You Require Permission From TrustedInstaller: Decoding Windows' Most Frustrating Error
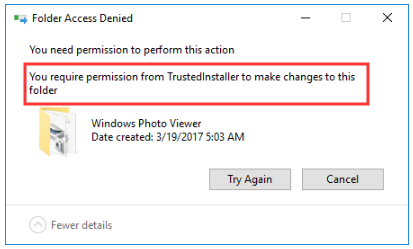
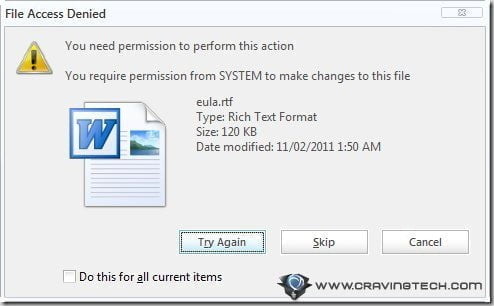
Have you ever been stopped dead in your tracks by a cryptic Windows message declaring, "You require permission from TrustedInstaller"? You’re trying to modify, delete, or rename a system file you know is on your own computer, but Windows treats it like a classified government document. It’s a moment of pure digital frustration—your admin account feels powerless, and that simple task suddenly requires a secret handshake. This isn't just a minor inconvenience; it's a fundamental security barrier designed by Microsoft to protect the core of your operating system. Understanding this message is the first step to safely managing your Windows PC, whether you're a curious tinkerer, a developer, or someone just trying to clean up their system. This guide will transform that frustrating error into a clear understanding of Windows security, providing you with the knowledge and safe methods to handle it.
What Exactly is TrustedInstaller? The Ghost in Your Machine
Before we can solve the permission problem, we must understand the gatekeeper. TrustedInstaller is not a user account in the traditional sense. It is a special, built-in security principal and service in Windows, formally known as the Windows Modules Installer service. Its primary job is to own and protect core system files, folders, and critical Windows components. Think of it as the ultimate, unbypassable system administrator that even your own admin account must answer to.
The Role of TrustedInstaller in Windows Security
Microsoft created TrustedInstaller as a key part of Windows Resource Protection (WRP), a feature introduced with Windows Vista. WRP's mission is to prevent accidental or malicious modification of essential system files, DLLs, and registry keys. By placing these files under the ownership of TrustedInstaller, Microsoft ensures that only the Windows Update service, the installer service itself, or a process running with TrustedInstaller's privileges can make changes. This design dramatically reduces the risk of a rogue program or a user accidentally corrupting the OS, which would lead to crashes, instability, and the infamous "Blue Screen of Death."
Why Your Admin Account Isn't Enough
Even if you are logged in with the built-in "Administrator" account or an account in the local Administrators group, you do not automatically have permission to touch TrustedInstaller-owned files. This is a deliberate security layer. The "User Account Control (UAC)" prompt you sometimes see is a related but different mechanism. UAC asks for consent to run a program with elevated privileges. The TrustedInstaller permission error is a hard stop—your current security token simply doesn't have the necessary access rights (specifically, the WRITE_DAC and WRITE_OWNER permissions) to the file's Access Control List (ACL). The system is telling you that the owner (TrustedInstaller) must explicitly grant you access, which it won't do for routine operations.
The Anatomy of the Error: When and Why It Strikes
You'll typically encounter the "You require permission from TrustedInstaller" error in specific, predictable scenarios. Recognizing these situations helps you assess the risk before attempting a fix.
Common Triggers for the Permission Denied Message
- Manual File Operations: Trying to delete, rename, move, or modify a file in protected directories like
C:\Windows\,C:\Program Files\, orC:\System32\. - Third-Party Software Installers/Uninstallers: Some older or poorly coded programs attempt to modify shared system DLLs or install services in protected locations.
- Manual Registry Edits: Accessing certain keys under
HKEY_LOCAL_MACHINE\SYSTEMorHKEY_LOCAL_MACHINE\SOFTWAREthat are owned by TrustedInstaller. - System Cleanup Tools: Aggressive disk cleaners or "optimizers" that try to remove what they perceive as unnecessary system files.
- Game Modding or Software Cracking: This is a very common source. Modifying game executable files in
Program Filesor applying cracks often hits this barrier.
The Real Risk: Why Microsoft Built This Wall
The statistic is telling: according to Microsoft's own data, system file corruption is a leading cause of Windows startup failures and performance degradation. The TrustedInstaller barrier exists to protect against:
- Accidental Deletion: A user mistaking a critical
.dllfor a junk file. - Malware Persistence: Viruses that try to replace system files to embed themselves.
- Software Conflicts: One application overwriting a shared system component that another application depends on, causing a cascade of failures.
- Windows Update Integrity: Ensuring that only the official Windows Update mechanism can patch system files, maintaining a consistent and secure OS state.
How to Safely Gain Permission: Your Step-by-Step Guide
Now for the practical part. The cardinal rule: Do not disable TrustedInstaller or take ownership of the entire C:\Windows folder. That is like removing the firewall from your house. Instead, we use precise, surgical methods for the specific file or folder causing the issue.
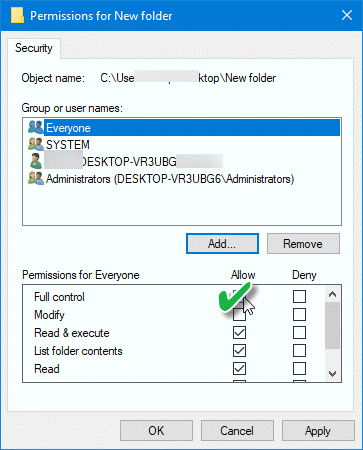
Method 1: The Graphical (File Explorer) Approach
This is the most user-friendly method for one-off file operations.
- Right-click the problematic file or folder and select Properties.
- Navigate to the Security tab. Click Advanced.
- Next to the "Owner:" label, you'll see "TrustedInstaller." Click Change.
- In the "Select User or Group" window, type your user account name (e.g.,
YourPCName\YourUsername) and click Check Names, then OK. - Crucially, check the box that says "Replace owner on subcontainers and objects" if you need to modify a folder's contents. Click Apply and OK.
- Back in the Advanced Security Settings window, select your user account from the list and click Edit to change permissions.
- Grant yourself at least "Full control" and click Apply. You will now be able to modify the file.
⚠️ Critical Warning: After you're done, it is highly recommended to revert the ownership back to TrustedInstaller for system files. You can do this by repeating the steps and changing the owner back to
NT SERVICE\TrustedInstaller. Leaving system files owned by your user account creates a permanent security vulnerability and can break Windows Update.
Method 2: The Power User (Command Line) Approach
For advanced users or batch operations, takeown and icacls are powerful tools. Open Command Prompt or PowerShell as Administrator.
- To take ownership of a file:
takeown /f "C:\Path\To\File.txt" - To grant full control permissions to your admin group:
icacls "C:\Path\To\File.txt" /grant Administrators:F - To recursively take ownership of a folder and all its contents:
takeown /f "C:\Path\To\Folder" /r /d y - To reset permissions to default (often restoring TrustedInstaller ownership):
icacls "C:\Path\To\Folder" /reset /t /c
Remember: The /r (recursive) and /t (tree) flags are powerful. Double-check your path. A typo could apply these commands to the wrong directory.
Method 3: The "Just Let Me Do It" Shortcut (Not Recommended)
Some guides suggest disabling the Windows Modules Installer service (TrustedInstaller). Do not do this. This service is critical for installing Windows Updates, service packs, and optional Windows features. Disabling it will break your ability to keep your system secure and functional. The goal is controlled access, not removing the guard.
Best Practices: Working with Protected Files Without Breaking Windows
Gaining permission is one thing; using that power responsibly is another. Follow these principles to avoid a system repair nightmare.
- The Principle of Least Privilege: Only take ownership and grant permissions for the single, specific file you need. Never take ownership of
C:\WindowsorC:\Program Files. If a program installer is failing, try running it as Administrator (right-click > Run as administrator) first—this often provides the necessary elevation without touching file ownership. - Always Revert Ownership: After modifying a genuine system file, change the owner back to
NT SERVICE\TrustedInstaller. Use the same Advanced Security Settings window. This restores the default security posture. - Verify the File's Importance: Before modifying any system file, search online for its exact name and purpose. Is it
ntoskrnl.exe(the Windows kernel)?winlogon.exe? Modifying these will render your system unbootable. If you're unsure, assume it's critical and leave it alone. - Create a System Restore Point First: Before making any changes to system files or permissions, create a manual System Restore point. This is your "undo" button if something goes wrong. Search for "Create a restore point" in the Start menu to access the System Properties dialog.
- Consider Alternative Solutions: Often, the need to modify a system file arises from a specific problem. For example:
- Can't delete a stubborn file? Boot into Safe Mode and try again.
- Need to edit a protected config file? Copy it to your desktop, edit it, then copy it back (you'll be prompted for admin permission, which is usually sufficient).
- Game modding? Many modern games on Steam support a "beta" or "mods" folder outside of
Program Files. Research community-supported modding methods for your specific game.
Advanced Scenarios and Troubleshooting
Sometimes, the problem is more complex than a simple permission error on one file.
"Access Denied" Even After Taking Ownership
If you've taken ownership and granted permissions but still get "Access Denied," check for:
- Inheritance: The folder might have permissions inherited from a parent folder that is still blocking you. In the Advanced Security Settings, you can disable inheritance and copy the existing permissions before making changes.
- File in Use: The file is locked by a running process. Use a tool like Process Explorer (from Microsoft's Sysinternals suite) to search for which process has a handle on the file and close it.
- Encrypting File System (EFS): The file might be encrypted. You would need the original encryption certificate to access it.
TrustedInstaller and Windows Update Failures
Paradoxically, if the TrustedInstaller service itself is disabled or corrupted, Windows Update will fail. You might see error codes like 0x80070005 (Access Denied). The fix is to ensure the Windows Modules Installer service is set to Manual (Trigger Start) and is running. You can check this via services.msc.
The Nuclear Option: In-Place Repair Install
If you've messed up system file permissions extensively and your Windows installation is unstable, the safest recovery is an in-place upgrade/repair install. This uses the Windows installation media to reinstall Windows while keeping your personal files, apps, and settings. It will restore all default system file permissions and ownership. This is a more reliable fix than a clean install for permission-related corruption.
Conclusion: Knowledge is the Key to Control
The message "You require permission from TrustedInstaller" is not a bug; it is a feature. It is the digital equivalent of a "Do Not Disturb" sign on the server room door of your operating system. While it can be a hurdle for power users and developers, its purpose is noble: to preserve the integrity and security of your Windows installation.
The power you now hold—the knowledge of how to safely take ownership and adjust permissions—comes with a corresponding responsibility. Always ask yourself: "Should this file be protected?" If the answer is yes (and for anything in C:\Windows\System32, it almost certainly is), make your change, then meticulously restore the original TrustedInstaller ownership. Treat your system's core files with the respect they're designed to demand. By doing so, you maintain the delicate balance between user control and system stability, ensuring your Windows PC remains both powerful and secure for years to come. The next time that error appears, you won't see a barrier—you'll see a well-designed security protocol, and you'll know exactly how to respectfully ask for a temporary pass.