Stash House Safe Code: What It Is And Why You Should Care
Have you ever wondered what a "stash house safe code" really means? The phrase conjures images from gritty crime dramas—hidden compartments, whispered combinations, and high-stakes secrecy. But beyond the Hollywood glamorization, the concept touches on real-world issues of security, privacy, and legal boundaries. Whether you're a homeowner concerned about valuables, a business owner protecting assets, or simply a curious observer of security culture, understanding the nuances of a stash house safe code is more relevant than you might think. This guide dives deep into the definition, legal implications, security best practices, and cultural footprint of this intriguing term, separating myth from reality.
The term "stash house" historically refers to a location, often a residence or commercial property, used to store illegal goods—drugs, weapons, or stolen merchandise—away from direct association with the owners. The "safe code" is the combination, PIN, or access method securing the physical safe or hidden compartment within that location. In legitimate contexts, it's simply the access credential for a personal or business safe. The intersection of these two ideas creates a powerful cultural shorthand for clandestine operations. However, the principles of securing valuables behind a code are universal and critically important for law-abiding citizens. This article will explore the full spectrum, from the criminal underworld's tactics to the robust security measures every responsible individual should adopt.
The Anatomy of a "Stash House": Definition and Context
What Exactly Is a Stash House?
A stash house is fundamentally a concealment hub. In criminal enterprises, it serves as a buffer between the source of illegal items and their point of distribution. Law enforcement agencies, like the DEA and FBI, routinely dismantle stash houses during operations targeting drug trafficking and weapons rings. These locations are chosen for their perceived normalcy—quiet suburban homes, nondescript apartments, or storage units—to avoid drawing attention. The primary goal is operational security: if one location is compromised, the broader network remains insulated.
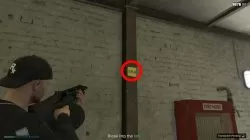
The infrastructure inside can range from a simple, commercially available safe to elaborate, custom-built hideaways behind false walls, under floorboards, or inside appliances. The sophistication often correlates with the value and risk associated with the stored items. A high-level drug cartel might invest in a biometric safe with time-delay locks and anti-tamper mechanisms, while a small-time operator might rely on a basic lockbox. Understanding this spectrum is key to appreciating the security challenges involved.
The "Safe Code" in Criminal vs. Legitimate Use
In a criminal stash house, the safe code is a critical vulnerability. It's a piece of knowledge that, if discovered by rivals or law enforcement, can unravel an entire operation. Codes are often changed frequently, shared on a strict need-to-know basis, and sometimes memorized rather than written down. The human element is the weakest link; betrayal, coercion, or simple carelessness can lead to the code's compromise.
Conversely, in legitimate use—protecting jewelry, important documents, firearms, or cash—the safe code is part of a comprehensive security plan. Here, the goal is not to hide from law enforcement but to protect against burglary, fire, or unauthorized access by family members or guests. The psychology shifts from paranoia to prudent risk management. The code is chosen for memorability by authorized users but difficulty for outsiders to guess, and it's managed with protocols that would be alien in a criminal setting, such as regular audits and documented access logs.
The Blurred Line: When Legitimate Security Gets Questioned
The line between prudent personal security and suspicious activity can sometimes appear blurred to outsiders. A person with an exceptionally secure safe, who is discreet about its contents, might inadvertently raise eyebrows if their behavior aligns with certain stereotypes. This is where situational awareness becomes crucial. Legitimate safe owners should be prepared to explain their security measures calmly if questioned, though they are under no obligation to disclose their combination. The key distinction lies in intent and legality: securing your own property is a right; concealing stolen property is a crime.
The Legal Landscape: Understanding Your Rights and Risks
When Is a "Stash House" Actually Illegal?
The legality hinges entirely on what is being stashed. A safe in your home containing your grandmother's heirlooms, a collection of rare coins, or a handgun you legally own is perfectly lawful. The moment the contents violate federal or state laws—controlled substances, stolen property across state lines, unregistered automatic weapons—the location transforms from a personal vault into a criminal stash house. The safe code itself isn't illegal, but it becomes evidence in a criminal investigation. Law enforcement can obtain a warrant to compel you to disclose a combination if they have probable cause to believe the safe contains evidence of a crime. The Fifth Amendment's protection against self-incrimination has complex applications here, often requiring skilled legal interpretation.
Key Statutes and Potential Charges
Operating or maintaining a stash house can trigger multiple felony charges. Under 21 U.S.C. § 841, possessing a stash house for drug distribution carries severe mandatory minimum sentences. 18 U.S.C. § 922 governs firearms in stash houses, with enhanced penalties for using a safe to conceal weapons from a convicted felon. State laws often have parallel or additional charges, like maintaining a drug house or criminal conspiracy. The presence of a sophisticated safe can even be used by prosecutors to argue "intent to distribute" or "knowledge of illegal activity," aggravating sentencing.
The Homeowner's Legal Safeguards
For the law-abiding citizen, the legal framework is protective. Your Fourth Amendment rights protect you from unreasonable searches. Police generally need a warrant, based on probable cause, to enter your home and access your safe. Never consent to a warrantless search. If served with a warrant, you are typically required to provide the combination. Refusal can lead to a charge of obstruction, but you have the right to consult an attorney first. Documenting the legitimate origin of your valuables (appraisals, receipts, bills of sale) is a powerful proactive measure. This paper trail transforms your safe from a suspicious cache into a verified asset.
Security Best Practices: From Hollywood Fantasy to Real-World Protection
Choosing the Right Safe: It's Not One-Size-Fits-All
The first step in effective security is selecting the appropriate safe. ** burglary-resistant safes** are rated by Underwriters Laboratories (UL) for their ability to withstand forced entry (e.g., UL TL-15, TL-30). Fire-resistant safes protect documents and media from heat. Gun safes must meet specific regulations for firearm storage. For most homeowners, a composite safe offering moderate burglary and fire protection is sufficient. Consider size and placement; a safe that's too large may be impossible to conceal securely, while one that's too small may not hold essential items. Anchor large safes to the floor or wall to prevent removal.
Crafting and Managing a Secure Safe Code
The stash house safe code in a legitimate context should follow these principles:
- Length and Complexity: Use at least 4-6 digits for a dial or keypad lock. Avoid obvious patterns (1234, 0000), birthdays, or years.
- Memorability vs. Guessability: Create a code from a personal mnemonic that isn't publicly known (e.g., the last four digits of a childhood friend's phone number, not your own).
- Exclusive Knowledge: Only authorized users should know the code. Never write it on or near the safe, or store it in a desk drawer.
- Regular Rotation: Change the code annually or when an authorized user no longer needs access (e.g., after a roommate moves out).
- Access Logging: For high-security needs, consider a safe with an audit trail that records every access attempt with date and time.
Layered Security: The Safe is Just One Layer
Relying solely on a safe is a mistake. Implement defense-in-depth:
- Physical Concealment: Hide the safe itself. Place it in a closet, behind a false wall, under a secure floorboard, or inside a locked cabinet. The harder it is to find, the better.
- Alarm Systems: Connect your safe's location to a monitored alarm system with sensors on doors, windows, and motion detectors.
- Surveillance: Install visible security cameras (dummy cameras can also deter) covering the safe's location and entry points.
- Environmental Controls: Ensure the safe is in a location with low humidity to prevent rust and damage to contents.
- Discretion: Do not discuss your safe, its contents, or its location with anyone outside your trusted circle. OPSEC (Operational Security) is not just for spies.
Pop Culture and Misconceptions: The "Stash House" in Media
How Movies and TV Shows Distort Reality
Films like The Town, Heat, and TV series like Breaking Bad have glamorized and sensationalized the stash house concept. They often depict:
- Impossibly Complex Hides: Secret rooms activated by pulling a specific book or pressing a hidden panel. While such custom concealments exist, they are expensive and often less reliable than a high-quality safe.
- Instant Code Cracking: Characters effortlessly guess or brute-force combinations. In reality, modern safes have lockout features after a few incorrect attempts, and manipulation-resistant locks are standard.
- The "One Big Score": The entire plot revolves around one stash house. Real criminal operations use distributed risk, with multiple smaller stash locations to avoid total loss from a single bust.
- Clean Getaways: Burglars walk in and out with the safe. In truth, a properly anchored, high-rated safe requires heavy machinery and significant time to remove, creating a huge noise signature that attracts attention.
The Realities of Law Enforcement Tactics
Contrary to the "silent alarm" trope, real police raids on suspected stash houses are high-risk, dynamic entries. They use no-knock warrants based on credible intelligence about imminent destruction of evidence or danger. Tactical teams employ breaching tools (shotguns, battering rams), flashbang grenades, and overwhelming force to secure the scene. Their first targets are often the bedrooms and likely hiding spots for occupants, followed by a systematic search for contraband. They have advanced tools like borescopes to peer into safes and hydraulic door openers. The cinematic "standoff" over a safe is rare; the safe is usually documented, seized, and opened later under controlled conditions at a evidence facility.
The Unintended Consequences of Glamorization
This media portrayal has a dual negative effect. For criminals, it creates a false sense of sophistication and invincibility, leading to overconfidence and sloppy operational security. For the public, it can breed either irrational fear of "hidden dangers" or a dangerous underestimation of real security needs. It also complicates the work of legitimate security professionals, who must constantly dispel myths when advising clients. The reality is far less cinematic but far more critical: security is a boring, consistent process of good habits, quality hardware, and layered protocols, not a dramatic one-time event.
Ethical and Social Considerations: Beyond the Lock and Key
The Moral Weight of Secrecy
The concept of a stash house safe code inherently involves secrecy. For legitimate owners, this is a responsible choice to protect assets from those who would misuse them. However, secrecy can also enable abuse. In domestic violence situations, an abusive partner might use a safe to control finances or hide assets. In elder fraud, scammers may coerce seniors into revealing safe combinations. Recognizing these potential ethical pitfalls is part of responsible ownership. Having a trusted confidant (a spouse, adult child, or attorney) who knows the code and can intervene in cases of incapacity or duress is a wise, albeit sensitive, consideration.
The Community Impact of Illicit Stash Houses
Real stash houses for illegal goods are not victimless. They are nodes in networks that fuel addiction, violence, and community decay. A stash house dealing in fentanyl-laced pills directly contributes to the overdose epidemic. A weapons stash house increases the risk of gun violence in surrounding neighborhoods. The associated criminal activity—turf wars, robberies, and police activity—creates an environment of fear and instability. Even the property itself can become a blight, with neglected maintenance and constant suspicious traffic lowering property values for neighbors. Understanding this chain of harm underscores why society criminalizes the operation of such places.
Responsible Disclosure and Reporting
What should you do if you suspect a neighbor is operating a stash house? Do not investigate yourself. Confrontation is extremely dangerous. Instead, gather only objective facts: specific dates/times of unusual activity (excessive short-term visitors at odd hours, strong chemical odors, constant heavy traffic), descriptions of vehicles, and license plate numbers if visible from public space. Report your suspicions anonymously to local police non-emergency lines or national tip lines like the DEA's. Provide your observations factually, without speculation. Your vigilance can prevent violence and trafficking in your community, but your personal safety must be the priority.
Conclusion: Securing Your World, Decoding the Myth
The phrase "stash house safe code" is a cultural Rorschach test. To some, it's a thrilling trope of crime fiction. To law enforcement, it's a critical piece of evidence. To a security professional, it's a fundamental component of asset protection. To a concerned citizen, it might be a worrying sign of illicit activity. This article has aimed to decode the myth and present the reality.
For the law-abiding individual, the takeaway is clear and empowering: The principles of securing valuables are universal and essential. Invest in a safe appropriate for your needs, choose and manage your combination with care, and integrate the safe into a layered security system. Understand your legal rights and responsibilities. Maintain discretion not out of criminal intent, but out of prudent self-protection. By doing so, you transform the Hollywood notion of a "stash house safe code" into a mundane but powerful tool of responsible ownership and personal security.
Ultimately, the code you choose is less about hiding from the world and more about asserting control over your own assets and peace of mind. In a world of digital breaches and physical threats, that control is not just valuable—it's indispensable. Secure your code, secure your peace, and contribute to a safer community by using security knowledge responsibly.