Decoding "Verifying You Are Human. This May Take A Few Seconds.": The Invisible Shield Of The Internet
Have you ever been mid-task online—trying to book a concert ticket, submit a form, or simply log in—only to be halted by the iconic, slightly frustrating message: "Verifying you are human. This may take a few seconds."? You stare at the spinning wheel or the grid of blurry storefronts, wondering what mysterious digital ritual is unfolding behind the scenes. Is it scanning your soul? Is it judging your ability to pick crosswalks? What actually happens during those few seconds, and why does the internet insist on this pause? This message is the frontline greeting of a silent, global war against bots, and understanding it is key to navigating our secure, yet often irritating, digital world.
This process, commonly known as a CAPTCHA or human verification challenge, is far more than a simple annoyance. It’s a sophisticated, ever-evolving security measure designed to distinguish genuine users from automated scripts and malicious bots. Those "few seconds" represent a complex handshake between your browser and a security provider's server, involving behavioral analysis, risk assessment, and sometimes, a tiny puzzle for you to solve. While it can disrupt our flow, its purpose is to protect the integrity of websites, prevent fraud, and safeguard our personal data from large-scale automated attacks. Let’s pull back the curtain on this ubiquitous digital checkpoint and explore the technology, the reasons for the delay, and what the future holds for proving you’re not a robot.
What "Verifying You Are Human" Actually Means
At its core, the prompt "Verifying you are human" is a request for proof. The internet is flooded with automated traffic—estimates suggest bots account for nearly 40% of all web traffic. These range from harmless search engine crawlers to destructive spam bots, credential Stuffers, and scalper bots that snap up limited inventory. Websites need a way to let legitimate humans in while keeping this digital horde at bay. The verification is that gatekeeper.
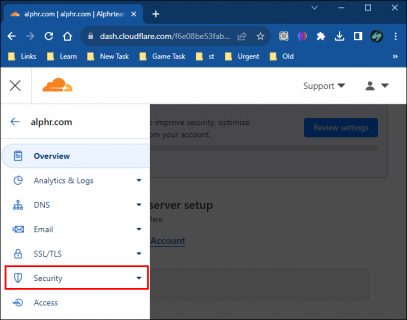
The term CAPTCHA is an acronym for "Completely Automated Public Turing test to tell Computers and Humans Apart." Coined in 2000, it was initially a simple test of human cognitive abilities that were presumed difficult for machines, like reading distorted text. The modern iteration, often powered by services like Google's reCAPTCHA, hCaptcha, or Cloudflare's Turnstile, has evolved dramatically. It’s less about challenging you and more about observing you. The system analyzes a myriad of signals—your mouse movements, typing cadence, browser history, IP reputation, and interaction patterns—to assign a risk score. The message you see is often the final step in this invisible analysis, a confirmation that the system’s confidence has crossed a threshold, or a request for a final, explicit signal if doubt remains.
This shift from explicit puzzles to implicit, risk-based analysis is why you sometimes breeze through with just a checkbox, and other times face a grid of traffic lights. The system is dynamically adjusting the challenge based on the perceived threat level of the interaction. A login from a known device on a familiar network might get an easy pass, while a sign-up from a new country using a VPN might trigger a more rigorous check.
The Intricate Technology Powering Those "Few Seconds"
So, what is happening during those "few seconds"? It’s a rapid-fire exchange of data and analysis. When you encounter a verification prompt, your browser sends a token—a small piece of data—to the verification service's server (e.g., Google for reCAPTCHA). This token contains encrypted information about your interaction with the page up to that point.
The server then performs a multi-layered risk assessment:
- Behavioral Biometrics: Did your cursor move to the checkbox in a smooth, human-like arc, or did it teleport? Did you click with variable pressure and timing? Humans exhibit micro-movements and inconsistencies that bots typically lack.
- Device and Browser Fingerprinting: It checks for signs of automation. Is the browser instance headless (without a graphical interface, common for bots)? Are there unusual plugins or inconsistencies in the browser's reported properties?
- IP and Network Analysis: Is the IP address from a data center known for bot activity? Is it a residential proxy? The reputation of the network is a major factor.
- Historical Interaction: Have you successfully verified this site or similar sites before? Services build anonymous profiles of trust based on past verified human activity.
If the risk score is high (e.g., likely human), the service instantly returns a "pass" token to the website, and you proceed. If the score is low or ambiguous, it escalates to an explicit challenge. This is where you see the image selection ("select all squares with a storefront") or the audio challenge. Your response to this challenge is then analyzed for correctness and, crucially, for the manner of your response. A human might hesitate slightly on a tricky image; a bot might answer with superhuman, uniform speed. The entire process, from initial token to final verdict, is designed to happen in under 500 milliseconds on a good connection. The "few seconds" you perceive is often the cumulative time of multiple attempts, network latency, or a complex puzzle that genuinely requires your visual processing.
Why the Verification Sometimes Takes "A Few Seconds" (And Sometimes Much Longer)
The promise of "a few seconds" is a best-case scenario. Several factors can extend that wait into a frustrating minute or more:
- Network Latency and Server Load: Your request has to travel to the verification service's server and back. If the service is under heavy attack (a DDoS event) or simply experiencing high global traffic, response times slow down. A slow internet connection on your end exacerbates this.
- Challenge Complexity: Not all image grids are created equal. Some use high-resolution, ambiguous images that require careful scrutiny. The "select all buses" challenge becomes harder when buses are partially obscured, at odd angles, or in poor lighting. The system may also present multiple rounds if your first attempt is deemed insufficient.
- Accessibility Tools: If you're using a screen reader or other assistive technology, the process often defaults to the audio challenge, which can take longer to listen to and process. Some services also deliberately introduce delays to prevent timing-based bot attacks.
- Geolocation and Proxy Issues: Traffic routed through a VPN or proxy, especially one with a poor reputation, is automatically flagged for higher scrutiny. This can trigger multiple, sequential challenges as the system tries to find a pattern it can trust.
- Browser and Device Factors: Outdated browsers, disabled JavaScript (which many verification scripts require), or privacy extensions that block tracking scripts can interfere with the silent, behavioral analysis phase, forcing the system to rely on slower, explicit tests.
Understanding these factors can help troubleshoot. If you're consistently facing long waits, try switching from a VPN, ensuring JavaScript is enabled, updating your browser, or moving to a stronger Wi-Fi signal.
The Most Common Types of Human Verification You'll Encounter
The landscape of human verification is diverse, each type with its own strengths and user experience trade-offs.
1. Image-Based Selection (The Classic Grid): This is the most recognizable. You're shown images and asked to select those matching a criterion (e.g., "select all squares with a traffic light"). It tests visual perception and common sense. Pros: Intuitive for most humans. Cons: Can be problematic for visually impaired users, culturally biased (e.g., recognizing specific storefronts or vehicles), and increasingly challenged by advanced AI image recognition.
2. The Simple Checkbox ("I'm not a robot"): This is often the result of a successful invisible analysis. Clicking it may trigger a quick, behind-the-scenes check. If your behavioral signals are strong, you pass instantly. Pros: Fast, seamless for low-risk users. Cons: Can be a red flag for bots that mimic mouse movements, though advanced systems analyze the click itself.
3. Audio Challenges: An alternative for the visually impaired, playing a sequence of numbers or letters amidst background noise that you must type. Pros: Essential for accessibility compliance (WCAG). Cons: Can be difficult in noisy environments, for those with hearing impairments, or with non-Latin alphabets.
4. Invisible/Passive Verification (reCAPTCHA v3, Turnstile): This is the holy grail of user experience. There is no widget, no checkbox, no puzzle. The service runs silently in the background, analyzing your entire session behavior and returning a continuous risk score (from 0.0 to 1.0) to the website. The site then decides, based on its own threshold, whether to allow the action, challenge you, or block the request. Pros: Zero user friction. Cons: Completely opaque to the user; raises more privacy questions about background data collection.
5. SMS/Phone Verification: A code is sent to your mobile phone, which you must enter. This ties the verification to a physical, personal device and phone number. Pros: Very strong proof of a unique, reachable human. Cons: Requires a phone number, incurs potential costs, and is vulnerable to SIM-swap attacks.
6. Biometric Verification (Emerging): Using device-native features like fingerprint scanners or facial recognition (e.g., Apple's Face ID) to confirm presence. Pros: Extremely accurate and fast. Cons: Requires compatible hardware, raises significant privacy and data storage concerns, and is not universally accessible.
The User Experience: Balancing Security with Sanity
The collective groan when a CAPTCHA appears is a testament to a fundamental tension in security: usability versus protection. While necessary, poorly implemented verification can be a major point of friction, leading to abandoned carts, failed form submissions, and user frustration. Common pain points include:
- Ambiguous Images: "Is this a mountain or a hill? Is that a motorcycle or a bicycle?" These subjective challenges can cause multiple failures.
- Accessibility Failures: Many image-based CAPTCHAs are incompatible with screen readers, excluding blind and low-vision users unless an audio alternative is perfectly implemented.
- Repetitive Challenges: Being asked to verify multiple times on the same site during a single session feels punitive and indicates a poorly tuned risk model.
- Mobile Difficulties: Small touch targets on image grids are prone to mis-taps, and the audio challenge is hard to hear without headphones in public.
Actionable Tips for Users:
- Ensure Good Lighting & Focus: For image challenges, a clear screen helps.
- Use a Stable Network: A flaky connection can cause timeouts and restarts.
- Check for Accessibility Options: Look for the audio or accessibility icon (often a circle with an "a" or headphones) if you struggle with visuals.
- Consider Your Privacy Tools: If you use aggressive ad/tracker blockers, they might interfere. Temporarily whitelist a trusted site if you're having persistent issues.
- Be Patient with Multiple Attempts: The system may be calibrating its trust. One wrong click doesn't mean you've failed forever; it just adjusts its parameters.
For website owners, the solution lies in choosing modern, adaptive providers (like hCaptcha or Turnstile) that prioritize invisible verification and accessibility, and in tuning the sensitivity thresholds to match their actual bot threat level—not using a sledgehammer to crack a nut.
The Critical Security Perspective: Why We Can't Just Turn It Off
It's easy to view the verification prompt as an inconvenience imposed by faceless corporations. But the reality is stark: without these checks, the modern internet as we know it would collapse under the weight of automated abuse. Consider the attack vectors they block:
- Credential Stuffing: Bots use lists of stolen usernames/passwords to try logging into thousands of sites per minute. Verification stops automated login attempts.
- Scalping & Inventory Hoarding: Bots snap up concert tickets, sneakers, and PS5s within seconds, inflating prices on resale markets.
- Spam and Fraudulent Account Creation: Mass creation of fake social media, email, and forum accounts for disinformation, phishing, and scam campaigns.
- Scraping and Price Gouging: Bots scrape pricing and inventory data from e-commerce sites to undercut competitors or monitor for deals.
- DDoS and Resource Abuse: Bots can flood contact forms, poll APIs, or exploit "forgot password" features to lock out real users or incur SMS/email costs for the site owner.
According to cybersecurity firm Imperva's 2023 report, bad bot traffic increased by 27% year-over-year, with sophisticated, evasive bots now making up over 50% of all bot traffic. These aren't just dumb scripts; they can solve simple CAPTCHAs, mimic human mouse movements, and rotate through millions of IP addresses. The "human verification" you experience is the last line of defense, the moment where a site says, "I need to be absolutely sure this is a person before I grant access to this valuable resource or personal account." The few seconds of your time are a tiny price to pay for preventing systemic fraud, data theft, and service degradation.
The Future of Human Verification: Seamless, Private, and Invisible
The trajectory is clear: the goal is to make verification completely invisible and frictionless for legitimate users while becoming impenetrable to bots. Several trends are accelerating this:
- Advanced Behavioral Biometrics: Moving beyond mouse movements to analyze typing rhythm, device tilt (via accelerometer), and even subtle interaction patterns unique to a user over time. Your device itself becomes the proof of humanity.
- Privacy-Preserving Models: Newer solutions like Cloudflare Turnstile and next-gen reCAPTCHA are designed to minimize personal data sent to the verification service, using cryptographic proofs and local analysis to prove "human-ness" without creating a detailed user profile.
- Continuous Authentication: Instead of a one-time checkpoint, systems will constantly and silently assess risk during a session. A sudden switch in behavior (e.g., a user who slowly scrolls suddenly tries to rapidly submit 50 forms) would trigger a step-up challenge.
- Hardware-Backed Attestation: Leveraging the secure enclaves in modern smartphones and computers (like Apple's Secure Enclave or Android's Titan M) to cryptographically prove that a request is coming from a genuine, unmodified human-operated device.
- The Death of the Distorted Text: Image-based puzzles are on the way out. They are poor for accessibility, vulnerable to AI, and create a terrible user experience. The future is passive analysis and, where needed, tasks that are trivial for humans but nuanced for machines (e.g., "tap in the order shown" on a rotating 3D object).
The ideal future state is one where you never see a "verifying you are human" message again, not because security has been abandoned, but because the verification has become so intelligent, contextual, and integrated that it happens without your conscious participation—a silent, trustworthy handshake between your device and the service you're using.
Conclusion: Embracing the Necessary Pause
The next time that familiar message—"Verifying you are human. This may take a few seconds."—appears on your screen, take a breath. Those few seconds are not a digital timeout; they are the sound of a complex, global security apparatus working to protect your account, your data, and the very website you're trying to use. It's a small, shared ritual of trust in an automated world. While the experience can be frustrating, and the technology is constantly evolving to be better, its fundamental purpose is noble: to preserve the human element of the internet.
As users, we can advocate for better, more accessible implementations from the services we use. As technology advances, we can look forward to a future where this verification fades into the background, a seamless guardian of our digital lives. Until then, understanding the "why" behind the wait transforms it from an annoyance into a moment of appreciation for the invisible shields that allow us to shop, bank, connect, and create online with a reasonable expectation of safety and authenticity. The internet is a shared space, and these brief pauses are the toll we collectively pay to keep the bots at the gate.