DMARC Quarantine/Reject Policy Not Enabled: Why Your Emails Are Still At Risk
Have you meticulously set up SPF and DKIM records for your domain, believing your email authentication is complete and secure? You might be shocked to learn that this critical half-measure leaves your organization dangerously exposed. The single most common and costly oversight in email security today is having a DMARC quarantine/reject policy not enabled. This means your domain is publishing a DMARC record, but it’s set to p=none—a mode that simply monitors and reports, but takes no action against fraudulent emails. It’s like installing a state-of-the-art alarm system on your building but leaving the front door wide open with a sign that says "Please don't rob me." Cybercriminals aren’t politely complying; they’re exploiting that gap every single day to launch phishing campaigns, business email compromise (BEC) scams, and brand impersonation attacks that erode customer trust and drain finances.
This comprehensive guide will dismantle the myth that p=none is "good enough." We will dive deep into what the quarantine (p=quarantine) and reject (p=reject) policies truly do, the severe risks of leaving them disabled, and provide a clear, actionable roadmap to move from passive monitoring to active enforcement. By the end, you’ll understand exactly why enabling your DMARC policy is not just a technical checkbox, but a fundamental business imperative for protecting your reputation, your customers, and your bottom line.
Understanding DMARC: Beyond SPF and DKIM
Before we can grasp the peril of a missing enforcement policy, we need to understand DMARC’s role in the email authentication trio. Domain-based Message Authentication, Reporting, and Conformance (DMARC) is the policy layer that tells the world’s mail servers what to do with emails that fail SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) checks. SPF verifies that an email comes from an authorized IP address, while DKIM uses cryptographic signatures to prove the email content hasn’t been tampered with and originates from your domain. DMARC unifies these results and publishes your domain’s rulebook.
Think of it this way: SPF and DKIM are the security guards checking IDs at the door. DMARC is the manager who decides whether a person with a fake or missing ID gets turned away (reject), held in a back room (quarantine), or simply logged and allowed in (none). The p=none policy is that manager saying, "Log everything, but don’t you dare stop anyone." It’s invaluable for initial testing and visibility, but it provides zero protection against the very threats it was designed to stop. A DMARC quarantine/reject policy not enabled renders the entire authentication framework toothless against active attacks.
The Three DMARC Policies: None, Quarantine, and Reject
DMARC policies are defined in your domain’s DNS TXT record with the p= tag. Understanding the operational difference between them is crucial.
p=none(Monitor Mode): This is the starting point. Receiving mail servers will accept emails that fail SPF/DKIM, but they will send you aggregate (rua=) and forensic (ruf=) reports detailing the failures. It’s a diagnostic tool, not a security policy. Your domain remains fully spoofable.p=quarantine(Enforcement Mode): This instructs receiving servers to treat failed emails as suspicious. The exact action is at the receiver's discretion, but it typically means the email is delivered to the recipient’s spam/junk folder. It’s a soft block, significantly reducing the visibility of fraudulent emails in the primary inbox.p=reject(Enforcement Mode): This is the strictest and most protective policy. It instructs receiving servers to completely reject any email that fails SPF or DKIM alignment. The email is bounced at the SMTP level and is never delivered to the recipient’s inbox or spam folder. For major providers like Gmail and Outlook, ap=rejectpolicy is a powerful signal that dramatically reduces the chance of your domain being used in phishing attacks.
The High Cost of Inaction: Risks of a Missing Enforcement Policy
So, what’s the real-world impact of having a DMARC quarantine/reject policy not enabled? It’s not a theoretical vulnerability; it’s an active attack surface being exploited right now.
1. Unrestricted Domain Spoofing and Phishing
Without a reject or quarantine policy, there is nothing to stop an attacker from sending an email that appears to be from yourcompany.com to your customers or employees. They can craft incredibly convincing phishing emails that bypass basic user training because the "From" address looks legitimate. According to the 2023 Verizon DBIR, phishing remains one of the top initial attack vectors, and email spoofing is its primary delivery mechanism. Your p=none policy is a green light for these actors.
2. Brand Reputation and Customer Trust Erosion
When your customers receive a fake "password reset" or "invoice" email from your domain and fall victim, who do they blame? They blame your brand. The damage to your reputation is swift and severe. Rebuilding trust after a widespread phishing incident is a long, expensive process involving public relations campaigns and customer support overload. A DMARC quarantine/reject policy not enabled directly facilitates this brand impersonation.
3. Business Email Compromise (BEC) and Financial Loss
BEC attacks, which often involve spoofed emails to finance departments requesting wire transfers, cost businesses billions annually. The FBI’s IC3 reports that BEC scams are among the most financially damaging cybercrimes. A strong DMARC policy (p=quarantine or p=reject) is a critical control that can prevent these fraudulent emails from ever reaching the target’s inbox, stopping the scam before it starts.
4. Poor Email Deliverability for Legitimate Senders
Ironically, a p=none policy can also hurt your legitimate email marketing and transactional campaigns. Major receiving providers like Gmail use DMARC alignment as a positive signal in their spam filtering algorithms. Domains with no enforcement policy are often viewed as less reputable, potentially causing your legitimate newsletters or order confirmations to land in the spam folder. Enforcing DMARC can actually improve deliverability by proving you are a responsible sender.
5. Missing the Forest for the Trees in Your Reports
You might be diligently reviewing your DMARC aggregate reports (those XML files from rua=), seeing thousands of failing sources. But if p=none is set, you’re only an observer. You’re documenting the crime scene without ever calling the police. The reports show you who is failing, but without an enforcement policy, you have no mechanism to stop them. This creates a false sense of security—"we have DMARC"—while the vulnerability remains wide open.
How to Diagnose: Is My DMARC Policy Actually Enforcing?
The first step to solving the problem is confirming it exists. Checking your domain’s DMARC policy is straightforward.
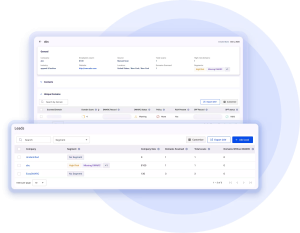
- Use a DMARC Lookup Tool: Websites like MXToolbox, DMARC Analyzer, or Postmark's DMARC Viewer allow you to enter your domain (e.g.,
yourcompany.com) and instantly see your published DMARC record. - Interpret the Record: Look for the
p=tag. If it saysp=none, you have identified the issue. You should also check forsp=(subdomain policy), which can override the organizational policy for subdomains. Asp=noneon a subdomain is equally problematic. - Check for
pct=: Thepct=tag specifies the percentage of emails to which the policy applies. If you seepct=100(or it’s omitted, as 100 is the default), the policy applies to all mail. Apctvalue less than 100 means even withp=quarantineorp=reject, you are only enforcing on a fraction of your mail, leaving a gap. - Examine Your Reports: If you’re already receiving aggregate reports, analyze them. Are you seeing a high volume of failures from sources you don’t recognize or control? This is a clear sign that enforcement is needed to block that unauthorized traffic.
Example of a Non-Enforcing DMARC Record:v=DMARC1; p=none; rua=mailto:dmarc-reports@yourcompany.com;
Example of an Enforcing DMARC Record:v=DMARC1; p=reject; rua=mailto:dmarc-reports@yourcompany.com; ruf=mailto:dmarc-forensics@yourcompany.com; fo=1;
The Path to Enforcement: Safely Implementing Quarantine and Reject
Moving from p=none to p=reject is a journey, not a flip of a switch. A rash transition can break legitimate email flows from unauthenticated sources you rely on (e.g., third-party senders, marketing platforms, or legacy systems). Here is the proven, phased approach.
Phase 1: Achieve Full Visibility and Alignment (Already in p=none)
You must be in this phase first. Use your DMARC reports to identify all legitimate email sources sending on behalf of your domain. This includes:
- Your corporate email server (Microsoft 365, Google Workspace, etc.)
- Transactional email services (SendGrid, Amazon SES, Mailgun)
- Marketing automation platforms (Mailchimp, HubSpot)
- CRM systems (Salesforce)
- Any other service that sends emails using your domain in the
From:header.
For each source, ensure SPF is correctly published (the source’s IPs are included) and DKIM is signing with a selector that aligns with your domain. This is the "alignment" requirement. Fixing these for all legitimate sources is the prerequisite for safe enforcement.
Phase 2: Transition to p=quarantine
Once you have high confidence (e.g., >95%) that your legitimate email sources are passing authentication, change your policy to p=quarantine. This is your safety net. Any email that fails will be sent to spam. Monitor your reports and user feedback for a period of 2-4 weeks.
- Action: Update your DMARC TXT record in DNS from
p=nonetop=quarantine. - Watch For: Are any critical, legitimate emails (e.g., from a new vendor you forgot to onboard) landing in spam? Your reports will show failures. You can then troubleshoot that specific source without a major business disruption.
Phase 3: Move to p=reject for Maximum Protection
After a smooth quarantine period with no significant issues with legitimate mail, you are ready for the gold standard.
- Action: Update your DMARC TXT record from
p=quarantinetop=reject. - Result: Any email failing SPF or DKIM alignment will be silently rejected at the SMTP level by compliant receivers (Gmail, Yahoo, Outlook, etc.). It will never see the light of an inbox.
Crucial Subdomain Policy (sp=) Consideration
Do not forget the sp= tag. If you have active subdomains (e.g., news.yourcompany.com, support.yourcompany.com), you must manage their policy. A common best practice is to set sp=reject alongside your organizational p=reject to ensure subdomains are equally protected. If you have a subdomain you use for testing or a specific purpose that can’t be authenticated yet, you can set a separate, less strict policy for that subdomain only.
Best Practices and Advanced Configurations for Robust Security
Enforcing DMARC is a massive win, but you can optimize further.
- Use
rua=andruf=: Always specify email addresses for aggregate (rua=) and forensic (ruf=) reports. These are your eyes on the battlefield. Use a dedicated mailbox or, better yet, a DMARC reporting service to parse the complex XML reports into actionable dashboards. - Set
fo=for Forensic Reports: Thefo=tag controls forensic report generation.fo=1requests reports for all failures (both SPF and DKIM), giving you the most complete picture for troubleshooting. - Implement BIMI (Brand Indicators for Message Identification): Once you have
p=quarantineorp=rejectin place, you can apply for BIMI. This allows your verified logo to appear in the inbox of supporting clients (like Gmail), turning your authenticated emails into a branded trust signal. BIMI requires a strictp=rejectpolicy and a registered trademark. - Regularly Audit and Update: Your email ecosystem changes. New marketing tools, new employees sending from personal devices, new cloud services. Schedule a quarterly review of your DMARC reports to ensure no new, unauthorized sources have appeared and that all legitimate sources remain compliant.
Frequently Asked Questions (FAQ)
Q: Will enabling p=reject break my email?
A: It will only break email from sources that fail SPF/DKIM alignment. This is precisely the point—it blocks bad email. The phased approach (none -> quarantine -> reject) is designed to identify and fix any legitimate sources before they get blocked. If you follow the preparation steps, legitimate business email will not break.
Q: What about emails forwarded by a recipient?
A: Forwarding is a known challenge for SPF, as the IP address of the forwarder isn’t in your SPF record. However, DKIM is designed to survive forwarding as long as the forwarder doesn’t modify the email body. A p=reject policy will reject emails that fail both SPF and DKIM. Many forwarded emails will fail SPF but pass DKIM, and thus will be accepted. For the small percentage that fail both, the recipient’s forwarder is the problem, not your domain’s policy. The security benefit of rejecting outright spoofed mail far outweighs this minor inconvenience.
Q: Do all receiving mail servers respect DMARC policies?
A: No, not 100%. However, the vast majority of major consumer and business email providers (Google/Gmail, Microsoft/Outlook.com & 365, Yahoo, AOL, Comcast) and many corporate mail systems do enforce DMARC. By setting p=reject, you are protecting your recipients on these massive platforms, which constitute the primary target for phishing campaigns. You are not, and never will be, able to control every mail server on the internet, but you control the policy for your own domain.
Q: My marketing platform says they handle authentication. Do I still need DMARC?
A: Absolutely. Your marketing platform may use its own domain to send emails (e.g., sendgrid.net in the From: address via a "via" or "on behalf of" clause). If you want emails to show your domain in the From: field (which is best for branding and trust), you must configure SPF and DKIM for your domain to include that platform. Then, DMARC will validate that alignment. The platform's own authentication does not cover your domain.
Conclusion: From Passive Observer to Active Defender
The state of DMARC quarantine/reject policy not enabled is the single most significant remaining vulnerability in an otherwise robust email authentication setup. It transforms your domain from a potential target into an open invitation. The statistics are clear: organizations without enforced DMARC are exponentially more likely to be successful targets of phishing and BEC attacks. The journey to p=reject requires diligence—auditing your senders, configuring SPF and DKIM correctly, and using reports intelligently—but it is a well-mapped path.
The era of hoping your customers can spot a fake email is over. The era of proactive, protocol-based defense is here. Enabling your DMARC quarantine or reject policy is the definitive action that shifts your email security from reactive monitoring to active prevention. It’s the final, critical step in claiming ownership of your domain’s reputation and cutting off a primary channel for cybercrime. Take the step today. Audit your policy, clean up your sources, and move to enforcement. Your brand’s integrity and your customers’ safety depend on it.