Secure Boot Enable But Not Active: Decoding The Silent Security Gap
Have you ever peered into your computer's UEFI/BIOS settings, only to see the cryptic message "Secure Boot Enable but Not Active" and wondered what it truly means? You’re not alone. This seemingly contradictory state confounds even tech-savvy users, leaving a critical security feature in a limbo—turned on in theory, but disabled in practice. It’s like having a locked door with the key still in the lock on the outside; the intention is security, but the execution is flawed. This comprehensive guide will dismantle the mystery of this status, explore why it happens, the significant risks it poses, and provide you with a clear, actionable roadmap to resolve it and fortify your system's defenses.
Understanding the Paradox: What "Secure Boot Enable But Not Active" Really Means
To grasp this paradox, we must first understand Secure Boot itself. Secure Boot is a foundational security standard within the UEFI (Unified Extensible Firmware Interface) specification. Its primary job is to ensure that only trusted, signed operating system bootloaders and critical firmware components can execute during your computer's startup sequence. It creates a chain of trust, starting from the firmware, preventing malware like rootkits from hijacking the boot process before the operating system even loads.
When your firmware displays "Secure Boot Enable but Not Active," it’s communicating a specific state: the Secure Boot policy is enabled in the firmware settings, but the enforcement mechanism is currently inactive. Think of it like setting an alarm system to "Armed" but then removing the batteries from the sensors. The system is configured to be secure, but a critical component is missing or invalid, so it cannot function. The most common reason for this state is the absence of valid, trusted Platform Key (PK) and Key Exchange Key (KEK) databases in the firmware's non-volatile memory (NVRAM). Without these cryptographic keys, Secure Boot has nothing to verify against, so it gracefully disables itself, reporting this "enable but not active" status.
This state is not a firmware bug; it's a deliberate safety feature. UEFI specifications mandate that if the necessary key databases are missing or corrupted, Secure Boot must not enforce validation, as it would prevent any operating system from booting, rendering your PC unusable. The firmware chooses a "fail-open" (insecure but bootable) over a "fail-closed" (secure but unbootable) scenario. This design philosophy prioritizes user access but creates a dangerous window of vulnerability.
The Root Causes: Why Does This Status Appear?
Several scenarios can lead to this insecure limbo. Understanding the cause is the first step toward the solution.
1. Factory Defaults and OEM Installations
Many computers, especially those from major manufacturers (OEMs like Dell, HP, Lenovo), ship with Secure Boot disabled by default. However, some newer models, particularly those intended for business or Windows 11 compatibility, may have the Secure Boot policy pre-enabled in the firmware menu, but without the necessary Microsoft-signed keys installed. The firmware is "ready" but not "armed." Users who never enter the firmware settings to activate it properly remain in this vulnerable state.
2. Manual Clearing of Secure Boot Keys
A user or technician might have manually enrolled or reset the Secure Boot keys through the firmware's "Key Management" or "Secure Boot" menu. Options like "Clear Secure Boot Keys" or "Restore Factory Keys" can sometimes leave the PK and KEK databases empty if the restore process fails or is interrupted. The policy flag remains set to "Enable," but the key stores are blank.
3. Failed or Incomplete OS Installation
During a clean installation of an operating system like Windows or a Linux distribution, the installer is responsible for writing the appropriate Secure Boot keys (often the Microsoft KEK for Windows, or a distribution-specific key for Linux) into the firmware. If this process is interrupted—due to a power loss, a forced restart, or a disk error—the installer may have toggled the policy to "Enable" but failed to write the keys. The result is a system that thinks it should be using Secure Boot but lacks the tools to do so.
4. Motherboard CMOS/BIOS Battery Failure
The firmware settings, including Secure Boot keys and policy flags, are stored in CMOS memory powered by a small battery on the motherboard. If this battery dies, the CMOS memory clears, resetting all firmware settings to factory defaults. On a system where the default was "Secure Boot Enable" (policy on) but with no keys provisioned, you will boot to this "Enable but Not Active" state. You'll also lose custom boot orders, overclocking settings, and other configured preferences.
5. Corrupted Firmware or Failed Update
A failed UEFI firmware update can corrupt the NVRAM region where Secure Boot keys are stored. The firmware might recover by disabling key enforcement but leaving the policy bit enabled, again resulting in this mixed status.
The Hidden Danger: Security Implications of an Inactive Secure Boot
You might think, "If it's not active, isn't it just like it was never there?" The answer is both yes and no, and the "yes" part is the problem. While the system is not benefiting from Secure Boot's protection, the mere presence of the "Enable" policy flag creates a false sense of security. Users and even some IT administrators might see the word "Enable" and assume the system is protected, when in reality, it is more vulnerable than if Secure Boot were fully disabled and clearly labeled as such.
Here’s why the "Enable but Not Active" state is a significant security gap:
- No Protection Against Bootkits: Malicious software like bootkits (e.g., Mebromi, Nimnul) and rootkits that target the Master Boot Record (MBR) or the UEFI bootloader can install themselves with impunity. Without key validation, the firmware will execute any code presented to it at boot time.
- Bypassing Disk Encryption: For systems using full-disk encryption (like BitLocker on Windows or LUKS on Linux), the bootloader is a critical part of the trusted chain. A compromised bootloader can capture the encryption keys or passwords as they are entered, rendering disk encryption moot. Secure Boot helps ensure the bootloader itself is genuine.
- Persistence and Stealth: UEFI-based malware can be exceptionally persistent, surviving OS reinstalls and disk formatting by residing in the firmware's flash memory itself. An inactive Secure Boot does nothing to prevent this firmware-level infection.
- Compliance and Audit Failures: For businesses and organizations, security standards like NIST SP 800-171, CIS Benchmarks, and Microsoft's Windows 11 requirements mandate that Secure Boot be enabled and active. A system in this "enable but not active" state will fail security audits and compliance scans, potentially violating regulations and leaving the organization non-compliant.
According to data from cybersecurity firms, bootkit attacks, while less common than ransomware, are on a concerning upward trend due to their high effectiveness and stealth. A 2023 report by SentinelOne highlighted a 50% year-over-year increase in firmware and bootkit threats, underscoring that leaving this foundational security layer non-functional is a gamble with increasingly high stakes.
Diagnosing the Problem: How to Confirm Your Secure Boot Status
Before you can fix the issue, you need to confirm it exists and understand your system's specific configuration. The diagnostic process varies slightly by operating system.
On Windows 10 & 11
- Press
Win + R, typemsinfo32, and press Enter. - In the System Information window, locate the "Secure Boot State" item.
- You will likely see it listed as "Enabled" but with a note or a separate field saying "Secure Boot is not active" or simply see "Enabled" while the "Secure Boot State" reads "Unsupported" or "Disabled." The key is the mismatch. If it says "Secure Boot State: On", it is active and working. If it says "Secure Boot State: Off" while the firmware setting is "Enable," you've found the issue.
- For a more technical view, open PowerShell as Administrator and run the command:
If it returnsConfirm-SecureBootUEFITrue, Secure Boot is active. If it returnsFalseor an error, it is not active, and you should check your firmware settings.
On Linux (Using systemd-boot or GRUB)
- Open a terminal.
- Run the command:
mokutil --sb-state - This will output either
SecureBoot enabled(good) orSecureBoot disabled(problem). If it's disabled, you must check your firmware.
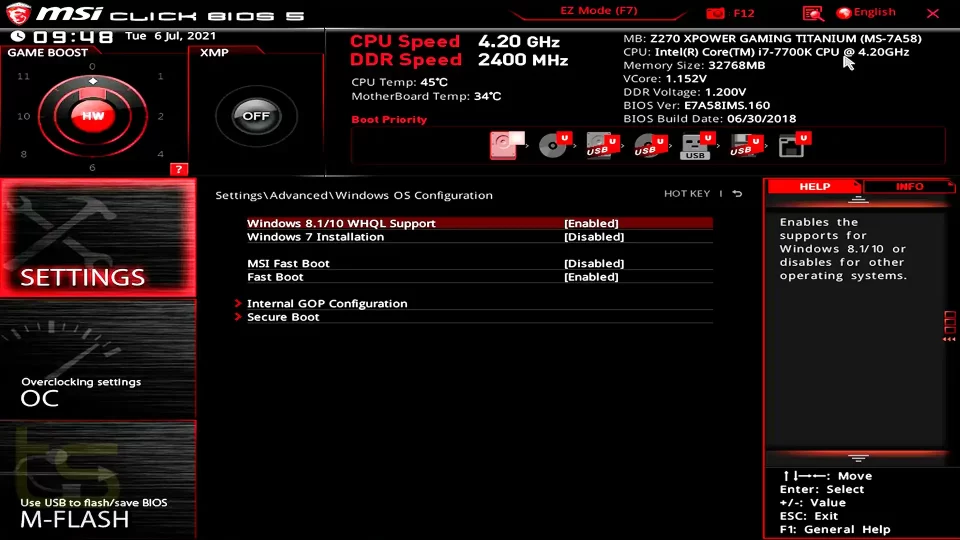
The Definitive Check: Entering UEFI/BIOS Setup
This is the ultimate source of truth.
- Restart your computer and press the appropriate key (Del, F2, F10, F12, or Esc—varies by manufacturer) to enter the UEFI/BIOS setup utility.
- Navigate to the "Boot" or "Security" tab.
- Find the "Secure Boot" option. You will see its status. It may say:
- Enabled (This is the policy flag. It's on).
- Active or On (This is the enforcement state. If missing, it's inactive).
- Look for a sub-menu like "Key Management" or "Secure Boot Keys". Enter it. You will see the list of installed keys: PK (Platform Key), KEK (Key Exchange Key), db (Signature Database), and dbx (Forbidden Signature Database). If these lists are empty or say "Not Enrolled," that is the root cause. The policy is enabled, but there are no keys to enforce it.
The Resolution Pathway: Activating Your Secure Boot
Fixing this issue requires writing the necessary trusted keys into your firmware's Secure Boot databases. The method depends on your operating system and whether you want to use the default Microsoft keys (for Windows and most Linux distros) or manage custom keys.
Method 1: The Standard Fix for Windows Systems (Restore Factory Keys)
This is the most straightforward method for Windows PCs, especially those from OEMs.
- Enter your UEFI/BIOS setup (as described above).
- Navigate to the Secure Boot or Key Management menu.
- Look for an option called:
- "Restore Factory Keys"
- "Load Factory Defaults" (specifically for Secure Boot)
- "Reset to Setup Mode" (this is the opposite—don't use this unless you want to disable Secure Boot).
- Select "Restore Factory Keys" or its equivalent. This option is designed to write the original, vendor-signed Microsoft KEK and Platform Key that the OEM installed at the factory.
- Save changes and exit (
F10usually). - The system will reboot. Re-enter the firmware setup and check the Key Management screen again. You should now see entries in the PK and KEK fields. The Secure Boot State should now read "Active" or "On" in both the firmware and Windows'
msinfo32.
Method 2: For Linux or Custom Setups (Enrolling Your Own Keys)
If you're running a Linux distribution or want to use custom keys, you need to enroll them manually.
- For most mainstream Linux distros (Ubuntu, Fedora, Debian, etc.): They are signed with keys that are already in the db (Signature Database) if your system's KEK chain trusts the Microsoft UEFI CA (which is the default on most consumer PCs). Therefore, Method 1 (Restore Factory Keys) is usually sufficient. The distro's bootloader shim is signed by a key in the db, which is signed by the Microsoft KEK, which is signed by your Platform Key. Restoring the factory keys completes this chain.
- For custom kernels or self-signed bootloaders: You must enroll your own keys.
- Generate your own PK, KEK, and db keys using the
certutiloropenssltools. - In the UEFI setup's Key Management menu, you will have options to "Enroll Key" or "Add New Key."
- You will need to provide the key file (usually a
.ceror.crtfile) and specify which database it belongs to (PK, KEK, db). - Warning: This process is advanced. Losing your Platform Key can permanently brick your motherboard's ability to boot, requiring a hardware flash recovery. Most users should stick to the factory keys.
- Generate your own PK, KEK, and db keys using the
Method 3: Using the Windows Recovery Environment (If You Can't Boot)
If your system won't boot because you messed with Secure Boot keys, you'll need a Windows Installation USB/DVD.
- Boot from the Windows media.
- On the "Install Windows" screen, click "Repair your computer" > "Troubleshoot" > "Advanced Options" > "UEFI Firmware Settings".
- This will reboot you directly into the UEFI setup. From here, perform Method 1 (Restore Factory Keys).
- Save and exit. The system should now boot normally.
Best Practices and Proactive Measures
Once you've activated Secure Boot, maintain its integrity with these practices:
- Never Disable Secure Boot Unless Absolutely Necessary: Some older hardware or niche software (like certain overclocking tools, legacy PCIe device ROMs, or dual-booting with very old operating systems) may require Secure Boot to be disabled. If you must disable it, be aware you are lowering your system's security posture. Re-enable it as soon as the incompatibility is resolved.
- Keep Your UEFI Firmware Updated: Motherboard manufacturers release updates that often include updated Secure Boot databases (e.g., adding new Microsoft Windows Production CA keys) and security patches. Regularly check your manufacturer's website for updates.
- Understand the "Setup Mode" vs. "User Mode": When you clear all keys, Secure Boot enters "Setup Mode," where you can enroll keys but no validation occurs. "User Mode" is when keys are present and validation is active. Your goal is always to be in User Mode with valid keys.
- For System Builders and Enthusiasts: If you build your own PC, the motherboard will typically have Secure Boot disabled by default. You must enter the firmware and enable it. Most modern boards will automatically enroll the necessary Microsoft keys when you first enable it, or provide a "Restore Factory Keys" option. Consult your motherboard manual.
- Document Custom Key Setups: If you manage a fleet of machines with custom keys, maintain a secure, backed-up copy of all key files and the enrollment procedure. Losing the Platform Key is catastrophic.
Addressing Common Questions and Edge Cases
Q: I restored factory keys, but Secure Boot is still not active. What now?
A: This suggests a deeper firmware issue. Try a full CMOS clear (power off, unplug, remove the CMOS battery for 5 minutes, reinstall). This resets all firmware settings. On boot, re-enter setup, re-enable Secure Boot (it may be off after the clear), and then restore factory keys. If it still fails, your firmware's NVRAM storing the key databases may be corrupted, and a firmware re-flash using the manufacturer's official tool (often from a USB drive in a recovery mode) may be necessary.
Q: My system says "Secure Boot is Enabled" in Windows msinfo32, but I don't see the "Not Active" warning. Is it safe?
A: If msinfo32 says "Secure Boot State: On", then it is active and working correctly. The "Enable but Not Active" state specifically shows as "Secure Boot State: Off" or "Unsupported" while the firmware setting reads "Enable." Trust the msinfo32 output for the final state.
Q: Does this affect older BIOS-based systems?
A: No. Secure Boot is a UEFI-only feature. If your system uses a legacy BIOS (often indicated by the lack of a "UEFI/Legacy" boot mode option in firmware), it does not have Secure Boot at all. The message you're seeing is exclusive to UEFI firmware.
Q: I'm dual-booting Windows 11 and Linux. Will activating Secure Boot break Linux?
A: For most mainstream distributions (Ubuntu, Fedora, openSUSE, Debian), no. Their bootloaders are signed by keys that chain back to the Microsoft UEFI CA, which is trusted by the default factory keys. As long as you use the distribution's standard bootloader (GRUB with shim), it will work. For more exotic or custom Linux setups, you may need to enroll your own Linux distribution's key into the db (Signature Database), which is a more advanced procedure.
Conclusion: Turning a Silent Warning into Robust Security
The "Secure Boot Enable but Not Active" status is more than a quirky firmware message; it's a critical security warning light that is all too often ignored. It represents a fundamental break in the chain of trust that protects your system's most vulnerable moment: the boot process. While the firmware's fail-safe design prevents a total lockout, it inadvertently creates a period of maximum vulnerability where sophisticated malware can gain a persistent, deep-rooted foothold.
Resolving this issue is not a complex, hours-long ordeal for the vast majority of users. It is a five-minute task involving a trip into your UEFI settings and clicking "Restore Factory Keys." The return on that minimal investment is immense: you restore a vital layer of defense against bootkits, rootkits, and firmware-based attacks. It ensures compliance with modern security standards and, for Windows 11 users, satisfies a mandatory system requirement.
Do not be lulled into complacency by the word "Enable" in that status message. Take action today. Reboot, enter your firmware, and verify your Secure Boot keys. Activate them. Confirm they are active. In the ongoing battle for digital security, securing the boot process is not a optional upgrade—it is the essential foundation upon which all other protections are built. Make sure your foundation is solid.
![How to Enable Secure Boot Without BIOS [Complete Guide]](https://10pcg.com/wp-content/uploads/bios-secure-boot-on-300x176.jpg)