. Avoid unless in a completely isolated, trusted lab.all_squash: Maps all client users (including root) to the anonymousnobodyuser. Good for public, writeable shares.anonuid/anongid: Specify the UID/GID for the anonymous user when usingall_squash.sec: Security flavor. For simple setups,sys(AUTH_SYS) is default. For better security, considerkrb5(Kerberos) but it requires a KDC.
A Practical Example: Creating a Secure Shared Media Directory
Let's create a share for media files that your entire trusted home network can read, but only a specific user can write to.
Create the Share Directory and Set Permissions:
sudo mkdir -p /srv/nfs/media sudo chown -R mediauser:mediagroup /srv/nfs/media sudo chmod -R 775 /srv/nfs/mediaHere,
mediauseris a local user on your CachyOS server. We'll map client users to this UID.Edit
/etc/exports:
Open the file with your preferred editor (e.g.,sudo nano /etc/exports) and add:/srv/nfs/media 192.168.1.0/24(rw,sync,no_subtree_check,all_squash,anonuid=1001,anongid=1001)Breakdown of this line:
/srv/nfs/media: The directory to share.192.168.1.0/24: Any client on your local network.rw: Read/write.sync: Safe writes.no_subtree_check: Performance and reliability.all_squash: Maps all incoming client users (root or otherwise) to the anonymous user.anonuid=1001,anongid=1001: The anonymous user is mapped to UID 1001 and GID 1001, which should correspond to themediauserandmediagroupwe created. Find their UID/GID withid mediauser.
This setup means anyone on your network can read/write to the share, but all files created will be owned by
mediauseron the server, preventing arootuser on a client from creatingroot:rootowned files.Apply the Configuration:
After saving/etc/exports, you must tell the NFS server to re-read the file and apply the changes:sudo exportfs -ravThe
-rflag re-exports all directories,-aexports all directories listed in/etc/exports, and-vprovides verbose output.
Enabling and Starting the NFS Services
With the exports defined, you need to start the NFS server daemons. On CachyOS (and most modern systemd-based distributions), this is managed via systemd.
Enable and Start the Main NFS Server Service:
sudo systemctl enable --now nfs-serverThe
--nowflag starts it immediately and enables it to start on boot.Check Service Status:
sudo systemctl status nfs-serverYou should see it
active (running). Thenfs-serverservice automatically starts and manages the requiredrpcbindservice as a dependency.Verify Exports are Active:
sudo exportfs -sThis command shows a summary of all currently exported filesystems and their options. You should see your
/srv/nfs/mediaentry with the options you specified.
The Client-Side: Mounting the NFS Share on CachyOS (or Other Linux)
Now that your CachyOS server is sharing, it's time to mount that share on a client. We'll use another CachyOS machine as the client example.
Temporary Mount (For Testing)
First, test the connection without making it permanent.
- Install NFS client utilities (if not present):
sudo pacman -S nfs-utils - Create a local mount point:
sudo mkdir -p /mnt/media_share - Mount the share:
Replacesudo mount -t nfs cachyos-server:/srv/nfs/media /mnt/media_sharecachyos-serverwith your server's IP or hostname. - Test It:
Thels -la /mnt/media_share touch /mnt/media_share/test.txt ls -la /mnt/media_sharetest.txtfile should be owned by UID 1001 (mediauser), proving theall_squash,anonuidmapping works.
Permanent Mount with /etc/fstab
For a share that mounts automatically at boot, edit the client's /etc/fstab file.
Add this line:
cachyos-server:/srv/nfs/media /mnt/media_share nfs defaults,_netdev,auto 0 0 Key options explained:
defaults: Usesrw,suid,dev,exec,auto,nouser,async._netdev: Crucial. Tells systemd the mount requires a network. It will wait for the network to be online before attempting the mount, preventing boot failures.auto: Mount automatically at boot (implied bydefaults, but good to be explicit in fstab context).
After saving /etc/fstab, test the configuration without rebooting:
sudo mount -a If no errors appear, your permanent mount is configured correctly.
Advanced Configuration & Optimization for CachyOS
To truly harness the power of your CachyOS NFS server, consider these advanced tweaks.
Tuning NFS Performance in /etc/nfs.conf
CachyOS's kernel is tuned for low latency. You can align NFS settings. Edit /etc/nfs.conf on the server.
Under [nfsd], you can adjust:
[nfsd] # Increase the number of NFS server threads. A good starting point is 8-16. threads=16 # Enable NFSv4 by default (usually on by default) vers4=y Under [nfs] on the client, you can set:
[nfs] # Set the default NFS version to try (4, 4.1, 4.2) # Setting to 4.2 enables features like pNFS if supported. vers=4.2 After changes, restart nfs-server on the server.
Using NFSv4.2 Features (pNFS, Space Reservation)
If all your clients and the server support NFSv4.2, you gain powerful features:
- pNFS (Parallel NFS): Allows data to be transferred in parallel across multiple network paths or storage devices. Relevant for very high-performance clusters.
- Space Reservation (
rsize/wsize): Whilersizeandwsizeare also used in v3, v4 handles them more efficiently. You can set them in the mount options on the client (e.g.,rsize=32768,wsize=32768). Experiment with values like65536for maximum throughput on a reliable LAN.
Securing Your Share: Beyond Basic Trust
For shares exposed beyond a single, physically secured LAN, you must implement stronger security.
- Kerberos (NFSv4 with
sec=krb5): This is the enterprise-grade method. It requires setting up a Kerberos Key Distribution Center (KDC) likekrb5orFreeIPA. This is complex and beyond a simple home setup but is the correct way to secure NFS in a domain environment. - Network-Level Security: The most effective simple security is network isolation. Place your NFS server and clients on a dedicated VLAN or physically separate network segment. Use firewall rules to restrict port 2049 (and related RPC ports) to only the specific IPs of your clients.
- Avoid
no_root_squash: Never use this option unless you have absolute control and trust over every client machine and user. A compromised client with root access could then have unrestricted root access to your NFS share.
Troubleshooting Common "cachyos create nfs share" Issues
Even with careful setup, issues can arise. Here’s a diagnostic checklist.
"mount.nfs: access denied by server" or "Permission denied"
- Check
/etc/exportssyntax and directory path. Runsudo exportfs -ravand check for errors. - Verify client IP matches the export rule. Use
showmount -e cachyos-serverfrom the client to see what shares the server is actually exporting. If your share isn't listed, the server's/etc/exportsisn't configured for your client's IP. - Check UID/GID mapping. If files appear with
nobody:nobodyor strange UIDs on the client, yourall_squash/anonuidmapping or default mapping is incorrect. Ensure the UID/GID exists on both server and client for consistent ownership.
"mount.nfs: Connection timed out" or "No route to host"
- Ping the server.
ping cachyos-server. If this fails, you have a basic network issue (wrong IP, server down, firewall blocking ICMP). - Check server firewall. Ensure ports 111 (rpcbind), 2049 (nfs), and the mountd/statd ports are open for the client's IP. Use
sudo ss -tulpn | grep :2049on the server to confirmrpc.mountdandrpc.nfsdare listening. - Check
rpcbindservice. Ensurerpcbindis running on the server:sudo systemctl status rpcbind.
Slow Performance or Stalls
- Use
syncvsasync. You should be usingsyncfor data integrity. If performance is critical and you accept risk of corruption on crash,asyncis faster but not recommended. - Adjust
rsizeandwsize. On the client mount options, tryrsize=32768,wsize=32768or even65536. Test withdd if=/dev/zero of=/mnt/share/test bs=1M count=1024 oflag=direct. - Check network infrastructure. A bad cable, switch port, or Wi-Fi connection will cripple NFS. Use a wired connection for best results.
- Verify
no_subtree_checkis set. This option eliminates a significant performance overhead.
Comparing NFS with Samba (SMB) for CachyOS
A common point of confusion is whether to use NFS or Samba for file sharing. Here’s a quick comparison in the context of a CachyOS setup:
| Feature | NFS (on CachyOS) | Samba (SMB) |
|---|---|---|
| Primary Use Case | Linux/Unix-to-Linux/Unix sharing. Native, fast, simple. | Cross-platform sharing (Windows, macOS, Linux). |
| Performance | Generally faster on a Linux-only LAN due to simpler protocol. | Slightly higher overhead, but excellent with modern versions (SMB3). |
| Authentication | Relies on host/IP trust and UID/GID mapping. Simple, less granular. | User/password-based (integrated with Windows AD/LDAP). More granular per-user control. |
| Ease of Setup | Very simple for a trusted network. Edit /etc/exports. | More complex configuration (smb.conf), user management (smbpasswd). |
| Security Model | Network-based (firewall) + UID mapping. NFSv4+Kerberos is strong. | Stronger built-in user authentication and encryption (SMB3). |
| Best For | CachyOS/Linux clusters, home labs, media servers (Plex/Jellyfin backend), development shares. | Mixed-OS environments (Windows clients), shares needing per-user passwords, replacing a Windows Server file share. |
Verdict for CachyOS: If all your clients are Linux-based (other CachyOS, Ubuntu, etc.) and you control the network, NFS is the superior, simpler, and higher-performance choice. Use Samba if you have Windows or macOS clients that need seamless, password-protected access.
Conclusion: Your CachyOS NFS Share is Live
You have now traversed the entire journey from the initial question "how to cachyos create nfs share" to a fully operational, secure, and performant NFS server. You've installed nfs-utils, meticulously crafted your /etc/exports file with security-conscious options, started the nfs-server service, and successfully mounted the share on a client machine.
Remember the core principles: security through network isolation and careful UID mapping, reliability through the sync option, and performance through no_subtree_check and appropriate rsize/wsize tuning. Your CachyOS system, with its performance-oriented kernel, is now a robust hub for file sharing, capable of serving media to multiple devices, synchronizing project files across workstations, or acting as the storage backbone for a small-scale container cluster.
The power of NFS on CachyOS lies in its simplicity and speed. By following this guide, you've unlocked a fundamental Linux networking capability that scales from a single-room Raspberry Pi cluster to enterprise-grade storage servers. Now, go ahead, mount that share on your laptop, your media player, and your development box, and experience the seamless, network-transparent storage you've just built.