Ari Kytsya & Girthmaster Leak: Digital Privacy, Consequences, And What You Need To Know
What happens when a private moment becomes a public spectacle overnight? The phrase "ari kytsya girthmaster leaked" entered the digital lexicon not as a planned marketing campaign, but as a stark reminder of the fragile boundary between personal life and public consumption in the age of the internet. For those unfamiliar, the incident centered on private content involving Ari Kytsya, a prominent figure in the online fitness and bodybuilding community, and a figure known as "Girthmaster," allegedly being shared without consent. This event ignited fierce debates about consent, platform security, and the very real human cost of digital leaks. This article delves deep into the incident, unpacks the biography of those involved, explores the technical and legal landscapes of such breaches, and provides actionable insights for anyone navigating the digital world.
Understanding the Incident: More Than Just a Leak
Before dissecting the fallout, it's crucial to understand the core event. The term "ari kytsya girthmaster leaked" refers to the unauthorized distribution of explicit, private media. Such leaks are not mere gossip; they are violations of privacy with potentially devastating consequences. The speed at which such content spreads across social media platforms, forums, and file-sharing sites is staggering, often making containment impossible. This specific case gained traction due to the involved parties' public profiles, transforming a personal violation into a widely discussed topic.
The Anatomy of a Digital Leak: How It Happens
Digital leaks typically occur through several vectors:
- Compromised Accounts: Weak passwords, phishing scams, or data breaches from other services can give hackers access to private cloud storage or messaging apps.
- Malicious Insiders: Someone with legitimate access, like a former partner or disgruntled associate, intentionally shares private content.
- Device Theft or Loss: An unencrypted phone or laptop falling into the wrong hands.
- Exploiting Platform Vulnerabilities: Rarely, security flaws in apps or services can be exploited to access private data.
In the case of high-profile individuals like Ari Kytsya, the motive often blends personal vendetta, a desire for notoriety, or financial gain through extortion or selling the content to shady websites. The aftermath is a chaotic race against time as victims attempt to issue takedown notices under laws like the DMCA (Digital Millennium Copyright Act) in the U.S., while the content proliferates exponentially.
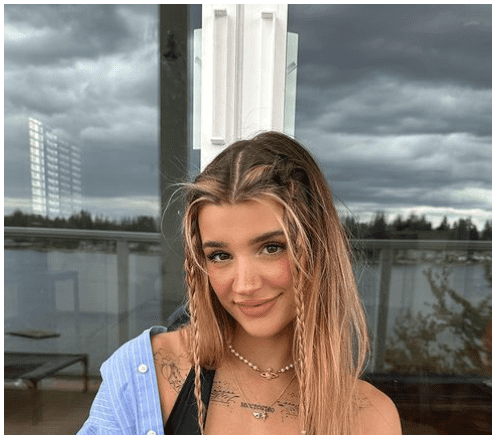
Who is Ari Kytsya? A Look at the Influencer at the Center
To understand the impact, one must first understand the person. Ari Kytsya is not a passive subject of the leak; she is an established entrepreneur and influencer in the fitness industry. Her brand is built on discipline, physical transformation, and motivational content.
Biographical Profile & Personal Data
| Attribute | Details |
|---|---|
| Full Name | Ari Kytsya |
| Primary Profession | Fitness Model, Entrepreneur, Social Media Influencer |
| Known For | Bodybuilding, fitness coaching, online presence on Instagram and YouTube |
| Online Persona | Promotes strength training, personal development, and a disciplined lifestyle. |
| Estimated Following | Hundreds of thousands to millions across platforms (exact figures fluctuate). |
| Business Ventures | Often includes fitness programs, merchandise, and brand sponsorships. |
| Public Stance | Typically projects an image of control, empowerment, and physical prowess. |
This public persona makes the private leak particularly jarring for her audience. It creates a dissonance between the controlled, powerful image she projects and the vulnerability exposed by the leak. Her biography is a testament to building a personal brand—a brand that a leak of this nature directly threatens by undermining the curated narrative of control and strength.
The Human and Professional Cost of a Leak
The consequences of such an incident extend far beyond initial embarrassment. They represent a profound attack on personal autonomy and professional livelihood.
Psychological and Emotional Toll
Victims of non-consensual pornography, often termed "image-based sexual abuse," report severe psychological distress. This can include:
- Anxiety and Depression: Constant fear of being recognized or judged.
- Post-Traumatic Stress: Symptoms akin to PTSD, including hypervigilance and flashbacks.
- Social Withdrawal: Isolating oneself to avoid potential encounters with the content or judgmental looks.
- Loss of Trust: Erosion of trust in relationships and digital platforms.
For an influencer like Kytsya, whose career relies on public engagement, this can trigger a crisis of identity and purpose. The very platform that built her career becomes the vector for her trauma.
Professional and Financial Repercussions
The professional damage is multifaceted:
- Brand Devaluation: Sponsors and business partners may distance themselves to avoid association with controversy, regardless of the victim's innocence.
- Loss of Revenue: A diminished following or demonetization of content directly impacts income streams from ads, sponsorships, and direct sales.
- Reputation Management Costs: Legal fees, PR crisis management, and digital forensics to track the leak's spread are prohibitively expensive.
- Long-Term Career Shadow: The incident can become an indelible part of one's digital footprint, resurfacing years later and hindering future opportunities.
Navigating the Legal Landscape: Rights and Remedies
The legal response to such leaks is a critical battleground. Laws are evolving but vary dramatically by jurisdiction.
Key Legal Frameworks
- Copyright Law: The victim typically holds the copyright to their own images. A DMCA takedown notice can be issued to websites hosting the content, demanding its removal. However, this is a reactive, whack-a-mole process.
- Criminal Laws: Many countries and U.S. states now have specific "revenge porn" or non-consensual pornography laws. These can carry significant penalties, including fines and imprisonment. The key is proving the content was shared without consent and with intent to harm or for sexual gratification.
- Civil Lawsuits: Victims can sue for invasion of privacy, intentional infliction of emotional distress, and defamation (if false statements accompany the leak). These suits can result in monetary damages but are lengthy and costly.
- Platform Policies: Major social media platforms (Meta, Twitter/X, TikTok) have policies against non-consensual intimate imagery. Reporting through these channels can lead to content removal and account bans for the perpetrator, but enforcement is inconsistent.
For someone in Kytsya's position, leveraging all these avenues simultaneously is often necessary. The legal process, however, is rarely swift, prolonging the period of distress and uncertainty.
The Role of the "Girthmaster" Persona and Online Subcultures
The inclusion of "Girthmaster" in the keyword points to a specific online subculture, often associated with bodybuilding, fetish communities, or adult content creators. This context is important for understanding the leak's propagation path.
Niche Communities and Rapid Dissemination
Content within these niche, often insular communities spreads with alarming speed and dedication. Forums, dedicated subreddits, Telegram channels, and specialized websites act as echo chambers and distribution hubs. The leak's association with a known persona like "Girthmaster" likely gave it initial traction within these circles before it bled into mainstream social media discourse. Understanding these ecosystems is key to comprehending how a private leak achieves viral status. The anonymity and lack of moderation in many of these spaces make them particularly hostile environments for victims seeking redress.
Protecting Yourself in the Digital Age: Proactive Strategies
While no one can be 100% immune, a layered approach to digital hygiene significantly reduces risk.
Essential Security Practices
- Password Hygiene: Use strong, unique passwords for every account. A password manager is non-negotiable.
- Enable Two-Factor Authentication (2FA): Use an authenticator app (like Google Authenticator or Authy) instead of SMS-based 2FA where possible, as SIM-swapping is a common attack vector.
- Encrypt Everything: Ensure your devices (phone, laptop) have full-disk encryption enabled. Use encrypted messaging apps (Signal, WhatsApp with end-to-end encryption) for sensitive conversations.
- Cloud Storage Caution: Be acutely aware of what you store in cloud services (iCloud, Google Photos, Dropbox). Review privacy settings meticulously. Assume anything digital could be compromised.
- Phishing Awareness: Never click suspicious links or download attachments from unknown senders. Verify requests for login details directly with the service.
Mindful Sharing and Digital Legacy
- The "Grandma Rule": If you wouldn't want your grandmother to see it, don't create or store it digitally.
- Audit Your Digital Footprint: Regularly search your name online. Use tools to request removal of old, unwanted content from search engines.
- Understand Platform Permanence: Even "deleted" content can be cached, screenshotted, or archived by third parties. Treat digital sharing as potentially permanent.
The Broader Societal Conversation: Consent and Ethics Online
Incidents like the "ari kytsya girthmaster leaked" search trend are symptomatic of a larger cultural failing. They force us to confront uncomfortable questions:
Why Does This Content Spread?
- Morbid Curiosity: The "forbidden fruit" effect drives clicks and searches.
- Victim Blaming Culture: A pervasive tendency to question the victim's actions ("Why did she take the photo?") rather than condemn the theft and distribution.
- Lack of Digital Empathy: The physical and emotional distance of the internet desensitizes people to the real harm caused by sharing such content.
- Monetization of Leaks: Some websites profit directly from hosting and advertising on pages with leaked content, creating a financial incentive for the cycle to continue.
Shifting this culture requires education on digital consent, holding platforms accountable for enabling distribution, and supporting victims instead of shaming them.
What to Do If You Are a Victim: A Practical Action Plan
If you find yourself the victim of a leak, immediate and organized action is critical.
- Document Everything: Take screenshots and URLs of where the content appears. Note dates and times. This is evidence for legal and platform reports.
- Report to Platforms: Use the official reporting tools on every site where the content appears. Be explicit: it is non-consensual intimate imagery. Cite relevant platform policies.
- Contact a Lawyer: Consult with an attorney specializing in privacy law or cybercrime immediately. They can guide you on cease-and-desist letters, law enforcement reports, and civil suits.
- Alert Law Enforcement: File a report with your local police. Provide all documentation. In the U.S., the FBI's Internet Crime Complaint Center (IC3) is also a resource for cross-state crimes.
- Secure Your Accounts: Immediately change all passwords, review active sessions on all accounts, and enable 2FA everywhere.
- Seek Support: Contact organizations like the Cyber Civil Rights Initiative or the National Center for Victims of Crime. They offer resources and advocacy. Do not isolate yourself; seek mental health support.
Conclusion: Beyond the Scandal
The "ari kytsya girthmaster leaked" phenomenon is far more than a salacious search trend or a celebrity scandal. It is a case study in digital vulnerability, the long arm of the internet, and the enduring importance of consent. It highlights the precarious position of public figures whose personal lives are commodified without their permission. While the specific details of this leak may fade from headlines, the underlying issues—weak platform security, inadequate legal recourse in many areas, and a culture that too often consumes rather than condemns such violations—persist.
The ultimate takeaway is a call for heightened personal digital responsibility and a collective push for stronger ethical and legal standards online. For individuals, it means treating personal data with the same care as physical safety. For society, it means supporting victims, demanding accountability from tech companies, and educating ourselves and others on the profound, real-world harm caused by treating private moments as public content. The goal is not just to navigate leaks like this one, but to build a digital environment where such violations become not just difficult, but socially and technologically obsolete.